The Forescout Certified Professional Exam (FSCP)
Passing Forescout Forescout Certified Professional exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard FSCP Dumps
In 2026, Forescout uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Forescout FSCP Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
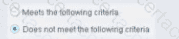
When configuring policy conditions, which of the statements is true regarding this image?
Select one:
Correct Answer & Rationale:
Answer: A
Explanation:
Based on the policy condition image showing "Does not meet the following criteria", the correct statement is that it negates the criteria as part of the property.
Understanding "Does not meet the following criteria":
According to the Forescout Administration Guide:
The "Does not meet the following criteria" radio button option in policy conditions creates a logical negation of the condition:
"Meets the following criteria" - Endpoint matches if the condition is true
"Does not meet the following criteria" - Endpoint matches if the condition is FALSE (negated)
How the Negation Works:
According to the documentation:
"Use the AND value between both properties: Windows > Manageable Domain > Does not meet the following criteria"
This syntax shows that "Does not meet the following criteria" negates the entire criteria evaluation:
Normal condition: "Windows Antivirus Running = True"
Result: Matches endpoints WITH antivirus running
Negated condition: "Windows Antivirus Running Does not meet the following criteria (= True)"
Result: Matches endpoints WITHOUT antivirus running (negates the criteria)
Negation Happens at Property Level:
The negation is applied as part of the property evaluation, not as a separate NOT operator. When you select "Does not meet the following criteria":
The condition is evaluated normally
The result is then negated/inverted
The endpoint matches only if the negated result is true
Why Other Options Are Incorrect:
B. Modifies the irresolvable condition to TRUE - "Does not meet the following criteria" doesn't specifically affect irresolvable property handling
C. Generates a NOT condition in the sub-rule condition - The negation is part of this property's evaluation, not a separate sub-rule NOT condition
D. Irresolvable hosts would match the condition - "Does not meet the following criteria" doesn't specifically target irresolvable hosts
E. Modifies the evaluate irresolvable condition to FALSE - This setting doesn't affect the "Evaluate irresolvable as" setting
Referenced Documentation:
Forescout Administration Guide v8.3
Forescout Administration Guide v8.4
ForeScout CounterACT Administration Guide - Policy Conditions section
Manage Actions documentation
QUESTION DESCRIPTION:
Which CLI command gathers historical statistics from the appliance and outputs the information to a single *.csv file for processing and analysis?
Correct Answer & Rationale:
Answer: E
Explanation:
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
The fstool sysinfo stats command is the correct CLI command used in Forescout platforms to gather and export historical statistics from the appliance to a single CSV file for processing and analysis.
According to the Forescout CLI Commands Reference Guide (versions 8.1.x through 8.5.3), the fstool sysinfo command is listed under the Machine Administration category of fstool commands. The command's primary purpose is to "View Extensive System Information about the Appliance".
When used with the stats parameter, the command fstool sysinfo stats specifically:
Gathers historical statistics - The command collects comprehensive time-series data and historical statistics from the Forescout appliance
Outputs to a CSV file - The information is exported to a * single .csv file format , making it suitable for import into spreadsheet applications and data analysis tools
Enables processing and analysis - The CSV format allows administrators and engineers to perform offline analysis, trend analysis, and detailed troubleshooting
Why Other Options Are Incorrect:
fstool tech-support - This command is used to send logs and diagnostic information to Forescout Customer Support, not to output appliance statistics
fstool appstats - This command is not documented in any official Forescout CLI reference guides
fstool va stats - This command variant is not a recognized fstool command in Forescout documentation
fstool stats - This standalone command variant is not a recognized fstool command in Forescout documentation
Referenced Documentation:
Forescout CLI Commands Reference Guide v8.1.x, 8.2.x, 8.4.x, 8.5.2, and 8.5.3
Forescout Administration Guide v8.3 and v8.4
Machine Administration fstool Commands section - Forescout Official Documentation Portal
QUESTION DESCRIPTION:
Which of the following best describes why PXE boot endpoints should be exempt from Assessment policies?
Correct Answer & Rationale:
Answer: C
Explanation:
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
PXE (Preboot Execution Environment) boot endpoints should be exempt from Assessment policies because they are not yet manageable and may not have all the required software and services installed. According to the Forescout Administration Guide, endpoints in the early stages of deployment, such as those booting via PXE, are temporary in nature and lack the necessary management capabilities and required software components.
PXE Boot Endpoints Characteristics:
PXE boot endpoints represent machines in a temporary state during the deployment process:
Not Yet Fully Deployed - PXE boot is used during initial OS installation and deployment
Lack Required Services - The endpoint does not yet have installed:
SecureConnector (if required for management)
Endpoint agents
Required security software
Management services
Limited Configuration - The endpoint may not have completed network configuration
Temporary State - PXE boot endpoints are in a transient state, not their final operational state
Policy Endpoint Exceptions:
According to the documentation, administrators can "select endpoints in the Detections pane and exempt them from further inspection for the policy that detected them". This is particularly important for PXE boot endpoints because:
False Positives - Assessment policies might flag PXE boot endpoints as non-compliant due to missing software that hasn't been installed yet
Blocked Deployment - If blocking actions are applied, they could interfere with the deployment process
Temporary Assessment - Once the endpoint is fully deployed and manageable, it can be added back to Assessment policies
Operational Efficiency - Exempting PXE boot endpoints prevents unnecessary policy violations during the deployment window
Manageable vs. Unmanageable Endpoints:
According to the documentation:
"Endpoints are generally unmanageable if their remote registry and file system cannot be accessed by Forescout. Unmanageable hosts can be included in your policy."
PXE boot endpoints specifically fall into this category because:
Remote management is not yet available
Required agents are not installed
File system access is not established
Why Other Options Are Incorrect:
A. Because they will not be subject to the Acceptable Use Policy - Not the primary reason; Assessment policies differ from Acceptable Use policies
B. They have already been deployed and should immediately be subject to Assessment policies - Contradicts the purpose; PXE boot endpoints are NOT yet deployed
D. Because they will never be manageable or have the required software and services - Incorrect; once deployed, they WILL become manageable
E. Because they are special endpoints playing a specific role in the network - While true in context, this doesn't explain why they need exemption
Referenced Documentation:
Forescout Administration Guide - Create Policy Endpoint Exceptions
Restricting Endpoint Inspection documentation
Manage Actions - Unmanageable hosts section
QUESTION DESCRIPTION:
What Protocol does CounterACT use to verify the revocation status of certificates?
Correct Answer & Rationale:
Answer: B
Explanation:
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
According to the Forescout Platform Administration Guide and Certificate Configuration documentation, Forescout uses the Online Certificate Status Protocol (OCSP) to verify the revocation status of certificates.
OCSP in Forescout:
According to the official Forescout documentation:
"You can also configure the use of Online Certificate Status Protocol (OCSP) and set up validation method failover between CRL and OCSP."
And further:
"The Forescout Platform supports certificate revocation lists (CRL) and Online Certificate Status Protocol (OCSP) for smart card authentication."
What OCSP Does:
According to the Wikipedia and Fortinet OCSP documentation:
"The Online Certificate Status Protocol (OCSP) is an Internet protocol used for obtaining the revocation status of an X.509 digital certificate."
OCSP provides:
Real-Time Status Verification - Checks current certificate revocation status
Request/Response Protocol - Sends a query to an OCSP responder
Revocation Status Response - Returns "good," "revoked," or "unknown"
Efficient Alternative to CRL - Smaller data payload than downloading full certificate revocation lists
How OCSP Works:
According to the OCSP documentation:
Request Sent - Client sends OCSP request to OCSP responder (server operated by CA)
Status Verification - Responder checks revocation status with trusted CA
Response Returned - Responder returns current status, revoked, or unknown
Decision Made - Application (like Forescout) accepts or rejects the certificate based on response
Forescout Smart Card Certificate Validation:
According to the Forescout documentation:
When using smart card authentication, Forescout:
Supports OCSP - Sends OCSP requests for certificate revocation status
Supports CRL - Also supports Certificate Revocation Lists as fallback
Failover Configuration - Can be configured to use OCSP with CRL fallback
OCSP vs. Certificate Revocation List (CRL):
According to the documentation:
Aspect
OCSP
CRL
Data Size
Smaller response
Larger list
Update Frequency
Real-time status
Periodic updates
Network Load
Lower burden
Higher burden
Timeliness
Current status
Potentially outdated
Processing
Less complex
More complex parsing
Forescout uses OCSP because it provides real-time, efficient certificate status verification.
Why Other Options Are Incorrect:
A. PKI Certificate Revocation Protocol (PCRP) - This is not a standard protocol; PCRP does not exist
C. Online Revocation Status Protocol (ORSP) - This is not the correct name; the protocol is OCSP, not ORSP
D. Certificate Revocation List Protocol (CRLP) - While Forescout supports CRL, the primary protocol for real-time status is OCSP
E. Certificate Revocation Protocol (CRP) - This is not a standard protocol; the correct protocol is OCSP
Referenced Documentation:
Smart Card Certificate Configuration for Forescout Platform
Using Forescout Platform Smart Card Authentication
Client-Server Connection documentation
Audit Actions - OCSP for Syslog validation
Online Certificate Status Protocol (OCSP) - Wikipedia
What Is Online Certificate Status Protocol (OCSP) - Fortinet
QUESTION DESCRIPTION:
Which two of the following are main uses of the User Directory plugin? (Choose Two)
Correct Answer & Rationale:
Answer: A, D
Explanation:
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
According to the Forescout User Directory Plugin documentation, the two main uses of the User Directory plugin are: Verify authentication credentials (A) and Query user details (D).
Main Functions of User Directory Plugin:
According to the official documentation:
"The User Directory plugin resolves endpoint user details and performs user authentication via configured internal and external directory servers."
The plugin's two primary functions are:
Authenticate Users - Verify/validate authentication credentials
Resolve User Information - Query and retrieve user details from directory servers
Verifying Authentication Credentials:
According to the documentation:
The User Directory plugin:
Validates user credentials against configured directory servers (Active Directory, LDAP, etc.)
Performs authentication for:
Endpoint user authentication
Console login authentication
Guest user registration
RADIUS authentication
Querying User Details:
According to the documentation:
The User Directory plugin:
Resolves endpoint user information including:
User name and identity
Group membership
User properties and attributes
Department and organizational unit information
Retrieves details via LDAP queries when "Use as directory" is enabled
Why Other Options Are Incorrect:
B. Define authentication traffic - The plugin doesn't define traffic; it queries authentication servers for user information
C. Perform Radius authorization - This is the function of the RADIUS Plugin, not the User Directory plugin (though they work together)
E. Populate the Dashboard - Dashboard population is not a primary function of the User Directory plugin
User Directory vs. RADIUS Plugin:
According to the documentation:
Function
User Directory
RADIUS
Authenticate credentials
✓ Yes
✓ Yes (primary)
Query user details
✓ Yes (primary)
✗ No
802.1X authentication
✗ No
✓ Yes
Authorization
Partial
✓ Yes (primary)
Referenced Documentation:
User Directory plugin overview
About the User Directory Plugin
Initial Setup – User Directory
QUESTION DESCRIPTION:
When using the "Assign to VLAN action," why might it be useful to have a policy to record the original VLAN?
Select one:
Correct Answer & Rationale:
Answer: D
Explanation:
According to the Forescout Switch Plugin documentation, the correct answer is: "Since CounterACT reads the running config to find the original VLAN, any changes to switch running configs could overwrite this VLAN information".
Why Recording Original VLAN is Important:
According to the documentation:
When CounterACT assigns an endpoint to a quarantine VLAN:
Reading Original VLAN - CounterACT reads the switch running configuration to determine the original VLAN
Temporary Change - The endpoint is moved to the quarantine VLAN
Restoration Issue - If network administrators save configuration changes to the running config, CounterACT's reference to the original VLAN may be overwritten
Solution - Recording the original VLAN in a policy ensures you have a backup reference
Why Option D is the Most Accurate:
Option D states the key issue clearly: "any changes to switch running configs could overwrite this VLAN information." This is the most comprehensive and accurate statement because it acknowledges that ANY changes (not just those by administrators specifically) could cause the issue.
QUESTION DESCRIPTION:
What should be done after the Managed Windows devices are sent to a policy to determine the Windows 10 patch delivery optimization setting?
Correct Answer & Rationale:
Answer: E
Explanation:
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
After managed Windows devices are sent to a policy to determine the Windows 10 patch delivery optimization setting, the best practice is to write sub-rules to check for each of the DWORD values used in patch delivery optimization.
Windows 10 Patch Delivery Optimization DWORD Values:
Windows 10 patch delivery optimization is configured through DWORD registry settings in the following registry path:
Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\DeliveryOptimization
The primary DWORD value is DODownloadMode, which supports the following values:
0 = HTTP only, no peering
1 = HTTP blended with peering behind the same NAT (default)
2 = HTTP blended with peering across a private group
3 = HTTP blended with Internet peering
63 = HTTP only, no peering, no use of DO cloud service
64 = Bypass mode (deprecated in Windows 11)
Why Sub-Rules Are Required:
When implementing a policy to manage Windows 10 patch delivery optimization settings, administrators must create sub-rules for each possible DWORD configuration value because:
Different Organizational Requirements - Different departments or network segments may require different delivery optimization modes (e.g., value 1 for some devices, value 0 for others)
Compliance Checking - Each sub-rule verifies whether a device has the correct DWORD value configured according to organizational policy
Enforcement Actions - Once each sub-rule identifies a specific DWORD value, appropriate remediation actions can be applied (e.g., GPO deployment, messaging, notifications)
Granular Control - Sub-rules allow for precise identification of devices with non-compliant delivery optimization settings
Implementation Workflow:
Device is scanned and identified as Windows 10 managed device
Policy queries the DODownloadMode DWORD registry value
Multiple sub-rules evaluate the current DWORD value:
Sub-rule for value "0" (HTTP only)
Sub-rule for value "1" (Peering behind NAT)
Sub-rule for value "2" (Peering across private group)
Sub-rule for value "3" (Internet peering)
Sub-rule for value "63" (No peering, no cloud)
Matching sub-rule triggers appropriate policy actions
Why Other Options Are Incorrect:
A. Push out the proper DWORD setting via GPO - This is what you do AFTER checking via sub-rules, not what you do after sending devices to the policy
B. Non Windows 10 devices must be called out in sub-rules since they will not have the relevant DWORD - While non-Windows 10 devices should be excluded, the answer doesn't address the core requirement of checking each DWORD value
C. Manageable Windows devices are not required by this policy - This is incorrect; managed Windows devices are the focus of this policy
D. Non Windows 10 devices must be called out in sub-rules so that the relevant DWORD value may be changed - This misses the point; you check the DWORD values first, not change them in sub-rules
Referenced Documentation:
Microsoft Delivery Optimization Reference - Windows 10 Deployment
Forescout Administration Guide - Defining Policy Sub-Rules
How to use Group Policy to configure Windows Update Delivery Optimization
QUESTION DESCRIPTION:
What best defines a 'Post-Connect Methodology'?
Correct Answer & Rationale:
Answer: C
Explanation:
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
According to the Forescout Blog on Post-Connect Access Controls and the Comply-to-Connect framework documentation, a Post-Connect Methodology is best defined as treating endpoints as "Innocent until proven guilty".
Definition of Post-Connect Methodology:
According to the official documentation:
"Post-connect" is described as treating endpoints as innocent until they are proven guilty. They can connect to the network, during and after which they are assessed for acceptance criteria."
How Post-Connect Works:
According to the Post-Connect Access Controls blog:
Initial Connection - Endpoints are allowed to connect to the network immediately (innocent)
Assessment During/After Connection - After connecting, endpoints are assessed for acceptance criteria
Compliance Checking - Endpoints are checked for:
Corporate asset status (must be company-owned)
Security compliance (antivirus, patches, encryption, etc.)
Remediation or Quarantine - Based on assessment results:
Compliant endpoints: Full access
Non-compliant endpoints: Placed in quarantine for remediation
Post-Connect vs. Pre-Connect:
According to the Comply-to-Connect documentation:
Pre-Connect - "Guilty until proven innocent" - Endpoint must prove compliance BEFORE getting network access
Post-Connect - "Innocent until proven guilty" - Endpoint connects first, then compliance is assessed
Benefits of Post-Connect Methodology:
According to the documentation:
"The greatest benefit to the post-connect approach is a positive user experience. Unless a system is out of compliance and ends up in a quarantine, your company's users have no idea access controls are even taking place on the network."
Acceptance Criteria in Post-Connect:
According to the framework:
Corporate Asset Verification - Determines if the endpoint belongs to the organization
Compliance Assessment - Checks for:
Updated antivirus
Patch levels
Disk encryption status
Security tool functionality
If an endpoint fails these criteria, it's placed in quarantine (controlled network access) rather than being completely blocked.
Why Other Options Are Incorrect:
A. 802.1X is a flavor of Post-Connect - 802.1X is a pre-connect access control method (requires authentication before network access)
B. Guilty until proven innocent - This describes pre-connect methodology, not post-connect
D. Used subsequent to pre-connect - While post-connect can follow pre-connect, this doesn't define what post-connect is
E. Assessed for critical compliance before IP address is assigned - This describes pre-connect methodology
Referenced Documentation:
Forescout Blog - Post-Connect Access Controls
Comply-to-Connect Brief - Pre-connect vs Post-connect comparison
Achieving Comply-to-Connect Requirements with Forescout
QUESTION DESCRIPTION:
What is the default recheck timer for a NAC policy?
Correct Answer & Rationale:
Answer: B
Explanation:
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
According to the Forescout Administration Guide - Policy Main Rule Advanced Options, the default recheck timer for a NAC policy is 8 hours.
Default Policy Recheck Timer:
According to the official documentation:
"By default, both matched endpoints and unmatched endpoints are rechecked every eight hours, and on any admission event."
This 8-hour default ensures that all endpoints are periodically re-evaluated against policy conditions, regardless of whether they currently match the policy.
Recheck Configuration:
According to the documentation:
When you configure a policy's main rule advanced options:
Default Recheck Interval: 8 hours
Customizable Range: Can be configured from 1 hour to infinite (no recheck)
Applies to: All endpoints in the policy scope
Recheck Triggers:
According to the administration guide:
Policies recheck when:
Recheck Timer Expires - Every 8 hours by default
Admission Event - When specific network events occur
SecureConnector Event - When SC status changes
Referenced Documentation:
Forescout Platform Policy Main Rule Advanced Options
Main Rule Advanced Options
QUESTION DESCRIPTION:
Which of the following User Directory server settings is necessary to enable guest approval by sponsors?
Correct Answer & Rationale:
Answer: C
Explanation:
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
The Sponsor Group is the necessary User Directory server setting required to enable guest approval by sponsors. According to the Forescout User Directory Plugin Configuration Guide and Guest Management Portal documentation, Sponsor Groups must be created and configured to define the corporate employees (sponsors) who are authorized to approve or decline guest network access requests.
Sponsor Group Configuration:
In the Guest Management pane, the Sponsors tab is used to define the corporate employees who are authorized to log into the Guest Management Portal to approve network access requests from guests. These employees are assigned to specific Sponsor Groups, which control which sponsors can approve guest access requests.
How Sponsor Groups Enable Guest Approval:
Sponsor Definition - Corporate employees must be designated as sponsors and assigned to a Sponsor Group
Approval Authority - Sponsors in assigned groups can approve or decline guest network access requests
Authentication - When "Enable sponsor approval without authentication via emailed link" is selected, sponsors in the designated group can approve guests based on email link authorization
Guest Registration - Guest registration options connect Sponsor Groups to the guest approval workflow
Why Other Options Are Incorrect:
A. Policy to control - While policies are used for guest control, they do not define which sponsors can approve guests
B. Guest Tags - Guest Tags are used to classify and organize guest accounts, not to enable sponsor approval
D. Guest password policy - This setting controls password requirements for guests, not sponsor approval authority
E. Authentication Server - Authentication servers verify credentials but do not establish sponsor approval groups
Referenced Documentation:
Forescout User Directory Plugin Configuration Guide - Create Sponsors section
Guest Management Portal - Sponsor Configuration documentation
"Create sponsors" - Forescout Administration Guide section
A Stepping Stone for Enhanced Career Opportunities
Your profile having Forescout Certified Professional certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Forescout FSCP certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Forescout Exam FSCP
Achieving success in the FSCP Forescout exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in FSCP certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam FSCP!
In the backdrop of the above prep strategy for FSCP Forescout exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding FSCP exam prep. Here's an overview of Certachieve's toolkit:
Forescout FSCP PDF Study Guide
This premium guide contains a number of Forescout FSCP exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Forescout FSCP study guide pdf free download is also available to examine the contents and quality of the study material.
Forescout FSCP Practice Exams
Practicing the exam FSCP questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Forescout FSCP Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Forescout FSCP exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning FSCP exam dumps can increase not only your chances of success but can also award you an outstanding score.
Forescout FSCP Forescout Certified Professional FAQ
There are only a formal set of prerequisites to take the FSCP Forescout exam. It depends of the Forescout organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Forescout FSCP exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Forescout FSCP Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Forescout FSCP exam dumps to enhance your readiness for the exam.
Like any other Forescout Certification exam, the Forescout Certified Professional is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do FSCP exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The FSCP Forescout exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Forescout FSCP exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Forescout has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Forescout changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



