The PECB Certified ISO/IEC 27001 2022 Lead Auditor exam (ISO-IEC-27001-Lead-Auditor)
Passing PECB ISO 27001 exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard ISO-IEC-27001-Lead-Auditor Dumps
In 2026, PECB uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official PECB ISO-IEC-27001-Lead-Auditor Exam Domains
Our curriculum is meticulously mapped to the PECB official blueprint.
Fundamental Principles and Concepts of ISMS (0%)
Master the basic definitions and principles of Information Security Management Systems. Focus on the Confidentiality, Integrity, and Availability (CIA) triad and the relationship between ISO/IEC 27001, ISO/IEC 27002, and other regulatory frameworks.
Information Security Management System (ISMS) Requirements (0%)
Deep dive into the mandatory clauses (4 to 10) of ISO/IEC 27001. Master the requirements for the context of the organization, leadership, planning, support, operation, performance evaluation, and continual improvement.
Fundamental Audit Concepts and Principles (0%)
Understanding the auditing process based on ISO 19011 guidelines. Focus on the audit criteria, evidence-based approach, confidentiality, and the principles of auditor independence and professional integrity.
Preparation of an ISO/IEC 27001 Audit (0%)
Mastering the "Stage 1" audit process. Focus on defining the audit scope, objectives, and criteria. Learn how to perform a document review, develop an audit plan, and create effective audit work documents (checklists).
Conducting an ISO/IEC 27001 Audit (0%)
The core "Stage 2" audit activities. Master conducting opening meetings, collecting and verifying audit evidence, and identifying and documenting non-conformities. Focus on interview techniques and professional communication.
Closing an ISO/IEC 27001 Audit (0%)
Mastering the finalization of the audit. Focus on evaluating audit findings, drafting audit conclusions, conducting closing meetings, and preparing the final audit report. Includes the evaluation of corrective action plans.
Managing an ISO/IEC 27001 Audit Program (0%)
Focus on the strategic management of internal and external audit programs. Master the application of the PDCA cycle to the audit program, managing resources, and ensuring the program's objectives align with the organization's goals.
PECB ISO-IEC-27001-Lead-Auditor Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
After completing Stage 1 and in preparation for a Stage 2 initial certification audit, the auditee informs the audit team leader that they wish to extend the audit scope to include two additional sites that have recently been acquired by the organisation.
Considering this information, what action would you expect the audit team leader to take?
Correct Answer & Rationale:
Answer: B
Explanation:
According to ISO/IEC 17021-1, which specifies the requirements for bodies providing audit and certification of management systems, a certification body should establish criteria for determining audit time and audit team composition based on factors such as the scope of certification, size and complexity of the organization, risks associated with its activities, etc2. Therefore, if an auditee requests to extend the audit scope to include two additional sites after completing Stage 1 of an initial certification audit, the audit team leader should obtain information about the additional sites to inform the certification body, so that they can review and approve the change in scope and adjust the audit time and audit team accordingly2. The other options are not appropriate actions for the audit team leader to take in this situation. For example, increasing the length of the Stage 2 audit to include the extra sites without informing the certification body may violate their procedures and policies; arranging to complete a remote Stage 1 audit of the two sites using a video conferencing platform may not be feasible or effective depending on the nature and location of the sites; and informing the auditee that the request can be accepted but a full Stage 1 audit must be repeated may not be necessary or reasonable if there are no significant changes in the auditee’s ISMS since Stage 12. References: ISO/IEC 17021-1:2015 - Conformity assessment – Requirements for bodies providing audit and certification of management systems – Part 1: Requirements
QUESTION DESCRIPTION:
Review the following statements and determine which two are false:
Correct Answer & Rationale:
Answer: C, F
Explanation:
The number of days assigned to a third-party audit is not determined by the auditee’s availability, but by the audit program, which considers the audit scope, objectives, criteria, risks, and resources12. The auditee’s availability is only one factor that affects the audit planning and scheduling, but not the audit duration3. Auditors approved for conducting onsite audits do require additional training for virtual audits, as there are significant differences in the skillset required. Virtual audits pose different challenges and opportunities than onsite audits, such as communication, technology, security, and evidence collection4 . Auditors need to be familiar with the tools and techniques for conducting remote audits, as well as the ethical and professional behavior expected in a virtual environment . References:
PECB Candidate Handbook - ISO 27001 Lead Auditor, page 18
ISO 19011:2018, Guidelines for auditing management systems, clause 5.3.2
ISO 19011:2018, Guidelines for auditing management systems, clause 6.3.1
Deloitte - Conducting a Virtual Internal Audit, page 1
[A Guide to Conducting Effective and Efficient Remote Audits], page 1
[ISO 19011:2018, Guidelines for auditing management systems], clause 7.2.3
[Remote Auditing Best Practices & Checklist for Regulatory Compliance], page 1
QUESTION DESCRIPTION:
Scenario 9: Techmanic is a Belgian company founded in 1995 and currently operating in Brussels. It provides IT consultancy, software design, and hardware/software services, including deployment and maintenance. The company serves sectors like public services, finance, telecom, energy, healthcare, and education. As a customer-centered company, it prioritizes strong client relationships and leading security practices.
Techmanic has been ISO/IEC 27001 certified for a year and regards this certification with pride. During the certification audit, the auditor found some inconsistencies in its ISMS implementation. Since the observed situations did not affect the capability of its ISMS to achieve the intended results, Techmanic was certified after auditors followed up on the root cause analysis and corrective actions remotely During that year, the company added hosting to its list of services and requested to expand its certification scope to include that area The auditor in charge approved the request and notified Techmanic that the extension audit would be conducted during the surveillance audit
Techmanic underwent a surveillance audit to verify its iSMS ' s continued effectiveness and compliance with ISO/IEC 27001. The surveillance audit aimed to ensure that Techmanic’s security practices, including the recent addition of hosting services, aligned seamlessly with the rigorous requirements of the certification
The auditor strategically utilized the findings from previous surveillance audit reports in the recertification activity with the purpose of replacing the need for additional recertification audits, specifically in the IT consultancy sector. Recognizing the value of continual improvement and learning from past assessments. Techmanic implemented a practice of reviewing previous surveillance audit reports. This proactive approach not only facilitated identifying and resolving potential nonconformities but also aimed to streamline the recertification process in the IT consultancy sector.
During the surveillance audit, several nonconformities were found. The ISMS continued to fulfill the ISO/IEC 27001*s requirements, but Techmanic failed to resolve the nonconformities related to the hosting services, as reported by its internal auditor. In addition, the internal audit report had several inconsistencies, which questioned the independence of the internal auditor during the audit of hosting services. Based on this, the extension certification was not granted. As a result. Techmanic requested a transfer to another certification body. In the meantime, the company released a statement to its clients stating that the ISO/IEC 27001 certification covers the IT services, as well as the hosting services.
Based on the scenario above, answer the following question:
Question:
What action should be taken regarding Techmanic’s certification?
Correct Answer & Rationale:
Answer: A
Explanation:
Comprehensive and Detailed In-Depth Explanation:
A. Correct Answer:
Techmanic misrepresented its certification scope, which is a violation of ISO certification rules.
Suspension allows time for corrective action before withdrawal is considered.
B. Incorrect:
Certification withdrawal is only necessary if corrective actions fail after suspension.
C. Incorrect:
Transfer does not resolve misrepresentation issues.
Relevant Standard Reference:
ISO/IEC 17021-1:2015 Clause 9.6.5 (Certification Suspension and Misrepresentation Issues)
QUESTION DESCRIPTION:
Scenario 2
Knight is an electronics company based in Northern California, the US that develops video game consoles. With over 300 employees globally, Knight is celebrating its fifth anniversary by launching the G-Console, a next-generation gaming system aimed at international markets. G-Console is considered to be the ultimate media machine of 2021, and it will give players the best gaming experience. The console pack will include a pair of VR headsets, two games, and other gifts.
Over the years, the company has developed a strong reputation for integrity, honesty, and respect toward their customers. Besides being a very customer-oriented company, Knight also gained wide recognition within the gaming industry because of its quality.
As one of the leading video game console developers in the world, Knight often finds itself a target for malicious activities. Therefore, it has implemented an information security management system (ISMS) based on ISO/IEC 27001, and its scope was communicated to employees of the company over a weekly meeting.
Recently, however, Knight experienced a security breach when hackers leaked proprietary information. In response, the incident response team (IRT) immediately began a thorough investigation of the system and the specifics of the incident. Initially, the IRT suspected that employees may have used weak passwords, allowing hackers to easily access their accounts. Upon further investigation, it was revealed that the hackers captured traffic from the file transfer protocol (FTP), which transmits data using clear-text passwords for authentication.
In light of this security incident, and following the IRT’s recommendations, Knight decided to replace the FTP with Secure Shell (SSH) protocol. This change ensures that any captured traffic is encrypted, significantly improving security.
After implementing these changes, Knight conducted a risk assessment to verify that the implementation of controls had minimized the risk of similar incidents. Based on the results of the risk assessment, they chose a risk treatment option to treat the risk.
Question
According to Scenario 2, the ISMS scope was communicated to Knight’s employees at the weekly meeting. Is this acceptable?
Correct Answer & Rationale:
Answer: B
Explanation:
ISO/IEC 27001:2022 requires that the scope of the ISMS be established and maintained as documented information. This requirement is explicitly stated in clause 4.3, which requires organizations to determine the boundaries and applicability of the ISMS and to ensure that the scope is documented. While communication and awareness are important, verbal communication alone is not sufficient to meet this requirement.
In the scenario, Knight communicated the ISMS scope to employees during a weekly meeting. While this may support awareness, it does not satisfy the requirement for documented information. Employees, auditors, and other interested parties must be able to access the ISMS scope consistently over time, including new employees or external stakeholders. Relying on meetings creates a risk that the scope is misunderstood, forgotten, or inconsistently applied.
Option A is incorrect because documenting meeting minutes does not replace the requirement for a formally controlled ISMS scope document. The scope must exist independently as documented information, not merely as a record of communication. Option C is also incorrect because ISO/IEC 27001 does not mandate formal training sessions as the only acceptable communication method for scope awareness.
Therefore, the correct position is that while communicating the scope verbally is useful, it is not acceptable on its own, and the scope must be maintained as documented information.
QUESTION DESCRIPTION:
You are performing an ISMS audit at a residential nursing home that provides healthcare services. The next step in your audit plan is to verify the information security incident management process. The IT Security Manager presents the information security incident management procedure and explains that the process is based on ISO/IEC 27035-1:2016.
You review the document and notice a statement " any information security weakness, event, and incident should be reported to the Point of Contact (PoC) within 1 hour after identification " . When interviewing staff, you found that there were differences in the understanding of the meaning of " weakness, event, and incident " .
You sample incident report records from the event tracking system for the last 6 months with summarized results in the following table.
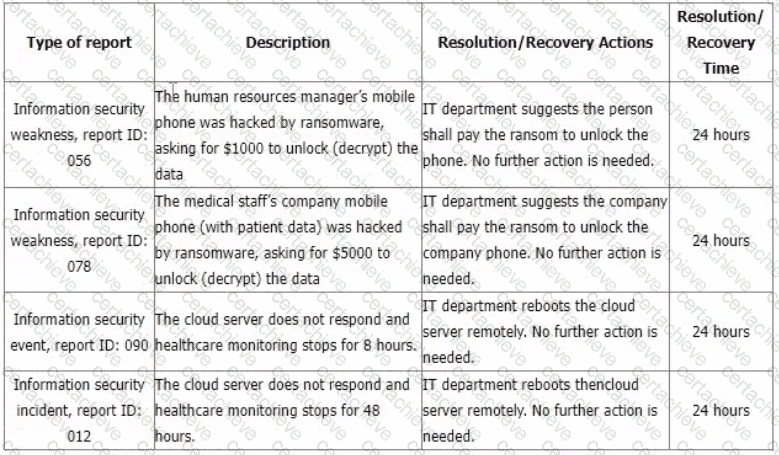
You would like to further investigate other areas to collect more audit evidence. Select two options that will not be in your audit trail.
Correct Answer & Rationale:
Answer: B, G
Explanation:
According to ISO/IEC 27001:2022, which specifies the requirements for establishing, implementing, maintaining and continually improving an information security management system (ISMS), clause 4.2 requires an organization to determine the needs and expectations of interested parties that are relevant to its ISMS1. This includes identifying the legal, regulatory, contractual and other requirements that apply to its information security activities1. Therefore, collecting more evidence on what the service requirements of healthcare monitoring are may not be relevant to verifying the information security incident management process, as it is not directly related to the audit objective or criteria. This option will not be in the audit trail.
QUESTION DESCRIPTION:
The auditor used sampling to ensure that event logs recording information security events are maintained and regularly reviewed. Sampling was based on the audit objectives, whereas the sample selection process was based on the probability theory. What type of sampling was used?
Correct Answer & Rationale:
Answer: A
Explanation:
The use of probability theory in the sample selection process indicates that " statistical sampling " was used. Statistical sampling allows auditors to make inferences about the population based on the properties of the sample, relying on the principles of probability to select representative elements.
QUESTION DESCRIPTION:
Scenario 6
Sinvestment is an insurance provider that offers a wide range of coverage options, including home, commercial, and life insurance. Originally established in North California, the company has expanded its operations to other locations, including Europe and Africa. In addition to its growth, Sinvestment is committed to complying with laws and regulations applicable to its industry and preventing any information security incident. They have implemented an information security management system (ISMS) based on ISO/IEC 27001 and have applied for certification.
A team of auditors was assigned by the certification body to conduct the audit. After signing a confidentiality agreement with Sinvestment, they started the audit activities. For the activities of the stage 1 audit, it was decided that they would be performed on site, except the review of documented information, which took place remotely, as requested by Sinvestment.
The audit team started the stage 1 audit by reviewing the documentation required, including the declaration of the ISMS scope, information security policies, and internal audit reports. The evaluation of the documented information was based on the content and procedure for managing the documented information.
In addition, the auditors found out that the documentation related to information security training and awareness programs was incomplete and lacked essential details. When asked, Sinvestment’s top management stated that the company has provided information security training sessions to all employees.
The stage 2 audit was conducted three weeks after the stage 1 audit. The audit team observed that the marketing department (not included in the audit scope) had no procedures to control employees’ access rights. Since controlling employees ' access rights is one of the ISO/IEC 27001 requirements and was included in the company ' s information security policy, the issue was included in the audit report.
Question
Based on Scenario 6, what methods did the audit team use for evidence collection and analysis during the audit of Sinvestment ' s ISMS?
Correct Answer & Rationale:
Answer: A
Explanation:
The audit team used documented information review and observation for evidence collection and evaluation for analysis, making option A the correct answer. This aligns directly with ISO 19011, which identifies document review, observation, and evaluation as primary audit techniques.
In the scenario, auditors reviewed ISMS documentation remotely, observed departmental practices during stage 2, and evaluated whether controls such as access rights management and training documentation met ISO/IEC 27001 requirements. These activities constitute classic evidence-based auditing methods.
Option B is incorrect because there is no indication that technical verification or extensive sampling of systems occurred. Option C is incorrect because the audit did not rely solely on interviews, nor was trend analysis the primary analytical method used. Interviews were supplementary, not exclusive.
ISO auditing requires auditors to triangulate evidence using multiple methods. The combination of document review, observation, and evaluative analysis reflects appropriate and recommended audit practice.
QUESTION DESCRIPTION:
How does the use of new technologies such as big data impact auditing?
Correct Answer & Rationale:
Answer: A
Explanation:
The use of new technologies such as big data presents new challenges in auditing, particularly the issue of combining structured and unstructured data. Big data environments often include diverse data sets that auditors need to understand and interpret, which requires new skills and approaches to ensure effective and comprehensive audit coverage.
QUESTION DESCRIPTION:
You are an experienced ISMS audit team leader. You are providing an introduction to ISO/IEC 27001:2022 to a class of Quality Management System Auditors who are seeking to retrain to enable them to carry out information security management system audits.
You ask them which of the following characteristics of information does an information security management system seek to preserve?
Which three answers should they provide?
Correct Answer & Rationale:
Answer: E, F, G
Explanation:
These three characteristics are the fundamental properties of information security, as defined by the ISO/IEC 27000 standard, which provides the overview and vocabulary of information security, cybersecurity, and privacy protection12. They are also the basis for the information security objectives and controls of the ISO/IEC 27001 standard, which specifies the requirements for establishing, implementing, maintaining, and continually improving an information security management system34. The definitions of these characteristics are as follows12:
•Availability: The property of being accessible and usable upon demand by an authorized entity.
•Confidentiality: The property that information is not made available or disclosed to unauthorized individuals, entities, or processes.
•Integrity: The property of safeguarding the accuracy and completeness of information and processing methods.
The other characteristics listed in the question, such as clarity, accessibility, completeness, importance, and efficiency, are not directly related to information security, although they may be relevant for other aspects of information management, such as quality, usability, or performance.
QUESTION DESCRIPTION:
Scenario 2: Knight is an electronics company from Northern California, US that develops video game consoles. Knight has more than 300 employees worldwide. On the
fifth anniversary of their establishment, they have decided to deliver the G-Console, a new generation video game console aimed for worldwide markets. G-Console is
considered to be the ultimate media machine of 2021 which will give the best gaming experience to players. The console pack will include a pair of VR headset, two
games, and other gifts.
Over the years, the company has developed a good reputation by showing integrity, honesty, and respect toward their customers. This good reputation is one of the
reasons why most passionate gamers aim to have Knight ' s G-console as soon as it is released in the market. Besides being a very customer-oriented company, Knight
also gained wide recognition within the gaming industry because of the developing quality. Their prices are a bit higher than the reasonable standards allow.
Nonetheless, that is not considered an issue for most loyal customers of Knight, as their quality is top-notch.
Being one of the top video game console developers in the world, Knight is also often the center of attention for malicious activities. The company has had an
operational ISMS for over a year. The ISMS scope includes all departments of Knight, except Finance and HR departments.
Recently, a number of Knight ' s files containing proprietary information were leaked by hackers. Knight ' s incident response team (IRT) immediately started to analyze
every part of the system and the details of the incident.
The IRT ' s first suspicion was that Knight ' s employees used weak passwords and consequently were easily cracked by hackers who gained unauthorized access to their
accounts. However, after carefully investigating the incident, the IRT determined that hackers accessed accounts by capturing the file transfer protocol (FTP) traffic.
FTP is a network protocol for transferring files between accounts. It uses clear text passwords for authentication.
Following the impact of this information security incident and with IRT ' s suggestion, Knight decided to replace the FTP with Secure Shell (SSH) protocol, so anyone
capturing the traffic can only see encrypted data.
Following these changes, Knight conducted a risk assessment to verify that the implementation of controls had minimized the risk of similar incidents. The results of
the process were approved by the ISMS project manager who claimed that the level of risk after the implementation of new controls was in accordance with the
company ' s risk acceptance levels.
Based on this scenario, answer the following question:
Based on scenario 2, the ISMS project manager approved the results of risk assessment. Is this acceptable?
Correct Answer & Rationale:
Answer: A
Explanation:
In the context of ISO/IEC 27001, the approval of the risk assessment and the acceptance of the remaining risk levels after treatment are typically responsibilities of the top management. This is because top management is accountable for the information security management system and its outcomes, and they have the authority to accept risks on behalf of the organization12. References: = The information provided is based on the standard practices of ISO/IEC 27001 risk assessment and treatment processes, which emphasize the role of top management in the approval and acceptance of risks
A Stepping Stone for Enhanced Career Opportunities
Your profile having ISO 27001 certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in PECB ISO-IEC-27001-Lead-Auditor certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace PECB Exam ISO-IEC-27001-Lead-Auditor
Achieving success in the ISO-IEC-27001-Lead-Auditor PECB exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in ISO-IEC-27001-Lead-Auditor certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam ISO-IEC-27001-Lead-Auditor!
In the backdrop of the above prep strategy for ISO-IEC-27001-Lead-Auditor PECB exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding ISO-IEC-27001-Lead-Auditor exam prep. Here's an overview of Certachieve's toolkit:
PECB ISO-IEC-27001-Lead-Auditor PDF Study Guide
This premium guide contains a number of PECB ISO-IEC-27001-Lead-Auditor exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of PECB ISO-IEC-27001-Lead-Auditor study guide pdf free download is also available to examine the contents and quality of the study material.
PECB ISO-IEC-27001-Lead-Auditor Practice Exams
Practicing the exam ISO-IEC-27001-Lead-Auditor questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces PECB ISO-IEC-27001-Lead-Auditor Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
PECB ISO-IEC-27001-Lead-Auditor exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning ISO-IEC-27001-Lead-Auditor exam dumps can increase not only your chances of success but can also award you an outstanding score.
PECB ISO-IEC-27001-Lead-Auditor ISO 27001 FAQ
There are only a formal set of prerequisites to take the ISO-IEC-27001-Lead-Auditor PECB exam. It depends of the PECB organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you PECB ISO-IEC-27001-Lead-Auditor exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using PECB ISO-IEC-27001-Lead-Auditor Testing Engine.
Finally, it should also introduce you to the expected questions with the help of PECB ISO-IEC-27001-Lead-Auditor exam dumps to enhance your readiness for the exam.
Like any other PECB Certification exam, the ISO 27001 is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do ISO-IEC-27001-Lead-Auditor exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The ISO-IEC-27001-Lead-Auditor PECB exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the PECB ISO-IEC-27001-Lead-Auditor exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. PECB has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If PECB changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



