The BIG-IP Administration Data Plane Configuration (F5CAB3) exam (F5CAB3)
Passing F5 F5-CA exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard F5CAB3 Dumps
In 2026, F5 uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
F5 F5CAB3 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
Refer to the exhibit.
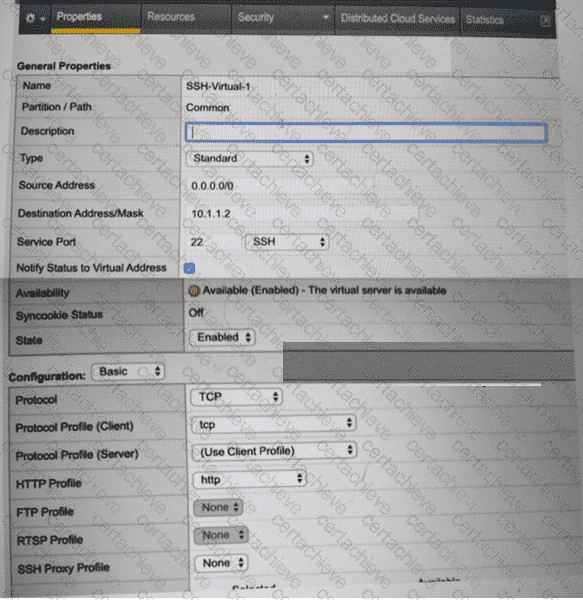
A BIG-IP Administrator creates a new Virtual Server to load balance SSH traffic. Users are unable to log on to the servers.
What should the BIG-IP Administrator do to resolve the issue? (Choose one answer)
Correct Answer & Rationale:
Answer: D
Explanation:
SSH is a Layer 4 TCP-based protocol that operates on TCP port 22 and does not use HTTP in any capacity. In the exhibit, the Virtual Server is configured with an HTTP Profile applied, which is inappropriate for SSH traffic and causes connection failures.
According to the BIG-IP Administration: Data Plane Configuration documentation:
An HTTP profile must only be applied to Virtual Servers handling HTTP or HTTPS traffic.
When an HTTP profile is attached, BIG-IP expects HTTP headers and attempts to parse application-layer data.
Non-HTTP protocols such as SSH, FTP (control), SMTP, and other raw TCP services will fail if an HTTP profile is enabled.
Why the other options are incorrect:
A. Set Protocol to UDPSSH uses TCP, not UDP. Changing the protocol would break SSH entirely.
B. Set Source Address to 10.1.1.2The source address setting controls client access restrictions and is unrelated to protocol parsing issues.
C. Set Destination Address/Mask to 0.0.0.0/0The destination address is already valid for a specific SSH service and does not impact protocol handling.
Correct Resolution:
The BIG-IP Administrator should remove the HTTP Profile (set it to None) so the Virtual Server functions as a pure Layer 4 TCP service, allowing SSH connections to pass through successfully.
QUESTION DESCRIPTION:
Exhibit:
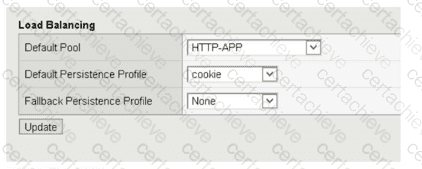
Due to a change in application requirements, a BIG-IP Administrator needs to modify the configuration of a Virtual Server to include a Fallback Persistence Profile. Which persistence profile type should the BIG-IP Administrator use for this purpose?
Correct Answer & Rationale:
Answer: B
Explanation:
In a BIG-IP environment, a Fallback Persistence Profile is utilized as a secondary " stickiness " mechanism when the primary (Default) persistence method fails to provide a valid persistence record. For example, if a Virtual Server uses HTTP Cookie Persistence as its primary method, but a client’s browser has cookies disabled, the BIG-IP will be unable to find a persistence cookie in the request. Without a fallback method, the system would treat every request from that client as a new, independent connection, potentially breaking the application session.
Source Address Affinity (also known as Source Address Persistence) is the most common and standard choice for a fallback profile. It operates at the network layer (Layer 3) by tracking the client’s source IP address. Because every IP packet contains a source address, this method is virtually guaranteed to work even when application-layer data (like Cookies or SSL Session IDs) is missing or encrypted beyond the BIG-IP ' s visibility. While Universal (Option A) and Hash (Option D) profiles are highly flexible and can use iRules to persist on almost any data, they require specific configuration and logic that may not always be present or valid. SSL persistence (Option C) relies on the SSL Session ID, which frequently changes due to modern browser security practices (session renegotiation), making it less reliable than Source Address Affinity. By configuring Source Address Affinity as the fallback, the administrator ensures that the BIG-IP has a " safety net " to maintain session integrity based on the client ' s IP address when the more granular cookie-based persistence is unavailable.
QUESTION DESCRIPTION:
How will the BIG-IP system distribute the traffic based on the configuration below?
pool my_pool {
lb_mode fastest
min_active_members 2
member 10.12.10.7:80 priority 3
member 10.12.10.8:80 priority 3
member 10.12.10.9:80 priority 3
member 10.12.10.4:80 priority 2
member 10.12.10.5:80 priority 2
member 10.12.10.6:80 priority 2
member 10.12.10.1:80 priority 1
member 10.12.10.2:80 priority 1
member 10.12.10.3:80 priority 1
}
(Pick the 2 correct responses below)
Correct Answer & Rationale:
Answer: A, C
Explanation:
The configuration provided utilizes Priority Group Activation in conjunction with the min_active_members setting. Priority groups allow an administrator to define primary servers and " backup " servers within the same pool. The BIG-IP prioritizes traffic based on the assigned priority number, with the highest number receiving traffic first.
In this specific configuration, the priority 3 group is the primary group. Therefore, connections are first distributed to all pool members with priority 3 as long as they are available. The system will continue to use only the priority 3 group unless the number of available members in that group falls below the min_active_members value, which is set to 2.
If the priority 3 group has fewer than two active members, the BIG-IP " activates " the next available priority group (priority 2) and distributes traffic among the remaining members of priority 3 and all members of priority 2. This cascading logic continues down the list. Consequently, if both the priority 3 group and the priority 2 group have fewer than two members available, traffic is directed to the priority 1 group. This ensures that even in a multi-server failure scenario, the system has a last-resort group of servers to handle the traffic.
Option D is incorrect because if only one member of priority 3 goes down, there are still two members active (10.12.10.8 and 10.12.10.9). Since 2 is not less than the min_active_members threshold of 2, the priority 2 group will not yet be activated. Option B is incorrect because traffic flows from high priority to low priority, not the other way around.
QUESTION DESCRIPTION:
Users are unable to reach an application. The Virtual Server shows a red diamond status in the Configuration Utility.
What is the cause?
Correct Answer & Rationale:
Answer: A
Explanation:
A red diamond indicates the Virtual Server is enabled but unavailable due to all pool members being down.
QUESTION DESCRIPTION:
A virtual server is configured to offload SSL from a pool of backend servers. When users connect to the virtual server, they successfully establish an SSL connection but no content is displayed. A packet trace performed on the server shows that the server receives and responds to the request. What should a BIG-IP Administrator do to resolve the problem? (Choose one answer)
Correct Answer & Rationale:
Answer: D
Explanation:
This scenario describes a classic case of asymmetric routing in a " one-arm " or non-gateway deployment. When a BIG-IP system is configured for SSL offloading, the following traffic flow occurs:
Client-Side: The client establishes a successful SSL/TLS handshake with the Virtual Server. This explains why the user can " successfully establish an SSL connection. "
Server-Side: The BIG-IP decrypts the traffic and forwards it as plain HTTP to the backend server. The packet trace confirms the server receives the HTTP GET request and responds with the content.
The Routing Failure: By default, the BIG-IP system preserves the client ' s original source IP address. If the backend server ' s default gateway is not the BIG-IP system (or if the server is on the same subnet as the client), the server will attempt to send the response directly back to the client ' s IP address, bypassing the BIG-IP.
Stateful Drop: Because the BIG-IP is a Full Proxy, it expects the response to return through its own internal state table to be encrypted and sent back to the client. Since the response bypasses the BIG-IP, the BIG-IP connection eventually times out, and the client receives no data despite the server having sent it.
Solution (SNAT): Enabling Secure Network Address Translation (SNAT), specifically SNAT Auto Map, ensures that the BIG-IP replaces the client ' s source IP with its own internal self-IP before sending the request to the server. This forces the server to send the response back to the BIG-IP, allowing the BIG-IP to complete the transaction and deliver the content to the user.
QUESTION DESCRIPTION:
What is the status of a pool member when manual resume is enabled and a health check first fails and then passes?
Correct Answer & Rationale:
Answer: A
Explanation:
With manual resume enabled, BIG-IP does not automatically return a pool member to service after recovery. The member remains offline until manually re-enabled.
QUESTION DESCRIPTION:
A BIG-IP Administrator configures a Virtual Server to load balance traffic between 50 webservers for an ecommerce website. Traffic is being load balanced using the Least Connections (node) method. The webserver administrators report that customers are losing the contents from their shopping carts and are unable to complete their orders. What should the BIG-IP Administrator do to resolve the issue?
Correct Answer & Rationale:
Answer: A
Explanation:
The issue of " lost shopping carts " in an ecommerce environment is a classic symptom of a missing or improperly configured Persistence Profile. In modern web applications, session data—such as items added to a cart—is often stored locally on the specific web server that initially handled the user ' s request. If the BIG-IP system load balances a user ' s subsequent request (like clicking " Checkout " ) to a different server among the 50 webservers, the new server will not have the session data, and the user will appear to have an empty cart.
While Least Connections (node) is an efficient load balancing algorithm, it makes a new decision for every connection unless persistence is enabled. To resolve this, the administrator must implement a persistence mechanism. HTTP Cookie Persistence (Option A) is the industry standard for web applications. By assigning a cookie persistence profile to the Virtual Server, the BIG-IP inserts a unique cookie into the HTTP response. When the user ' s browser returns that cookie in future requests, the BIG-IP identifies the specific server that handled the first request and consistently directs the user back to that same server for the duration of their session.
Sip_info (Option B) is a persistence method for VOIP traffic and is not applicable to web traffic. Ratio load balancing (Options C and D) merely changes the distribution frequency but still does not guarantee that a specific user will stay on the same server across multiple requests. Therefore, adding a cookie persistence profile is the direct procedural fix to maintain session state and ensure ecommerce functionality.
QUESTION DESCRIPTION:
A Standard Virtual Server reports poor network performance for Internet-based clients.
What configuration should be applied?
Correct Answer & Rationale:
Answer: A
Explanation:
WAN TCP profiles are optimized for high latency and packet loss typical of Internet clients, while LAN profiles are ideal for backend servers.
QUESTION DESCRIPTION:
A BIG-IP Administrator creates a new Virtual Server. The end user is unable to access the page. During troubleshooting, the administrator learns that the connection between the BIG-IP system and server is NOT set up correctly. What should the administrator do to solve this issue? (Choose one answer)
Correct Answer & Rationale:
Answer: D
Explanation:
The issue described is a classic symptom of asymmetric routing, which frequently occurs when the BIG-IP system and the back-end servers reside on the same subnet (often referred to as a " one-arm " deployment).
The Routing Problem: By default, the BIG-IP system preserves the original client source IP address when forwarding traffic to a pool member. If the server is in the same subnet as the client or if the server ' s default gateway is not the BIG-IP, the server will attempt to send its response directly back to the client’s IP address, bypassing the BIG-IP.
Stateful Failure: Since the BIG-IP is a Full Proxy, it maintains a state table. Because the response packet never returns through the BIG-IP, the system cannot complete the three-way handshake or manage the application session, resulting in a connection failure for the user.
The Solution (SNAT): Enabling Source Network Address Translation (SNAT) solves this by changing the source IP address of the request to an IP address owned by the BIG-IP (typically a self-IP).
Requirement for Subnet Alignment: To ensure the server sends the response back to the BIG-IP, the translation address must be reachable. By using a self-IP configured in the same subnet as the servers, the BIG-IP ensures that the server sees the request coming from a local " neighbor. " The server will then naturally send the response back to that self-IP, allowing the BIG-IP to translate the packet back and forward it to the client.
Why other options are incorrect:
A: Disabling address translation would ensure the server-side traffic uses the client IP, making asymmetric routing inevitable in this scenario.
B: This is technically contradictory; " Auto Map " specifically uses existing self-IPs and does not require or use a " SNAT pool " configuration.
C: While using a specific translation address can work, it does not inherently guarantee the Layer 2/Layer 3 reachability mentioned in the scenario as effectively as ensuring the self-IP is correctly placed in the server ' s subnet.
QUESTION DESCRIPTION:
The BIG-IP Administrator is investigating whether better TCP performance is possible for a virtual server.
Which built-in profile should be tried first? (Choose one answer)
Correct Answer & Rationale:
Answer: B
Explanation:
BIG-IP provides several built-in TCP profiles optimized for different traffic patterns and network conditions. When attempting to improve general TCP performance, the recommended starting point is f5-tcp-progressive.
According to the BIG-IP Administration: Data Plane Configuration documentation:
f5-tcp-progressive is designed as a balanced, general-purpose TCP optimization profile.
It dynamically adjusts TCP behavior to improve throughput and latency for most enterprise applications.
It is the recommended first-choice profile when tuning TCP performance before moving to more specialized profiles.
Why the other options are incorrect:
A. f5-tcp-legacyThis profile exists for backward compatibility and does not include modern TCP optimizations.
C. f5-tcp-mobileThis profile is optimized specifically for high-latency, lossy mobile networks and is not suitable for general-purpose environments.
D. No optionBIG-IP explicitly provides built-in TCP profiles for performance tuning; using none would forgo optimization opportunities.
Correct Resolution:
The administrator should first apply f5-tcp-progressive to evaluate potential TCP performance improvements before considering more specialized profiles.
A Stepping Stone for Enhanced Career Opportunities
Your profile having F5-CA certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in F5 F5CAB3 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace F5 Exam F5CAB3
Achieving success in the F5CAB3 F5 exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in F5CAB3 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam F5CAB3!
In the backdrop of the above prep strategy for F5CAB3 F5 exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding F5CAB3 exam prep. Here's an overview of Certachieve's toolkit:
F5 F5CAB3 PDF Study Guide
This premium guide contains a number of F5 F5CAB3 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of F5 F5CAB3 study guide pdf free download is also available to examine the contents and quality of the study material.
F5 F5CAB3 Practice Exams
Practicing the exam F5CAB3 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces F5 F5CAB3 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
F5 F5CAB3 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning F5CAB3 exam dumps can increase not only your chances of success but can also award you an outstanding score.
F5 F5CAB3 F5-CA FAQ
There are only a formal set of prerequisites to take the F5CAB3 F5 exam. It depends of the F5 organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you F5 F5CAB3 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using F5 F5CAB3 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of F5 F5CAB3 exam dumps to enhance your readiness for the exam.
Like any other F5 Certification exam, the F5-CA is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do F5CAB3 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The F5CAB3 F5 exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the F5 F5CAB3 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. F5 has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If F5 changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



