The CompTIA CyberSecurity Analyst CySA+ Certification Exam (CS0-003)
Passing CompTIA CompTIA CySA+ exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard CS0-003 Dumps
In 2026, CompTIA uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official CompTIA CS0-003 Exam Domains
Our curriculum is meticulously mapped to the CompTIA official blueprint.
Security Operations (33%)
The largest domain. Master the detection and analysis of malicious activity using modern tools. Focus on threat intelligence, threat hunting, and the use of SIEM/SOAR platforms to improve SOC efficiency and automate repeatable processes.
Vulnerability Management (30%)
Focus on the complete vulnerability lifecycle. Master the implementation of scanning methods, analyzing assessment tool outputs, and the critical skill of vulnerability prioritization based on risk, asset value, and exploitability.
Incident Response and Management (20%)
Master the incident management lifecycle. Focus on attack methodology frameworks (MITRE ATT&CK, Diamond Model), containment strategies, eradication, and post-incident activities like root cause analysis and forensic reporting.
Reporting and Communication (17%)
Master the "Business of Security." Focus on translating technical findings into actionable business decisions. Master vulnerability management reporting, compliance monitoring, and communicating risk to non-technical stakeholders.
CompTIA CS0-003 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
Which of the following is a nation-state actor least likely to be concerned with?
Correct Answer & Rationale:
Answer: D
Explanation:
A nation-state actor is a group or individual that conducts cyberattacks on behalf of a government or a political entity. They are usually motivated by national interests, such as espionage, sabotage, or influence operations. They are often highly skilled, resourced, and persistent, and they operate with the protection or support of their state sponsors. Therefore, they are less likely to be concerned with the forensic analysis for legal action of their actions, as they are unlikely to face prosecution or extradition in their own country or by international law. They are more likely to be concerned with the detection by the MITRE ATT & CK framework, which is a knowledge base of adversary tactics and techniques based on real-world observations. The MITRE ATT & CK framework can help defenders identify, prevent, and respond to cyberattacks by nation-state actors. They are also likely to be concerned with the detection or prevention of reconnaissance activities, which are the preliminary steps of cyberattacks that involve gathering information about the target, such as vulnerabilities, network topology, or user credentials. Reconnaissance activities can expose the presence, intent, and capabilities of the attackers, and allow defenders to take countermeasures. Finally, they are likely to be concerned with the examination of their actions and objectives, which can reveal their motives, strategies, and goals, and help defenders understand their threat profile and attribution.
QUESTION DESCRIPTION:
A security analyst is reviewing events that occurred during a possible compromise. The analyst obtains the following log:
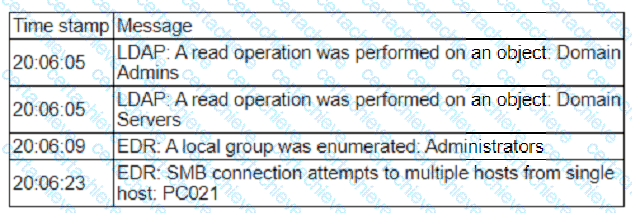
Which of the following is most likely occurring, based on the events in the log?
Correct Answer & Rationale:
Answer: A
Explanation:
1. Analyze the Log Evidence: The log displays a specific sequence of rapid-fire events (within 18 seconds) characteristic of automated reconnaissance tools used to map Active Directory environments.
20:06:05 (LDAP Reads): The attacker queries the directory for high-value groups (Domain Admins) and critical infrastructure (Domain Servers). They are not trying to log in; they are reading the membership lists to see who is important and where the servers are.
20:06:09 (EDR Enumeration): The attacker checks the local Administrators group. This is to see if the current compromised user has admin rights or who does.
20:06:23 (SMB Connections): The host PC021 attempts to connect to multiple other hosts. This indicates the attacker is testing where they can move laterally using the credentials or access they currently have.
2. Why this is " Finding the Shortest Path " (Option A): This behavior is the textbook signature of tools like BloodHound (or its data collector, SharpHound).
Concept: Adversaries use these tools to visualize relationships in Active Directory. They query LDAP to find out: " I am User A. Which computers can I access? Who is a Domain Admin? Is a Domain Admin logged into a computer I can access? "
Goal: The tool calculates the mathematical " shortest path " (graph theory) from the attacker ' s current low-level foothold to the ultimate target (Domain Admin).
The combination of LDAP querying (mapping the graph) and SMB connection attempts (verifying sessions/local admin rights) confirms the adversary is mapping out the network to find the most efficient route to total compromise.
Why the other options are incorrect:
B. An adversary is performing a vulnerability scan: Vulnerability scanners (like Nessus or Qualys) typically probe ports and services to identify unpatched software (CVEs). They generally do not focus on querying LDAP for " Domain Admins " group membership as their primary action.
C. An adversary is escalating privileges: While the attacker intends to escalate privileges eventually, the logs show enumeration (Discovery phase). They are currently looking for the path to escalate, not actively exploiting a vulnerability (like a kernel exploit) to change their privilege level in this specific snapshot.
D. An adversary is performing a password stuffing attack: Password stuffing involves high volumes of failed authentication attempts against a login service. The logs here show read operations and connection attempts, not the " Invalid Credential " errors associated with stuffing.
QUESTION DESCRIPTION:
An incident response team found indicators of compromise on a critical server. The team needs to isolate the server and collect technical evidence for further investigation. Which of the following pieces of data should be collected first in order to preserve sensitive information before isolating the server?
Correct Answer & Rationale:
Answer: D
Explanation:
The correct answer is D. Routing table. The routing table is volatile technical evidence because it is stored in memory and can change or be lost when the system is isolated, powered down, rebooted, or otherwise modified. In incident response and forensics, volatile evidence must be collected before less volatile evidence.
Exact supporting extract: the Sybex CySA+ Practice Tests explanation states that routing tables are typically stored in RAM, making them highly volatile. It also explains the order of volatility from least to most volatile as backups/printouts, disk drives, virtual memory, and finally CPU cache, registers, and RAM.
The Sybex CySA+ Study Guide states that forensic acquisition must account for the order of volatility, meaning how easily data can be lost. It explains that memory and cache data are highly volatile and may be lost if the system is powered off, while disk data is much less volatile.
The Secbay CySA+ guide also states that the order of volatility must be followed because failing to do so will likely result in evidence being lost. It specifically notes that volatile data is kept in areas such as CPU cache and memory, while archived media persists for much longer.
Why the other options are incorrect:
A. Hard disk is persistent storage and can be imaged later using forensic procedures.
B. Primary boot partition is also persistent disk evidence.
C. Malicious files are important, but files on disk are less volatile than memory-resident network state.
E. Static IP address is configuration information and is not as volatile as the active routing table.
D is correct because the routing table should be captured before isolation changes the server’s active network state.
QUESTION DESCRIPTION:
An auditor is reviewing an evidence log associated with a cybercrime. The auditor notices that a gap exists between individuals who were responsible for holding onto and transferring the evidence between individuals responsible for the investigation. Which of the following best describes the evidence handling process that was not properly followed?
Correct Answer & Rationale:
Answer: D
Explanation:
Thechain of custodyis a documented history that tracks how evidence is handled, collected, transported, and preserved at every stage of the forensic investigation. If a gap exists in the record of who transferred or accessed the evidence, it could call into question the integrity and admissibility of the evidence.
Validating data integrity (Option A)refers to ensuring that the forensic image is identical to the original data, often using cryptographic hashing, but it does not address procedural gaps in documentation.
Preservation (Option B)involves protecting the original evidence from modification or loss but does not include logging transfers of custody.
Legal hold (Option C)refers to a requirement to preserve data for legal proceedings, which is different from tracking evidence handling.
Thus, the correct answer isD, as chain of custody directly relates to tracking who had access to the evidence and when.
QUESTION DESCRIPTION:
An organization ' s email account was compromised by a bad actor. Given the following Information:
Which of the following is the length of time the team took to detect the threat?
Correct Answer & Rationale:
Answer: B
Explanation:
The threat was detected from the time the emails were sent at 8:30 a.m. to when the recipients started alerting the organization’s help desk about the email at 8:45 a.m., taking a total of 15 minutes. The detection time is the time elapsed between the occurrence of an incident and its discovery by the security team . The other options are either too short or too long based on the given information. References: : Detection Time : Incident Response Metrics: Mean Time to Detect and Mean Time to Respond
QUESTION DESCRIPTION:
Which of the following threat-modeling procedures is in the OWASP Web Security Testing Guide?
Correct Answer & Rationale:
Answer: C
Explanation:
The OWASP Web Security Testing Guide (WSTG) includes a section on threat modeling, which is a structured approach to identify, quantify, and address the security risks associated with an application. The first step in the threat modeling process is decomposing the application, which involves creating use cases, identifying entry points, assets, trust levels, and data flow diagrams for the application. This helps to understand the application and how it interacts with external entities, as well as to identify potential threats and vulnerabilities1. The other options are not part of the OWASP WSTG threat modeling process.
QUESTION DESCRIPTION:
A cybersecurity analyst is recording the following details
* ID
* Name
* Description
* Classification of information
* Responsible party
In which of the following documents is the analyst recording this information?
Correct Answer & Rationale:
Answer: A
Explanation:
A risk register typically contains details like ID, name, description, classification of information, and responsible party. It’s used for tracking identified risks and managing them.Recording details like ID, Name, Description, Classification of information, and Responsible party is typically done in a Risk Register. This document is used to identify, assess, manage, and monitor risks within an organization. It ' s not directly related to incident response or change control documentation.
QUESTION DESCRIPTION:
A web developer reports the following error that appeared on a development server when testing a new application:
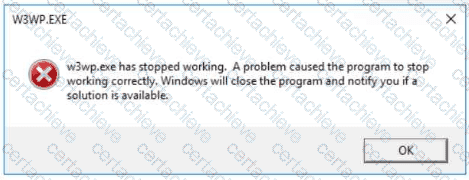
Which of the following tools can be used to identify the application ' s point of failure?
Correct Answer & Rationale:
Answer: C
Explanation:
The error indicates the application (running under w3wp.exe, the IIS worker process) crashed/stopped working. To identify the application’s point of failure, you need a debugger that can perform dynamic analysis—setting breakpoints, stepping through execution, inspecting memory/stack/registers, and/or analyzing a crash dump/core dump to pinpoint where the failure occurred.
The CySA+ All-in-One guide describes exactly how a debugger is used to analyze a crash and determine the program’s state at the time of failure:
Exact extract (All-in-One Exam Guide):
“Using a debugger, you can load the core dump file and examine the program’s state at the time of the crash…”
It then explains that debuggers (including Immunity) are used for dynamic analysis by stepping through code and examining runtime behavior:
Exact extract (All-in-One Exam Guide):
“Immunity… offers… features… valuable for security analysts… Security analysts can leverage Immunity to set breakpoints, step through code, and monitor the execution flow of a program… allowing analysts to… uncover critical security information.”
The Sybex CySA+ Study Guide reinforces that debuggers are used for dynamic analysis of executables and explicitly lists Immunity Debugger as a key tool:
Exact extract (Sybex Study Guide):
“Debuggers… allow testers to perform dynamic analysis of executable files… Immunity debugger is designed specifically to support penetration testing and the reverse engineering of malware.”
Also, the official CompTIA CS0-003 objectives list Immunity Debugger under tools used to analyze output from vulnerability assessment tools (debuggers category), confirming it as an expected exam-relevant tool choice:
Exact extract (CompTIA CS0-003 Objectives):
“Debuggers: Immunity debugger, GNU debugger (GDB)”
Why the other options are wrong
A. OpenVAS is an infrastructure vulnerability scanner, not a crash/failure debugger.
B. Angry IP Scanner is a network scanning/mapping tool for IPs/ports, not application crash analysis.
D. Burp Suite is a web application testing/proxy tool (great for analyzing HTTP requests, auth, app logic flaws), but it does not directly pinpoint a process crash point like a debugger can.
References (CompTIA CySA+ CS0-003 documents / study guides used):
Mya Heath et al., CompTIA CySA+ All-in-One Exam Guide (CS0-003): debuggers analyze crash/core dump state; Immunity Debugger supports breakpoints/stepping/execution monitoring
Mike Chapple & David Seidl, CompTIA CySA+ Study Guide (CS0-003): debuggers support dynamic analysis; Immunity debugger noted as a key debugger tool
CompTIA CySA+ CS0-003 Exam Objectives v4.0: lists “Immunity debugger” under debugger tools
QUESTION DESCRIPTION:
Which of the following best explains the importance of utilizing an incident response playbook?
Correct Answer & Rationale:
Answer: B
Explanation:
Incident response playbooksprovide a structuredstep-by-step guidefor handling security incidents. Theydefine actions to takewhen specificthreat indicators or eventsoccur, ensuring acoordinated and consistent response.
Option A (Prioritizing business-critical assets)relates more todisaster recovery (DR)than incident response.
Option C (Documenting asset management)is part ofIT governance, not incident response.
Option D (Defining DR sites)falls underbusiness continuity planning, not real-time incident handling.
Thus,B is the best answer, asplaybooks are designed to trigger appropriate responses to incidents.
QUESTION DESCRIPTION:
An analyst is conducting routine vulnerability assessments on the company infrastructure. When performing these scans, a business-critical server crashes, and the cause is traced back to the vulnerability scanner. Which of the following is the cause of this issue?
Correct Answer & Rationale:
Answer: B
Explanation:
The scanner is running in active mode, which is the cause of this issue. Active mode is a type of vulnerability scanning that sends probes or requests to the target systems to test their responses and identify potential vulnerabilities. Active mode can provide more accurate and comprehensive results, but it can also cause more network traffic, performance degradation, or system instability. In some cases, active mode can trigger denial-of-service (DoS) conditions or crash the target systems, especially if they are not configured to handle the scanning requests or if they have underlying vulnerabilities that can be exploited by the scanner12. Therefore, the analyst should use caution when performing active mode scanning, and avoid scanning business-critical or sensitive systems without proper authorization and preparation3. References: Vulnerability Scanning for my Server - Spiceworks Community, Negative Impacts of Automated Vulnerability Scanners and How … - Acunetix, Vulnerability Scanning Best Practices
A Stepping Stone for Enhanced Career Opportunities
Your profile having CompTIA CySA+ certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in CompTIA CS0-003 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace CompTIA Exam CS0-003
Achieving success in the CS0-003 CompTIA exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in CS0-003 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam CS0-003!
In the backdrop of the above prep strategy for CS0-003 CompTIA exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding CS0-003 exam prep. Here's an overview of Certachieve's toolkit:
CompTIA CS0-003 PDF Study Guide
This premium guide contains a number of CompTIA CS0-003 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of CompTIA CS0-003 study guide pdf free download is also available to examine the contents and quality of the study material.
CompTIA CS0-003 Practice Exams
Practicing the exam CS0-003 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces CompTIA CS0-003 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
CompTIA CS0-003 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning CS0-003 exam dumps can increase not only your chances of success but can also award you an outstanding score.
CompTIA CS0-003 CompTIA CySA+ FAQ
There are only a formal set of prerequisites to take the CS0-003 CompTIA exam. It depends of the CompTIA organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you CompTIA CS0-003 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using CompTIA CS0-003 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of CompTIA CS0-003 exam dumps to enhance your readiness for the exam.
Like any other CompTIA Certification exam, the CompTIA CySA+ is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do CS0-003 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The CS0-003 CompTIA exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the CompTIA CS0-003 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. CompTIA has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If CompTIA changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



