The Palo Alto Networks XSIAM Analyst (XSIAM-Analyst)
Passing Paloalto Networks Security Operations exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard XSIAM-Analyst Dumps
In 2026, Paloalto Networks uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Paloalto Networks XSIAM-Analyst Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
With regard to Attack Surface Rules, how often are external scans updated?
Correct Answer & Rationale:
Answer: B
Explanation:
The correct answer is B - Daily .
In Cortex XSIAM's Attack Surface Management (ASM), external scans and associated attack surface rules are refreshed and updated on a daily basis . Daily updates ensure that security analysts are provided with timely and relevant insights regarding exposed assets and potential vulnerabilities that could impact the organization's security posture.
"External scans for Attack Surface Rules are updated daily to ensure the latest and most relevant security visibility."
Document Reference: XSIAM Analyst ILT Lab Guide.pdf
Exact Page: Page 41 (Attack Surface Management Section)
QUESTION DESCRIPTION:
What information is provided in the timeline view of Cortex XSIAM?
Correct Answer & Rationale:
Answer: D
Explanation:
The correct answer is D – Sequence of events, alerts, rules and other actions involved over the lifespan of an incident .
The timeline view in Cortex XSIAM provides a chronological sequence of all events, alerts, and actions that have occurred in relation to a specific incident, helping analysts understand the incident’s progression from start to finish.
"The timeline view provides a detailed, chronological sequence of events, alerts, and actions for the lifespan of an incident."
Document Reference: XSIAM Analyst ILT Lab Guide.pdf
Page: Page 32 (Incident Handling section)
===========
QUESTION DESCRIPTION:
During an investigation of an alert with a completed playbook, it is determined that no indicators exist from the email "indicator@test.com" in the Key Assets & Artifacts tab of the parent incident. Which command will determine if Cortex XSIAM has been configured to extract indicators as expected?
Correct Answer & Rationale:
Answer: C
Explanation:
The correct answer is C, the !checkIndicatorExtraction text="indicator@test.com" command.
This command specifically verifies if Cortex XSIAM has been correctly configured to extract indicators from given text. It ensures that the text provided ("indicator@test.com") would indeed be recognized and extracted as an indicator under the current configuration of Cortex XSIAM.
Other provided commands do not directly verify the indicator extraction configuration:
Option A: IcreateNewIndicator manually creates an indicator; it does not validate extraction capability.
Option B: !extractIndicators attempts extraction immediately but does not verify existing configuration explicitly.
Option D: Iemailvalue command is generally for creating or querying email indicators, not verifying extraction configuration.
Therefore, the explicit functionality for checking if indicator extraction is configured correctly within Cortex XSIAM is precisely covered by !checkIndicatorExtraction.
Reference Extract from Official Document:
"Verify if Cortex XSIAM is correctly configured to extract indicators using the command !checkIndicatorExtraction text= < value > ."
This exact description confirms that option C is the correct answer to validate the configuration explicitly.
QUESTION DESCRIPTION:
Which attribution evidence will have the lowest confidence level when evaluating assets to determine if they belong to an organization’s attack surface?
Correct Answer & Rationale:
Answer: C
Explanation:
The correct answer is C – An asset attributed to the organization because the Subject Organization field contains the company name.
When determining ownership of assets in the attack surface, attribution based solely on the Subject Organization field containing the company name is considered less reliable than evidence based on domain registration, authoritative DNS relationships, or manual analyst validation. This is because the Subject Organization field may contain non-unique or common names, leading to a higher rate of false associations, and is not as strong as direct registration records or explicit analyst verification.
“The confidence level is lowest when asset attribution is based on the Subject Organization field, since this field may not be unique to the organization and can result in inaccurate mapping.”
Document Reference: XSIAM Analyst ILT Lab Guide.pdf
Page: Page 42 (Attack Surface Management section)
QUESTION DESCRIPTION:
In which two locations can mapping be configured for indicators? (Choose two.)
Correct Answer & Rationale:
Answer: A, B
Explanation:
The correct answers are A (Feed Integration settings) and B (Classification & Mapping tab) .
Feed Integration settings: Mapping of indicator fields can be configured directly within the feed integration configuration, allowing incoming threat intelligence feeds to be parsed and mapped correctly to XSIAM fields.
Classification & Mapping tab: This tab is available in various integration and indicator settings, enabling detailed field mapping and classification logic for incoming indicators.
"Mapping for indicators can be set within the Classification & Mapping tab or during Feed Integration setup to ensure proper parsing and normalization."
Document Reference: XSIAM Analyst ILT Lab Guide.pdf
Page: Page 36 (Threat Intel Management section)
===========
QUESTION DESCRIPTION:
SCENARIO:
A security analyst has been assigned a ticket from the help desk stating that users are experiencing errors when attempting to open files on a specific network share. These errors state that the file format cannot be opened. IT has verified that the file server is online and functioning, but that all files have unusual extensions attached to them.
The security analyst reviews alerts within Cortex XSIAM and identifies malicious activity related to a possible ransomware attack on the file server. This incident is then escalated to the incident response team for further investigation.
Upon reviewing the incident, the responders confirm that ransomware was successfully executed on the file server. Other details of the attack are noted below:
• An unpatched vulnerability on an externally facing web server was exploited for initial access
• The attackers successfully used Mimikatz to dump sensitive credentials that were used for privilege escalation
• PowerShell was used on a Windows server for additional discovery, as well as lateral movement to other systems
• The attackers executed SystemBC RAT on multiple systems to maintain remote access
• Ransomware payload was downloaded on the file server via an external site "file io"
QUESTION STATEMENT:
Which hunt collection category in Cortex XSIAM should the incident responders use to identify all systems where the attackers established persistence during the attack?
Correct Answer & Rationale:
Answer: A
Explanation:
The correct answer is A – Remote Access .
The Remote Access hunt collection category in Cortex XSIAM is specifically designed to help incident responders identify endpoints where attackers have installed remote access tools (RATs) or backdoors, which are classic methods of attacker persistence. In this scenario, the attackers executed SystemBC RAT on multiple systems to maintain remote access, making the "Remote Access" category the most relevant for finding all endpoints where persistence was established.
"Remote Access hunt collections in Cortex XSIAM identify the presence of remote access tools such as RATs and backdoors used by attackers to maintain persistence on endpoints. Analysts should review this collection category after incidents involving tools like SystemBC RAT."
Document Reference: XSIAM Analyst ILT Lab Guide.pdf, Page 28 (Alerting and Detection / Threat Intel Management sections)
QUESTION DESCRIPTION:
Which two methods can be used to create and share queries into the Query Library? (Choose two.)
Correct Answer & Rationale:
Answer: B, C
Explanation:
The correct answers are B and C .
From XQL Search , you can save existing queries directly to your personal Query Library and then choose to share them with others by enabling the sharing option.
You can also build new queries in the XQL Search field, then use "Save as" and select "Query to Library," followed by enabling the "Share with others" option.
"Queries can be created and saved to the Query Library from XQL Search either by saving existing queries or using the 'Save as' feature after building a new query. The 'Share with others' option allows for team collaboration."
Document Reference: XSIAM Analyst ILT Lab Guide.pdf
Page: Page 25 (Dashboards, Reports, and Widgets section)
===========
QUESTION DESCRIPTION:
A Cortex XSIAM analyst is investigating a security incident involving a workstation after having deployed a Cortex XDR agent for 45 days. The incident details include the Cortex XDR Analytics Alert "Uncommon remote scheduled task creation." Which response will mitigate the threat?
Correct Answer & Rationale:
Answer: A
Explanation:
The correct answer is A – Initiate the endpoint isolate action to contain the threat.
For incidents indicating possible remote compromise or unauthorized task creation, the most effective initial response is endpoint isolation . This cuts off the endpoint’s network access, preventing lateral movement and limiting attacker activity until further investigation and remediation.
“The endpoint isolate action is the primary containment step in incidents involving suspected remote compromise, halting network communication to reduce further risk.”
Document Reference: XSIAM Analyst ILT Lab Guide.pdf
Page: Page 40 (Incident Handling/SOC section)
QUESTION DESCRIPTION:
Why would an analyst schedule an XQL query?
Correct Answer & Rationale:
Answer: B
Explanation:
The correct answer is B – To retrieve data either at specific intervals or at a specified time.
Scheduling XQL queries allows analysts and teams to automate the retrieval of data at regular intervals or specific times (such as daily, hourly, or during set windows), supporting reporting, monitoring, and automation workflows without requiring manual intervention.
"Analysts can schedule XQL queries to automatically retrieve data or generate reports at regular intervals or specified times."
Document Reference: EDU-270c-10-lab-guide_02.docx (1).pdf
Page: Page 25 (Data Analysis with XQL section)
===========
QUESTION DESCRIPTION:
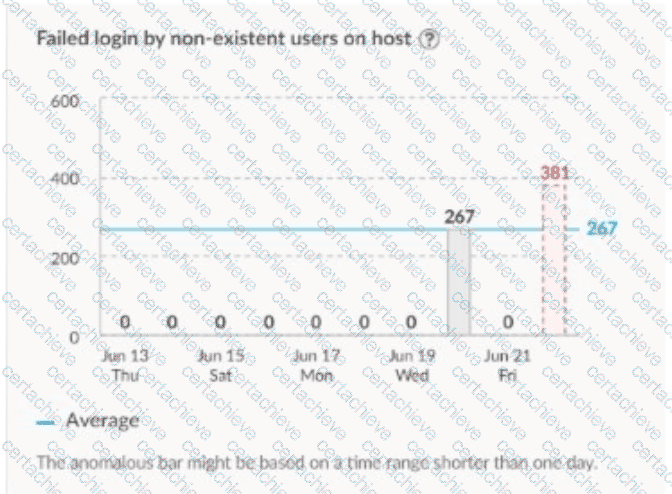
Which type of analytics will trigger the alert on the image shown?
Correct Answer & Rationale:
Answer: D
Explanation:
Comprehensive and Detailed Explanation From Exact Extract:
The correct answer is D – Anomaly .
In Cortex XSIAM, Anomaly analytics are designed to trigger alerts when a monitored activity deviates significantly from the established baseline or historical average. In the image, the "Failed login by non-existent users on host" metric remains at zero for several days and then suddenly spikes to 267 and 381—far above the average threshold. This significant deviation from the established norm is identified by the analytics engine as an anomaly and will trigger an alert for further investigation.
“Anomaly analytics identify significant deviations from established baselines or averages, such as unusual spikes in failed login attempts or other behavioral outliers, and trigger alerts for potential threats.”
Document Reference: XSIAM Analyst ILT Lab Guide.pdf
Page: Page 28 (Alerting and Detection section)
A Stepping Stone for Enhanced Career Opportunities
Your profile having Security Operations certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Paloalto Networks XSIAM-Analyst certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Paloalto Networks Exam XSIAM-Analyst
Achieving success in the XSIAM-Analyst Paloalto Networks exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in XSIAM-Analyst certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam XSIAM-Analyst!
In the backdrop of the above prep strategy for XSIAM-Analyst Paloalto Networks exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding XSIAM-Analyst exam prep. Here's an overview of Certachieve's toolkit:
Paloalto Networks XSIAM-Analyst PDF Study Guide
This premium guide contains a number of Paloalto Networks XSIAM-Analyst exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Paloalto Networks XSIAM-Analyst study guide pdf free download is also available to examine the contents and quality of the study material.
Paloalto Networks XSIAM-Analyst Practice Exams
Practicing the exam XSIAM-Analyst questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Paloalto Networks XSIAM-Analyst Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Paloalto Networks XSIAM-Analyst exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning XSIAM-Analyst exam dumps can increase not only your chances of success but can also award you an outstanding score.
Paloalto Networks XSIAM-Analyst Security Operations FAQ
There are only a formal set of prerequisites to take the XSIAM-Analyst Paloalto Networks exam. It depends of the Paloalto Networks organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Paloalto Networks XSIAM-Analyst exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Paloalto Networks XSIAM-Analyst Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Paloalto Networks XSIAM-Analyst exam dumps to enhance your readiness for the exam.
Like any other Paloalto Networks Certification exam, the Security Operations is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do XSIAM-Analyst exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The XSIAM-Analyst Paloalto Networks exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Paloalto Networks XSIAM-Analyst exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Paloalto Networks has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Paloalto Networks changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



