The Aruba Certified Network Security Expert Written Exam (HPE6-A84)
Passing HP ACA - Network Security exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard HPE6-A84 Dumps
In 2026, HP uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official HP HPE6-A84 Exam Domains
Our curriculum is meticulously mapped to the HP official blueprint.
Strategy, Design, and Security Concepts (15%)
Master the architecture of secure enterprise networks. Understanding threat landscapes, risk management, and the design of multi-layered defense strategies using the Aruba ESP (Edge Services Platform).
Secure Infrastructure and Connectivity (25%)
Deep dive into securing Aruba AOS-CX switches and Gateways. Mastery of User-Based Tunneling (UBT), dynamic segmentation, and implementing advanced firewall policies at the network edge.
ClearPass Policy Manager & Secure Access (30%)
Expert-level configuration of ClearPass (CPPM). Advanced profiling, specialized authentication (802.1X, MAC-Auth), and implementing complex enforcement policies across wired and wireless infrastructures.
Threat Detection and AI-Driven Analytics (20%)
Mastering Aruba IntroSpect and AI-powered security monitoring. Identifying anomalies, machine learning-based threat detection, and integrating security telemetry into a centralized dashboard.
Monitoring, Reporting, and Troubleshooting (10%)
Proactive system health monitoring and advanced troubleshooting of security incidents. Using Aruba Central for reporting, audit logs, and ensuring continuous compliance across the security fabric.
HP HPE6-A84 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
Refer to the exhibit.
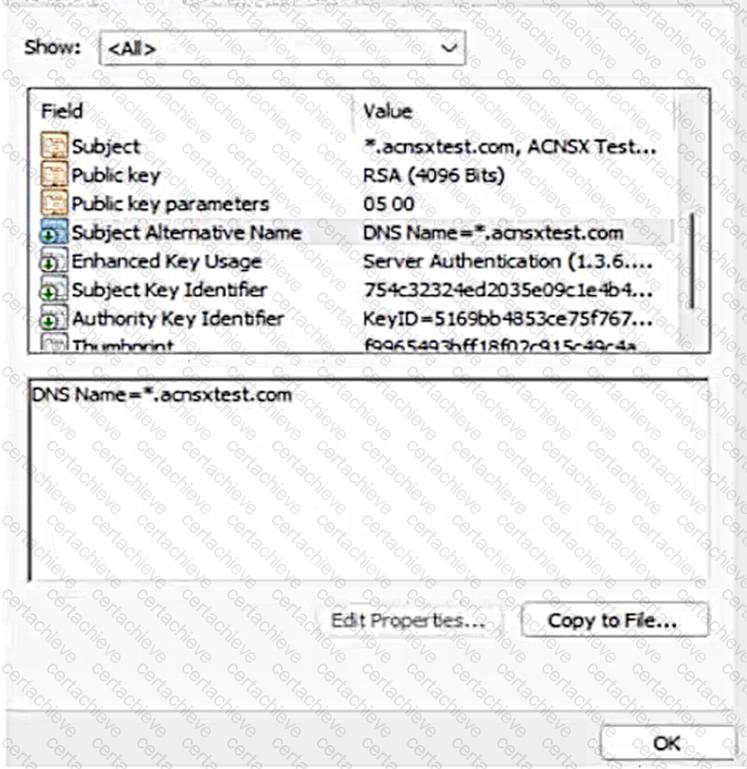
You have been given this certificate to install on a ClearPass server for the RADIUS/EAP and RadSec usages.
What is one issue?
Correct Answer & Rationale:
Answer: B
Explanation:
The exhibit shows a screenshot of a certificate that has the following information:
The subject common name (CN) is *.clearpass.local, which is a wildcard domain name that matches any subdomain under clearpass.local.
The subject alternative names (SANs) are DNS Name=clearpass.local and DNS Name=*.clearpass.local, which are the same as the subject CN.
The issuer CN is clearpass.local, which is the same as the subject domain name.
The key usage (KU) is Digital Signature and Key Encipherment, which are required for RADIUS/EAP and RadSec usages.
The extended key usage (EKU) is Server Authentication and Client Authentication, which are also required for RADIUS/EAP and RadSec usages.
The issue with this certificate is that it uses a fully qualified the ‘.local’ domain name, which is a reserved domain name for local networks that cannot be registered on the public Internet. This means that the certificate cannot be verified by any public certificate authority (CA), and therefore cannot be trusted by any external devices or servers that communicate with ClearPass. This could cause problems for RADIUS/EAP and RadSec usages, as they rely on secure and authenticated connections between ClearPass and other devices or servers.
To avoid this issue, the certificate should use a valid domain name that can be registered on the public Internet, such as clearpass.com or clearpass.net. This way, the certificate can be issued by a public CA that is trusted by most devices and servers, and can be verified by them. Alternatively, if the certificate is intended to be used only within a private network, it should be issued by a private CA that is trusted by all devices and servers within that network.
QUESTION DESCRIPTION:
A customer needs you to configure Aruba ClearPass Policy Manager (CPPM) to authenticate domain users on domain computers. Domain users, domain computers, and domain controllers receive certificates from a Windows CA. CPPM should validate these certificates and verify that the users and computers have accounts in Windows AD. The customer requires encryption for all communications between CPPM and the domain controllers.
You have imported the root certificate for the Windows CA to the ClearPass CA Trust list.
Which usages should you add to it based on these requirements?
Correct Answer & Rationale:
Answer: C
Explanation:
EAP (Extensible Authentication Protocol) is a framework that allows different authentication methods to be used for network access. EAP is used for RADIUS/EAP authentication, which is a common method for authenticating domain users on domain computers using certificates. EAP requires that the RADIUS server, such as ClearPass Policy Manager (CPPM), validates the certificates presented by the clients and verifies their identity against an identity source, such as Windows AD. Therefore, the root certificate for the Windows CA that issues the certificates to the clients should have the EAP usage in the ClearPass CA Trust list.
Radsec (RADIUS over TLS) is a protocol that allows secure and encrypted communication between RADIUS servers and clients using TLS. Radsec is used for encrypting all communications between CPPM and the domain controllers, which act as RADIUS clients. Radsec requires that both the RADIUS server and the RADIUS client validate each other’s certificates and establish a TLS session. Therefore, the root certificate for the Windows CA that issues the certificates to the domain controllers should have the Radsec usage in the ClearPass CA Trust list.
QUESTION DESCRIPTION:
A customer has an AOS 10 architecture, consisting of Aruba AP and AOS-CX switches, managed by Aruba Central. The customer wants to obtain information about the clients, such as their general category and OS.
What should you explain?
Correct Answer & Rationale:
Answer: C
Explanation:
Aruba Central can provide visibility and profiling of clients using the Client Insights feature, which is an AI-powered solution that uses native infrastructure telemetry to identify and classify clients based on their OS and general category. This feature does not require any additional hardware or software, such as gateways, IP helpers, or packet sniffers. It works by collecting and analyzing data from the Aruba APs and AOS-CX switches that are managed by Aruba Central. You can find more information about Client Insights in the Visibility and profiling solutions | HPE Aruba Networking page and the Clients Profile - Aruba page.
QUESTION DESCRIPTION:
When would you implement BPDU protection on an AOS-CX switch port versus BPDU filtering?
Correct Answer & Rationale:
Answer: B
Explanation:
BPDU (Bridge Protocol Data Unit) is a message that is exchanged between switches to maintain the spanning tree topology and prevent loops. BPDU protection and BPDU filtering are two features that can be configured on AOS-CX switch ports to enhance security and performance.
BPDU protection is a feature that disables a port if it receives a BPDU, indicating that an unauthorized switch or device has been connected to the port. BPDU protection is typically used on edge ports, which are ports that connect to end devices such as PCs or printers, and are not expected to receive BPDUs. BPDU protection prevents rogue devices from connecting to the network and affecting the spanning tree topology.
BPDU filtering is a feature that prevents a port from sending or receiving BPDUs, effectively isolating the port from the spanning tree topology. BPDU filtering is typically used on inter-switch ports, which are ports that connect to other switches, for specialized use cases such as creating a separate spanning tree domain or reducing the overhead of BPDUs. BPDU filtering should be used with caution, as it can create loops or inconsistencies in the network.
You can find more information about how to configure BPDU protection and BPDU filtering on AOS-CX switch ports in the [Configuring Spanning Tree Protocol - Aruba] page and the [AOS-CX Switching Configuration Guide] page. The other options are not correct because they either use BPDU protection or BPDU filtering on the wrong type of ports or for the wrong purpose. For ex ample, using BPDU protection on inter-switch ports would disable the ports if they receive BPDUs, which are expected in normal operation. Using BPDU filtering on edge ports would allow rogue devices to connect to the network and create loops or affect the spanning tree topology.
QUESTION DESCRIPTION:
Refer to the scenario.
An organization wants the AOS-CX switch to trigger an alert if its RADIUS server (cp.acnsxtest.local) rejects an unusual number of client authentication requests per hour. After some discussions with other Aruba admins, you are still not sure how many rejections are usual or unusual. You expect that the value could be different on each switch.
You are helping the developer understand how to develop an NAE script for this use case.
You are helping a customer define an NAE script for AOS-CX switches. The script will monitor statistics from a RADIUS server defined on the switch. You want to future proof the script by enabling admins to select a different hostname or IP address for the monitored RADIUS server when they create an agent from the script.
What should you recommend?
Correct Answer & Rationale:
Answer: B
Explanation:
This is because a parameter is a variable that can be defined and modified by the user or the script, and can be used to customize the behavior and output of the NAE script. A parameter can be referred to by using the syntax self ^ramsfname], where ramsfname is the name of the parameter.
By defining a parameter for the RADIUS server, you can make the NAE script more flexible and adaptable to different scenarios and switches. The parameter can be set to a default value, such as cp.acnsxtest.local, but it can also be changed by the user or the script based on the network conditions and requirements. For example, the user can select a different hostname or IP address for the monitored RADIUS server when they create an agent from the script, or the script can automatically detect and update the parameter based on the switch configuration. This way, the NAE script can monitor statistics from any RADIUS server defined on the switch without hard-coding the server name or IP address in the monitor URI.
A. Use this variable, %{radius-ipV when defining the monitor URI in the NAE agent script. This is not a valid recommendation because %{radius-ipV is not a valid variable in NAE scripts. Variables in NAE scripts are prefixed with self ^ramsfname], not with %. Moreover, radius-ipV is not a predefined variable that contains the RADIUS server name or IP address, but rather a generic term that could refer to any IP version.
C. Use a callback action to collect the name of any RADIUS servers defined on the switch at the time the agent is created. This is not a bad recommendation, but it is not as good as defining a parameter. A callback action is a feature that allows an NAE script to execute a command on the switch and collect its output for further processing or display. A callback action can be used to collect the name of any RADIUS servers defined on the switch by executing a command such as show radius-server or show running-config radius-server and parsing its output. However, a callback action might not be as fast or reliable as using a parameter, as it depends on the availability and responsiveness of the switch and its CLI.
D. Make the script editable so that admins can edit it on demand when they are creating scripts. This is not a good recommendation because making the script editable exposes it to potential errors or modifications that could affect its functionality or performance. Making the script editable also requires more effort and expertise from the admins, who might not be familiar with NAE scripting syntax or logic. Moreover, making the script editable does not future proof it, as it does not allow for dynamic changes or updates based on network conditions or requirements.
10of30
QUESTION DESCRIPTION:
Refer to the scenario.
A customer requires these rights for clients in the “medical-mobile” AOS firewall role on Aruba Mobility Controllers (MCs):
 Permitted to receive IP addresses with DHCP
Permitted to receive IP addresses with DHCP
 Permitted access to DNS services from 10.8.9.7 and no other server
Permitted access to DNS services from 10.8.9.7 and no other server
 Permitted access to all subnets in the 10.1.0.0/16 range except denied access to 10.1.12.0/22
Permitted access to all subnets in the 10.1.0.0/16 range except denied access to 10.1.12.0/22
 Denied access to other 10.0.0.0/8 subnets
Denied access to other 10.0.0.0/8 subnets
 Permitted access to the Internet
Permitted access to the Internet
 Denied access to the WLAN for a period of time if they send any SSH traffic
Denied access to the WLAN for a period of time if they send any SSH traffic
 Denied access to the WLAN for a period of time if they send any Telnet traffic
Denied access to the WLAN for a period of time if they send any Telnet traffic
 Denied access to all high-risk websites
Denied access to all high-risk websites
External devices should not be permitted to initiate sessions with “medical-mobile” clients, only send return traffic.
The exhibits below show the configuration for the role.
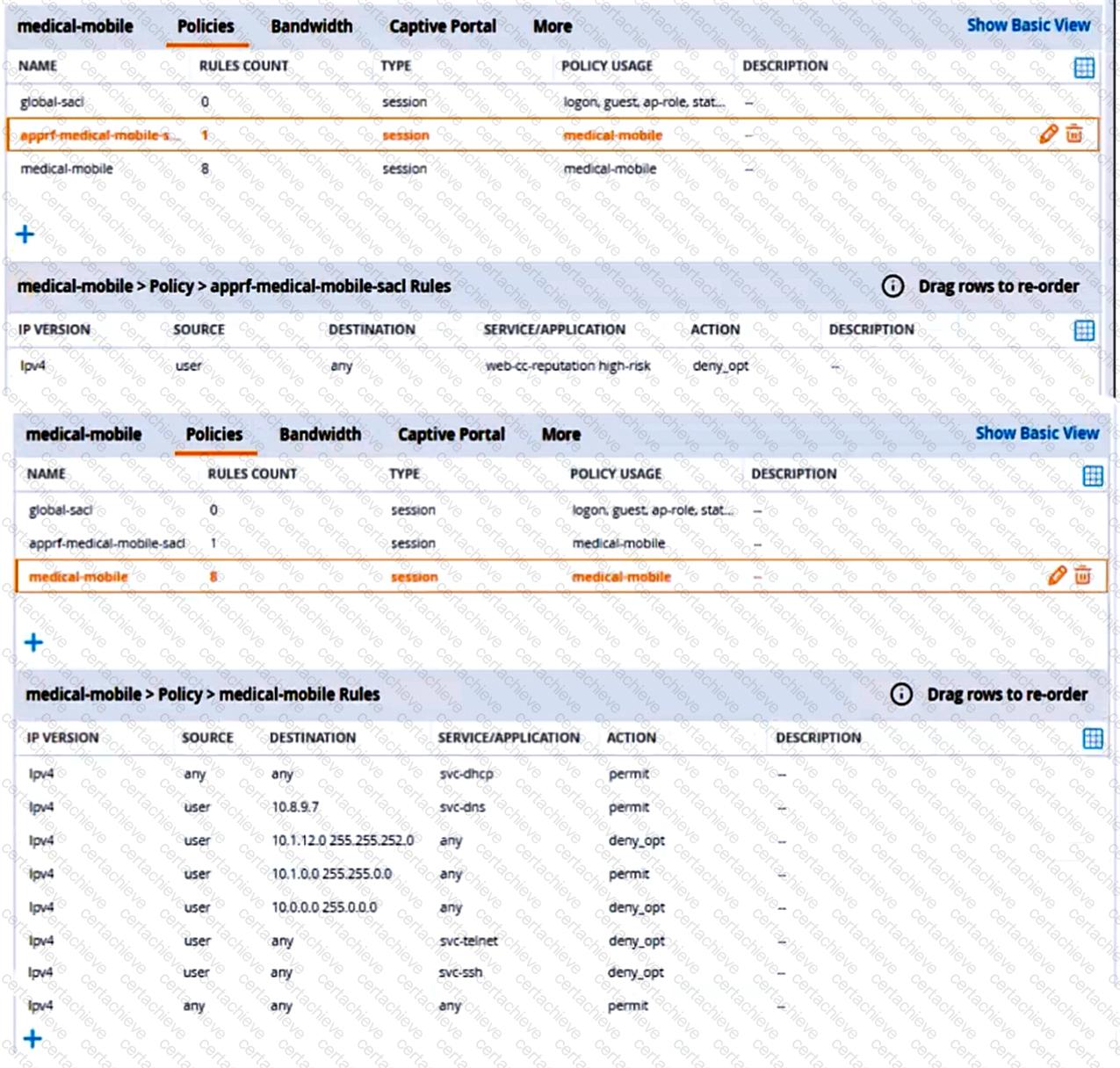
There are multiple issues with this configuration. What is one change you must make to meet the scenario requirements? (In the options, rules in a policy are referenced from top to bottom. For example, “medical-mobile” rule 1 is “ipv4 any any svc-dhcp permit,” and rule 8 is “ipv4 any any any permit”.)
Correct Answer & Rationale:
Answer: B
Explanation:
The subnet mask in rule 3 of the “medical-mobile” policy is currently 255.255.252.0, which means that the rule denies access to the 10.1.12.0/22 subnet as well as the adjacent 10.1.16.0/22 subnet 1 . This is not consistent with the scenario requirements, which state that only the 10.1.12.0/22 subnet should be denied access, while the rest of the 10.1.0.0/16 range should be permitted access.
To fix this issue, the subnet mask in rule 3 should be changed to 255.255.248.0, which means that the rule only denies access to the 10.1.8.0/21 subnet, which includes the 10.1.12.0/22 subnet 1 . This way, the rule matches the scenario requirements more precisely.
QUESTION DESCRIPTION:
You are working with a developer to design a custom NAE script for a customer. The NAE agent should trigger an alert when ARP inspection drops packets on a VLAN. The customer wants the admins to be able to select the correct VLAN ID for the agent to monitor when they create the agent.
What should you tell the developer to do?
Correct Answer & Rationale:
Answer: B
Explanation:
A custom NAE script is a Python script that defines the monitors, the alert-trigger logic, and the remedial actions for an NAE agent. A monitor is a URI that specifies the data source and the data type that the NAE agent should collect and analyze. For example, to monitor the ARP inspection statistics on a VLAN, the monitor URI would be something like this:
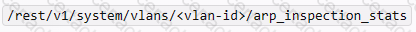
where < vlan-id > is the ID of the VLAN to be monitored.
To allow the admins to select the correct VLAN ID for the agent to monitor when they create the agent, you need to define a VLAN ID parameter in the NAE script. A parameter is a variable that can be set by the user when creating or modifying an agent. A parameter can be referenced in other parts of the script by using the syntax ${parameter-name}. For example, to define a VLAN ID parameter and reference it in the monitor URI, you would write something like this:
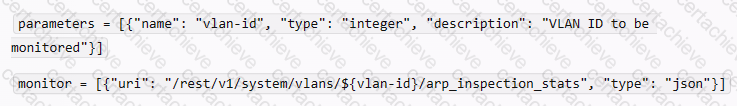
This way, when the admins create or modify the agent, they can enter the VLAN ID that they want to monitor, and the NAE script will use that value in the monitor URI.
You can find more information about how to write custom NAE scripts and use parameters in the NAE Scripting Guide
QUESTION DESCRIPTION:
Refer to the scenario.
A customer is migrating from on-prem AD to Azure AD as its sole domain solution. The customer also manages both wired and wireless devices with Microsoft Endpoint Manager (Intune).
The customer wants to improve security for the network edge. You are helping the customer design a ClearPass deployment for this purpose. Aruba network devices will authenticate wireless and wired clients to an Aruba ClearPass Policy Manager (CPPM) cluster (which uses version 6.10).
The customer has several requirements for authentication. The clients should only pass EAP-TLS authentication if a query to Azure AD shows that they have accounts in Azure AD. To further refine the clients’ privileges, ClearPass also should use information collected by Intune to make access control decisions.
The customer wants you to configure CPPM to collect information from Intune on demand during the authentication process.
What should you tell the Intune admins about the certificates issued to clients?
Correct Answer & Rationale:
Answer: B
Explanation:
To configure CPPM to collect information from Intune on demand during the authentication process, you need to use the Intune extension for ClearPass. This extension allows ClearPass to query Intune for device compliance and configuration information using the Intune API. To use this extension, you need to register an app in Azure AD and grant it the required permissions to access Intune 1
The Intune extension uses the device ID as the key to query Intune for device information. The device ID is a unique identifier that is assigned by Intune to each enrolled device. The device ID can be obtained from the client certificate that is used for EAP-TLS authentication. Therefore, the certificates issued to clients must include the Intune ID in the subject name, so that ClearPass can extract it and use it to query Intune 2
The certificates issued to clients do not need to be issued by a well-known, trusted CA, as long as ClearPass trusts the CA that issued them. The certificates do not need to include the client MAC address in the subject name, as this is not relevant for querying Intune. The certificates do not need to be issued by a ClearPass Onboard CA, as this is not a requirement for using the Intune extension.
QUESTION DESCRIPTION:
A customer has an AOS 10-based solution, including Aruba APs. The customer wants to use Cloud Auth to authenticate non-802.1X capable IoT devices.
What is a prerequisite for setting up the device role mappings?
Correct Answer & Rationale:
Answer: B
Explanation:
According to the Aruba Cloud Authentication and Policy Overview 1 , one of the prerequisites for configuring Cloud Authentication and Policy is to configure Device Insight (client profile) tags in Central. Device Insight tags are used to identify and classify IoT devices based on their behavior and characteristics. These tags can then be mapped to client roles, which are defined in the WLAN configuration for IAPs 2 . Client roles are used to enforce role-based access policies for the IoT devices. Therefore, option B is the correct answer.
Option A is incorrect because NetConductor is not related to Cloud Authentication and Policy. NetConductor is a cloud-based network management solution that simplifies the deployment and operation of Aruba Instant networks.
Option C is incorrect because integrating Aruba ClearPass Policy Manager (CPPM) and Device Insight is not a prerequisite for setting up the device role mappings. CPPM and Device Insight can work together to provide enhanced visibility and control over IoT devices, but they are not required for Cloud Authentication and Policy.
Option D is incorrect because creating global role-to-role firewall policies in Central is not a prerequisite for setting up the device role mappings. Global role-to-role firewall policies are used to define the traffic rules between different client roles across the entire network, but they are not required for Cloud Authentication and Policy.
QUESTION DESCRIPTION:
You are reviewing an endpoint entry in ClearPass Policy Manager (CPPM) Endpoints Repository.
What is a good sign that someone has been trying to gain unauthorized access to the network?
Correct Answer & Rationale:
Answer: C
Explanation:
A profile conflict occurs when ClearPass Policy Manager (CPPM) detects a change in the device category or OS family of an endpoint that has been previously profiled. This could indicate that someone has spoofed the MAC address of a legitimate device and is trying to gain unauthorized access to the network. For example, if an endpoint that was previously profiled as a Printer suddenly shows a new profile of Computer, this could be a sign of an attack. You can find more information about profile conflicts and how to resolve them in the ClearPass Policy Manager User Guide1. The other options are not necessarily signs of unauthorized access, as they could have other explanations. For example, multiple DHCP options under the fingerprints could indicate that the device has connected to different networks or subnets, an Unknown status could indicate that the device has not been authenticated yet, and a lack of hostname or a random hostname could indicate that the device has not been configured properly or has been reset to factory settings.
A Stepping Stone for Enhanced Career Opportunities
Your profile having ACA - Network Security certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in HP HPE6-A84 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace HP Exam HPE6-A84
Achieving success in the HPE6-A84 HP exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in HPE6-A84 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam HPE6-A84!
In the backdrop of the above prep strategy for HPE6-A84 HP exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding HPE6-A84 exam prep. Here's an overview of Certachieve's toolkit:
HP HPE6-A84 PDF Study Guide
This premium guide contains a number of HP HPE6-A84 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of HP HPE6-A84 study guide pdf free download is also available to examine the contents and quality of the study material.
HP HPE6-A84 Practice Exams
Practicing the exam HPE6-A84 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces HP HPE6-A84 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
HP HPE6-A84 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning HPE6-A84 exam dumps can increase not only your chances of success but can also award you an outstanding score.
HP HPE6-A84 ACA - Network Security FAQ
There are only a formal set of prerequisites to take the HPE6-A84 HP exam. It depends of the HP organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you HP HPE6-A84 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using HP HPE6-A84 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of HP HPE6-A84 exam dumps to enhance your readiness for the exam.
Like any other HP Certification exam, the ACA - Network Security is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do HPE6-A84 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The HPE6-A84 HP exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the HP HPE6-A84 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. HP has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If HP changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



