The Splunk Enterprise Security Certified Admin Exam (SPLK-3001)
Passing Splunk Splunk Enterprise Security Certified Admin exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard SPLK-3001 Dumps
In 2026, Splunk uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official Splunk SPLK-3001 Exam Domains
Our curriculum is meticulously mapped to the Splunk official blueprint.
Installation & Configuration (15%)
Master the preparation of Splunk environments, installation of ES on search heads, management of specialized ES user roles, and critical post-install configuration tasks.
Monitoring & Investigation (10%)
Deep focus on security posture analysis, incident review workflows, notable event management, and conducting comprehensive security investigations within the ES framework.
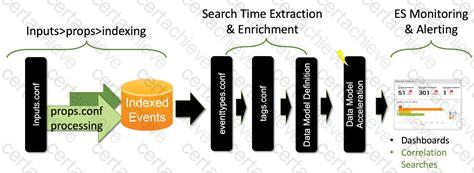
ES Deployment & Topology (10%)
Identifying optimal deployment topologies, managing indexing strategies for security data, and understanding the implementation of ES Data Models for high performance.
Correlation Search Management (20%)
Mastering both the creation and tuning of correlation searches, configuring adaptive responses for automated mitigation, and adjusting search sensitivity to reduce false positives.
Validating & Ingesting ES Data (10%)
Planning ES data inputs, configuring specialized technology add-ons (TAs), and ensuring data quality through proper field mapping and normalization.
Threat Intelligence & Identity (10%)
Configuring the Threat Intelligence Framework to manage indicators of compromise (IOCs) and maintaining asset and identity lookup lists for enriched security context.
Splunk SPLK-3001 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
Which indexes are searched by default for CIM data models?
Correct Answer & Rationale:
Answer: D
Explanation:
By default, the CIM data models search all indexes in Splunk Enterprise Security. This means that any event that matches the tags and fields of a data model can be included in the data model, regardless of the index where it is stored. However, this can also affect the performance and efficiency of the data model searches, especially if there are many indexes that do not contain relevant data for the data model. Therefore, it is recommended to use the indexes allow list setting in the CIM add-on to constrain the indexes that each data model searches. The indexes allow list is a comma-separated list of indexes that you want to include in the data model search. You can specify index names or index macros. For example, you can set the indexes allow list for the Authentication data model to index=main, index=security, index=auth to limit the search to only those three indexes 1 2 . References = 1 : Managing data models in Enterprise Security - Splunk Lantern - Indexes allow list. 2 : Overview of the Splunk Common Information Model - Splunk Documentation - Why the CIM exists.
QUESTION DESCRIPTION:
What is an example of an ES asset?
Correct Answer & Rationale:
Answer: C
Explanation:
According to the Splunk Enterprise Security documentation, an asset is a physical or logical device that is part of your network infrastructure, such as a server, a workstation, a router, or a firewall. An asset can have various attributes, such as IP address, MAC address, DNS name, NT host name, priority, business unit, owner, and others. Splunk Enterprise Security uses asset data to enrich and correlate security events and provide context for analysis. You can manage asset data using the Asset and Identity Management page in Splunk Enterprise Security. See Manage assets and identities in Splunk Enterprise Security for more details.
The other options are not examples of ES assets, but they may be related to other types of data. A MAC address is an attribute of an asset, not an asset itself. A user name is an example of an identity, which is a person or group that is associated with an asset or an event. Splunk Enterprise Security uses identity data to enrich and correlate security events and provide context for analysis. You can manage identity data using the Asset and Identity Management page in Splunk Enterprise Security. See Manage assets and identities in Splunk Enterprise Security for more details. People is a data model in the Splunk Common Information Model (CIM), which provides a common standard for organizing and naming data fields across different data sources. Splunk Enterprise Security uses the CIM to enable cross-source analysis and correlation of security events. The People data model contains the fields and tags for events that are related to people, such as user names, email addresses, phone numbers, and others. See People for more details. Therefore, the correct answer is C. Server. References =
Manage assets and identities in Splunk Enterprise Security
People
QUESTION DESCRIPTION:
Which data model populated the panels on the Risk Analysis dashboard?
Correct Answer & Rationale:
Answer: A
Explanation:
The Risk Analysis dashboard uses the Risk data model to populate the panels. The Risk data model is a data model that contains information about the risk scores and risk modifiers of various objects, such as systems, users, hashes, and network artifacts. The Risk data model accelerates these fields for the Risk Analysis and Incident Review dashboards. The Risk data model also handles case insensitive asset and identity correlation, allowing risk modifiers that are applied to system or user name variants to be correctly attributed to the same risk_object 1 . The other options, B, C, and D, are not correct. The Audit data model contains information about audit events, such as user logins, password changes, and system access. The Domain Analysis data model contains information about the domains that are visited by the systems in the network. The Threat Intelligence data model contains information about the threat intelligence sources, indicators, and matches. References =
Risk Analysis dashboard
Risk data model
Risk Analysis framework
QUESTION DESCRIPTION:
A newly built custom dashboard needs to be available to a team of security analysts In ES. How is It possible to Integrate the new dashboard?
Correct Answer & Rationale:
Answer: C
Explanation:
According to the Splunk Enterprise Security documentation, the best way to integrate a newly built custom dashboard to a team of security analysts in ES is to set the dashboard permissions to allow access by es_analysts and use the navigation editor to add it to the menu. This will ensure that the dashboard is visible and accessible to the users with the es_analyst role, which is the default role for security analysts in ES. The navigation editor allows you to customize the menu bar of ES and add links to custom dashboards, reports, or other views. See Customize Splunk Enterprise Security dashboards to fit your use case and Customize the navigation bar for more details.
The other options are not recommended, because they either do not integrate the dashboard properly or they create unnecessary complexity. Adding links on the ES home page to the new dashboard is not a good option, because it does not integrate the dashboard into the menu bar and it may clutter the home page. Creating a new role inherited from es_analyst, making the dashboard permissions read-only, and making this dashboard the default view for the new role is not a good option, because it creates a redundant role and it may confuse the users who expect to see the Security Posture dashboard as the default view. Adding the dashboard to a custom add-in app and installing it to ES using the Content Manager is not a good option, because it requires creating and maintaining a separate app and it may cause conflicts or performance issues with ES. Therefore, the correct answer is C. Set the dashboard permissions to allow access by es_analysts and use the navigation editor to add it to the menu. References =
Customize the navigation bar
Roles and capabilities in Splunk Enterprise Security
Content Management
Customize Splunk Enterprise Security dashboards to fit your use case
 How to Create Custom Dashboards and Alerts to Achi ... - Splunk Community
How to Create Custom Dashboards and Alerts to Achi ... - Splunk Community
QUESTION DESCRIPTION:
Which component normalizes events?
Correct Answer & Rationale:
Answer: D
Explanation:
A technology add-on (TA) is a Splunk app that contains the configurations for ingesting and normalizing data from a specific data source or vendor. A TA can include sourcetype definitions, index-time and search-time field extractions, event types, tags, lookups, and other settings that help to map the data to the Splunk Common Information Model (CIM). The CIM is a set of predefined data models that provide a common standard for organizing and naming data fields across different data sources. Splunk Enterprise Security uses the CIM to enable cross-source analysis and correlation of security events. Therefore, the correct answer is D. Technology add-on. References =
Technology add-ons overview
Splunk Common Information Model Add-on
Normalizing Enterprise Security data with technology add-ons
 Onboarding data to Splunk Enterprise Security
Onboarding data to Splunk Enterprise Security
QUESTION DESCRIPTION:
Which of the following features can the Add-on Builder configure in a new add-on?
Correct Answer & Rationale:
Answer: B
Explanation:
The correct answer is B. Normalize data. The Add-on Builder can configure a new add-on to normalize data by mapping the data fields to the Common Information Model (CIM). The CIM provides a common language for describing data across domains and technologies. Normalizing data enables the data to be used by other Splunk apps, such as Splunk Enterprise Security and Splunk IT Service Intelligence. The Add-on Builder can also con figure other features in a new add-on, such as collecting data from various sources, extracting fields from the data, creating alert actions and adaptive response actions, and testing and validating the add-on. However, the Add-on Builder cannot configure an add-on to expire data, summarize data, or translate data. These are not features of the Add-on Builder. References =
Splunk Add-on Builder
[Use the Common Information Model in Splunk Web]
QUESTION DESCRIPTION:
The option to create a Short ID for a notable event is located where?
Correct Answer & Rationale:
Answer: B
Explanation:
According to the Splunk Enterprise Security documentation, the option to create a Short ID for a notable event is located in the Event Details section of the notable event. The Event Details section shows the basic information about the notable event, such as title, description, urgency, owner, status, and others. It also provides a link to Create Short ID, which generates a 6-digit alphanumeric code that can be used to identify and share the notable event. The Short ID is appended to the URL of the Incident Review dashboard and can be used to filter the notable events by the Short ID field. See Manually create a notable event in Splunk Enterprise Security for more details. Therefore, the correct answer is B. The Event Details. References = Manually create a notable event in Splunk Enterprise Security .
QUESTION DESCRIPTION:
An administrator is provisioning one search head prior to installing ES. What are the reference minimum requirements for OS, CPU, and RAM for that machine?
Correct Answer & Rationale:
Answer: D
Explanation:
According to the Splunk Enterprise Security Admin documentation, the minimum hardware requirements for a dedicated search head running ES are as follows: OS: 64 bit, RAM: 32 GB, CPU: 16 cores. These requirements are based on the assumption that the search head is not performing any other tasks besides running ES. The documentation also recommends having at least 500 GB of disk space for the search head. References = Splunk Enterprise Security Admin documentation
QUESTION DESCRIPTION:
What can be exported from ES using the Content Management page?
Correct Answer & Rationale:
Answer: C
Explanation:
The Content Management page in Splunk Enterprise Security allows you to export any content type that is listed on the page as an app. The content types include correlation searches, glass tables, dashboards, reports, saved searches, key indicators, workbench panels, and managed lookups. You can use the export option to share custom content with other ES instances, such as migrating customized searches from a development or testing environment into production. You can also import content from other ES instances or from Splunkbase using the Content Management page. References =
Export content from Splunk Enterprise Security as an app
Import content to Splunk Enterprise Security as an app
QUESTION DESCRIPTION:
Which of the following steps will make the Threat Activity dashboard the default landing page in ES?
Correct Answer & Rationale:
Answer: C
Explanation:
According to the Splunk Enterprise Security documentation, the way to make the Threat Activity dashboard the default landing page in ES is to use the Edit Navigation page and click the ‘Set this as the default view’ checkmark for Threat Activity. The Edit Navigation page allows you to customize the menu bar of ES and add links to custom dashboards, reports, or other views. You can also set the default view for each app context, which determines the landing page when you open the app. To set the Threat Activity dashboard as the default view, you need to do the following steps:
On the Enterprise Security menu bar, select Configure > General > Navigation.
In the Edit Navigation page, select the Enterprise Security app context from the drop-down menu.
In the Navigation XML section, find the line that contains the view name ‘threat_activity’.
Add the attribute default=“true” to the line and remove the same attribute from any other line in the same app context.
Click Save Changes to apply the changes to the Edit Navigation page.
This will make the Threat Activity dashboard the default landing page when you open the Enterprise Security app. See Customize the navigation bar for more details.
The other options are not the correct ways to make the Threat Activity dashboard the default landing page in ES. Dragging and dropping the Threat Activity view to the top of the page will not change the default view, but only the order of the menu items. Selecting Enterprise Security as the default application will not change the default view within the app, but only the app that opens when you log in to Splunk. Editing the Threat Activity view settings will not change the default view, but only the title, description, permissions, and schedule of the dashboard. Therefore, the correct answer is C. From the Edit Navigation page, click the ' Set this as the default view " checkmark for Threat Activity. References = Customize the navigation bar .
A Stepping Stone for Enhanced Career Opportunities
Your profile having Splunk Enterprise Security Certified Admin certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Splunk SPLK-3001 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Splunk Exam SPLK-3001
Achieving success in the SPLK-3001 Splunk exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in SPLK-3001 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam SPLK-3001!
In the backdrop of the above prep strategy for SPLK-3001 Splunk exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding SPLK-3001 exam prep. Here's an overview of Certachieve's toolkit:
Splunk SPLK-3001 PDF Study Guide
This premium guide contains a number of Splunk SPLK-3001 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Splunk SPLK-3001 study guide pdf free download is also available to examine the contents and quality of the study material.
Splunk SPLK-3001 Practice Exams
Practicing the exam SPLK-3001 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Splunk SPLK-3001 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Splunk SPLK-3001 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning SPLK-3001 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Splunk SPLK-3001 Splunk Enterprise Security Certified Admin FAQ
There are only a formal set of prerequisites to take the SPLK-3001 Splunk exam. It depends of the Splunk organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Splunk SPLK-3001 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Splunk SPLK-3001 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Splunk SPLK-3001 exam dumps to enhance your readiness for the exam.
Like any other Splunk Certification exam, the Splunk Enterprise Security Certified Admin is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do SPLK-3001 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The SPLK-3001 Splunk exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Splunk SPLK-3001 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Splunk has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Splunk changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



