The CompTIA SecurityX Certification Exam (CAS-005)
Passing CompTIA CompTIA CASP exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard CAS-005 Dumps
In 2026, CompTIA uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official CompTIA CAS-005 Exam Domains
Our curriculum is meticulously mapped to the CompTIA official blueprint.
Governance, Risk, and Compliance (20%)
Master the strategic side of security. Focus on impact analysis for "extreme but plausible" scenarios, third-party supply chain risk, and the ethical governance of AI. Learn to align security programs with industry-specific regulations like GDPR, HIPAA, and the Digital Markets Act.
Security Architecture (27%)
Master the design of resilient enterprise systems. Focus on Zero Trust concepts, secure SDLC integration, and designing cloud-native capabilities. Learn to establish trust boundaries and perform architectural reviews for mergers, acquisitions, and divestitures.
Security Engineering (31%)
The largest and most technical domain. Master the practical implementation of identity management (MFA/SCIM), hardware security, and advanced cryptography. Focus on engineering secure network infrastructures and automating security workflows across specialized systems (IoT/ICS).
Security Operations (22%)
Master detection and response at scale. Focus on threat intelligence, vulnerability management, and incident response playbooks. Learn to perform complex malware analysis, forensic investigations, and use behavioral analytics to hunt for advanced persistent threats (APTs).
CompTIA CAS-005 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
A security engineer wants to stay up-to-date on new detections that are released on a regular basis. The engineer ' s organization uses multiple tools rather than one specific vendor security stack. Which of the following rule-based languages is the most appropriate to use as a baseline for detection rules with the multiple security tool setup?
Correct Answer & Rationale:
Answer: A
Explanation:
Step-by-Step Explanation:
Sigma (A) is a rule-based detection language that is vendor-agnostic, meaning it can be used across different SIEM (Security Information and Event Management) tools. Unlike YARA (B), which focuses on file-based detection, Sigma provides a standardized way to create rules that work across various security platforms.
QUESTION DESCRIPTION:
A security analyst is using data provided from a recent penetration test to calculate CVSS scores to prioritize remediation. Which of the following metric groups would the analyst need to determine to get the overall scores? (Select three).
Correct Answer & Rationale:
Answer: A, E, F
Explanation:
The Common Vulnerability Scoring System (CVSS) v3.1 uses three metric groups to calculate overall scores:Base,Temporal, andEnvironmental.
Base (E):Mandatory metrics assessing exploitability (e.g., attack vector) and impact (confidentiality, integrity, availability).
Temporal (A):Optional metrics reflecting the current state of the vulnerability (e.g., exploit availability, remediation level).
Environmental (F):Optional metrics tailoring the score to the organization’s context (e.g., security requirements).
B, C, D (Availability, Integrity, Confidentiality):These are subcomponents of the Base Impact metrics, not standalone groups.
G (Impact):A categorywithin Base, not a group.
H (Attack vector):A single Base metric, not a group.
QUESTION DESCRIPTION:
An organization with a remote workforce has a new client with the following requirements:
Consultants need to travel to the client site.
The company has proprietary information on its hard drives.
The company prohibits BYOD.
Which of the following would be the most beneficial for the organization to implement?
Correct Answer & Rationale:
Answer: D
Explanation:
The best answer is D. Host-based encryption . The strongest clue is that the company has proprietary information on its hard drives and consultants must travel with company-managed devices because BYOD is prohibited. That makes protection of data at rest on the endpoint the primary concern. Host-based encryption protects the contents of the drive if a laptop is lost, stolen, or physically accessed during travel. CompTIA’s SecurityX certification emphasizes building secure solutions across complex environments and supporting resilient enterprise protection, which includes securing endpoints and sensitive data stored on them.
Why the other options are not best:
A. Virtual hardware does not directly protect the data on the hard drive if the device is lost or stolen. B. Measured boot helps validate platform integrity at startup, but it does not primarily protect confidential data at rest. C. Secure enclave can protect certain secrets and key material, but it is narrower than full host-based encryption for an entire laptop drive. Because the requirement is specifically about proprietary data on traveling endpoints, full device or host-based encryption is the most beneficial control.
QUESTION DESCRIPTION:
Which of the following is the main reason quantum computing advancements are leading companies and countries to deploy new encryption algorithms?
Correct Answer & Rationale:
Answer: A
Explanation:
Advancements in quantum computing pose a significant threat to current encryption systems, especially those based on the difficulty of factoring large prime numbers, such as RSA. Quantum computers have the potential to solve these problems exponentially faster than classical computers, making current cryptographic systems vulnerable.
Why Large Prime Numbers are Vulnerable:
Shor ' s Algorithm: Quantum computers can use Shor ' s algorithm to factorize large integers efficiently, which undermines the security of RSA encryption.
Cryptographic Breakthrough: The ability to quickly factor large prime numbers means that encrypted data, which relies on the hardness of thismathematical problem, can be decrypted.
Other options, while relevant, do not capture the primary reason for the shift towards new encryption algorithms:
B. Zero Trust security architectures: While important, the shift to homomorphic encryption is not the main driver for new encryption algorithms.
C. Perfect forward secrecy: It enhances security but is not the main reason for new encryption algorithms.
D. Real-time IP traffic capture: Quantum computers pose a more significant threat to the underlying cryptographic algorithms than to the real-time capture of traffic.
QUESTION DESCRIPTION:
A security analystreviews the following report:
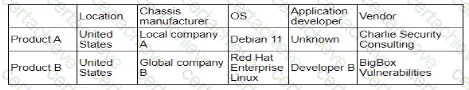
Which of the following assessments is the analyst performing?
Correct Answer & Rationale:
Answer: B
Explanation:
The table shows detailed information about products, includinglocation, chassis manufacturer, OS, application developer, and vendor. This type of information is typically assessed in a supply chain assessment to evaluate the security and reliability of components and services from different suppliers.
Why Supply Chain Assessment?
Component Evaluation: Assessing the origin and security of each component used in the products, including hardware, software, and third-party services.
Vendor Reliability: Evaluating the security practices and reliability of vendors involved in providing components or services.
Risk Management: Identifying potential risks associated with the supply chain, such as vulnerabilities in third-party components or insecure development practices.
Other types of assessments do not align with the detailed supplier and component information provided:
A. System: Focuses on individual system security, not the broader supply chain.
C. Quantitative: Focuses on numerical risk assessments, not supplier information.
D. Organizational: Focuses on internal organizational practices, not external suppliers.
QUESTION DESCRIPTION:
A company wants to invest in research capabilities with the goal to operationalize the research output. Which of the following is the best option for a security architect to recommend?
Correct Answer & Rationale:
Answer: B
Explanation:
Investing in a threat intelligence platform is the best option for a company looking to operationalize research output. A threat intelligence platform helps in collecting, processing, and analyzing threat data to provide actionable insights. These platforms integrate data from various sources, including dark web monitoring, honeypots, and other security tools, to offer a comprehensive view of the threat landscape.
Why a Threat Intelligence Platform?
Data Integration: It consolidates data from multiple sources, including dark web monitoring and honeypots, making it easier to analyze and derive actionableinsights.
Actionable Insights: Provides real-time alerts and reports on potential threats, helping the organization take proactive measures.
Operational Efficiency: Streamlines the process of threat detection and response, allowing the security team to focus on critical issues.
Research and Development: Facilitates the operationalization of research output by providing a platform for continuous monitoring and analysis of emerging threats.
Other options, while valuable, do not offer the same level of integration and operationalization capabilities:
A. Dark web monitoring: Useful for specific threat intelligence but lacks comprehensive operationalization.
C. Honeypots: Effective for detecting and analyzing specific attack vectors but not for broader threat intelligence.
D. Continuous adversary emulation: Important for testing defenses but not for integrating and operationalizing threat intelligence.
QUESTION DESCRIPTION:
An analyst must remediate vulnerabilities in IoT devices within 24 hours. These vulnerabilities:
Have CVSS scores of less than 7.0
Have updates available
Will not significantly impact production systems if remediation is unsuccessful
Which of the following practices is best for the analyst to use to resolve the issue?
Correct Answer & Rationale:
Answer: A
Explanation:
The best answer is A. Automated patching . The scenario already states that updates are available, the vulnerabilities must be remediated within 24 hours , and the risk of unsuccessful remediation is low because production impact would not be significant. That makes direct, rapid deployment of fixes the most appropriate practice. CompTIA’s SecurityX objectives include operational response and automation themes, and the official exam summary explicitly references automation capabilities in multiple areas. In this scenario, automation is not just helpful; it is the most practical way to meet the time requirement consistently across IoT devices.
Why the other options are incorrect:
B. Vulnerability prioritization is something you do before deciding what to remediate first, but the question already gives the prioritization context and asks how to resolve the issue. C. Forced restart does not remediate the vulnerabilities. D. SOAR playbook creation might support a broader workflow in the future, but creating a playbook is slower and less direct than simply using automated patching when patches already exist and risk is acceptable. Under the stated conditions, automated patching is the best-fit operational response.
QUESTION DESCRIPTION:
An organization is looking for gaps in its detection capabilities based on the APTs that may target the industry Which of the following should the security analyst use to perform threatmodeling?
Correct Answer & Rationale:
Answer: D
Explanation:
The ATT & CK (Adversarial Tactics, Techniques, and Common Knowledge) framework is the best tool for a security analyst to use for threat modeling when looking for gaps in detection capabilities based on Advanced Persistent Threats (APTs) that may target the industry. Here’s why:
Comprehensive Framework: ATT & CK provides a detailed and structured repository of known adversary tactics and techniques based on real-world observations. It helps organizations understand how attackers operate and what techniques they might use.
Gap Analysis: By mapping existing security controls against the ATT & CK matrix, analysts can identify which tactics and techniques are not adequately covered by current detection and mitigation measures.
Industry Relevance: The ATT & CK framework is continuously updated with the latest threat intelligence, making it highly relevant for industries facing APT threats. It provides insights into specific APT groups and their preferred methods of attack.
QUESTION DESCRIPTION:
A network engineer must ensure that always-on VPN access is enabled Curt restricted to company assets Which of the following best describes what the engineer needs to do ' '
Correct Answer & Rationale:
Answer: A
Explanation:
To ensure always-on VPN access is enabled and restricted to company assets, the network engineer needs to generate device certificates using the specific template settings required for the company ' s VPN solution. These certificates ensure that only authorized devices can establish a VPN connection.
Why Device Certificates are Necessary:
Authentication: Device certificates authenticate company assets, ensuring that only authorized devices can access the VPN.
Security: Certificates provide a higher level of security compared to username and password combinations, reducing the risk of unauthorized access.
Compliance: Certificates help in meeting security policies and compliance requirements by ensuring that only managed devices can connect to the corporate network.
Other options do not provide the same level of control and security for always-on VPN access:
B. Modify signing certificates for IKE version 2: While important for VPN protocols, it does not address device-specific authentication.
C. Create a wildcard certificate: This is not suitable for device-specific authentication and could introduce security risks.
D. Add the VPN hostname as a SAN entry: This is more related to certificate management and does not ensure device-specific authentication.
QUESTION DESCRIPTION:
An organization is developing an in-house software platform to support capital planning and reporting functions. In addition to role-based access controls and auditing/logging capabilities, the product manager must include requirements associated with archiving data and immutable backups. Which of the following organizational considerations are most likely associated with this requirement? (Select two)
Correct Answer & Rationale:
Answer: E, F
Explanation:
The requirements for archiving data and immutable backups directly align with legal hold compliance (E) and ransomware resilience (F).
Legal hold compliance ensures that organizations can retain data in a tamper-proof manner when required for litigation, regulatory mandates, or audits. Immutable backups satisfy this by preventing unauthorized changes or deletion, ensuring evidence and records are preserved.
Ransomware resilience is also a key factor. Immutable backups allow recovery from ransomware attacks, as attackers cannot encrypt or delete data stored in read-only or write-once media. This reduces downtime and supports business continuity.
Options A (crypto-export), B (supply chain), C (device attestation), and D (quality assurance) do not relate directly to data archiving or immutable storage.
CAS-005 stresses aligning security controls with business continuity and compliance requirements. By focusing on legal and ransomware-related considerations, the organization ensures both regulatory and operational resilience.
A Stepping Stone for Enhanced Career Opportunities
Your profile having CompTIA CASP certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in CompTIA CAS-005 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace CompTIA Exam CAS-005
Achieving success in the CAS-005 CompTIA exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in CAS-005 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam CAS-005!
In the backdrop of the above prep strategy for CAS-005 CompTIA exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding CAS-005 exam prep. Here's an overview of Certachieve's toolkit:
CompTIA CAS-005 PDF Study Guide
This premium guide contains a number of CompTIA CAS-005 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of CompTIA CAS-005 study guide pdf free download is also available to examine the contents and quality of the study material.
CompTIA CAS-005 Practice Exams
Practicing the exam CAS-005 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces CompTIA CAS-005 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
CompTIA CAS-005 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning CAS-005 exam dumps can increase not only your chances of success but can also award you an outstanding score.
CompTIA CAS-005 CompTIA CASP FAQ
There are only a formal set of prerequisites to take the CAS-005 CompTIA exam. It depends of the CompTIA organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you CompTIA CAS-005 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using CompTIA CAS-005 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of CompTIA CAS-005 exam dumps to enhance your readiness for the exam.
Like any other CompTIA Certification exam, the CompTIA CASP is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do CAS-005 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The CAS-005 CompTIA exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the CompTIA CAS-005 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. CompTIA has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If CompTIA changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



