The Netskope Certified Cloud Security Administrator (NCCSA) (NSK101)
Passing Netskope NCCSA exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard NSK101 Dumps
In 2026, Netskope uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official Netskope NSK101 Exam Domains
Our curriculum is meticulously mapped to the Netskope official blueprint.
Cloud Architecture & Traffic Steering (0%)
The "Connection" foundation. Master the deployment of the Netskope platform. Focus on the various traffic steering methods, including Netskope Client, IPsec/GRE tunnels, and Proxy Auto-Configuration (PAC) files. In 2026, this domain emphasizes the "Clientless" approach for unmanaged devices and how to configure steering configurations that balance user experience with total visibility.
Cloud Access Security Broker (0%)
The "SaaS" core. Master the visibility and control of cloud applications. Focus on the distinction between Inline (Real-time) and API-based (Introspection) CASB. Learn to manage the "Cloud Confidence Index" (CCI) to assess the risk of thousands of apps and implement policies that block risky activities (like "Upload") while allowing productive ones (like "View") in unsanctioned applications.
Next-Gen Secure Web Gateway (0%)
The "Web" engine. Master the protection of users browsing the public internet. Focus on URL filtering, SSL/TLS decryption (and its privacy exceptions), and dynamic threat protection. Learn to utilize Advanced Threat Protection (ATP) to catch zero-day malware and how to configure "Web Isolation" for high-risk categories to prevent browser-based exploits.
Data Loss Prevention & Threat Protection (0%)
The "Data" layer. This is the heart of the Netskope value proposition. Master the creation of DLP profiles using Regular Expressions (RegEx), Fingerprinting, and Exact Data Match (EDM). In 2026, this domain includes AI-driven document classification and the enforcement of DLP across both web traffic and API-connected storage (e.g., Google Drive, OneDrive).
Netskope Private Access & Zero Trust (0%)
The "Access" domain. Master the transition from legacy VPNs to Zero Trust Network Access (ZTNA). Focus on the configuration of Netskope Private Access (NPA) to provide secure, application-level connectivity to private data center or public cloud resources. Learn to define "Publishers" and access policies that verify user identity and device posture before granting the "Least Privilege" access.
Monitoring, Reporting, and Troubleshooting (0%)
The "Visibility" domain. Master the diagnostic tools within the Netskope tenant. Focus on the SkopeIT dashboard for real-time event monitoring, creating custom reports for compliance audits, and troubleshooting traffic steering failures. Learn to interpret "Alerts" and "Events" to identify security gaps and optimize policy performance.
Netskope NSK101 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
Users are connecting to sanctioned cloud applications from public computers, such as from a hotel business center.
Which traffic steering method would work in this scenario?
Correct Answer & Rationale:
Answer: C
Explanation:
Reverse Proxy Overview:
A reverse proxy allows users to access sanctioned cloud applications securely from public or untrusted networks.
It ensures that the traffic is inspected and policy controls are enforced before reaching the cloud application.
Scenario Justification:
Users connecting from public computers, such as those in hotel business centers, cannot have a steering client installed, and IPsec/GRE tunnels are not feasible.
Proxy chaining requires control over the client ' s browser settings, which is not possible in this scenario.
A reverse proxy can handle the traffic without requiring configuration changes on the public computer.
Implementation:
Configure the reverse proxy to handle traffic for sanctioned applications.
Ensure the reverse proxy settings are enforced via your organization ' s security policies.
References:
Detailed configurations and use cases can be found in the Netskope documentation on reverse proxy solutions.
QUESTION DESCRIPTION:
You are attempting to allow access to an application using NPA. Private Apps steering is already enabled for all users.
In this scenario, which two actions are required to accomplish this task? (Choose two.)
Correct Answer & Rationale:
Answer: B, C
Explanation:
To allow access to an application using Netskope Private Access (NPA) with Private Apps steering already enabled for all users, follow these steps:
Create a Private App :
Go to the Netskope admin console.
Navigate to the Private Access section.
Create a new Private App by specifying the necessary details such as app name, IP address, ports, and protocols. This step is essential for defining the private application that users will access through NPA.
Create a Real-time Protection " Allow " Policy :
Navigate to the Policies section in the Netskope admin console.
Create a new Real-time Protection policy.
Set the policy action to " Allow " .
Define the criteria for the policy to match the traffic directed to the newly created Private App.
Apply the policy to the relevant users or groups to ensure that access to the Private App is allowed.
Ensure Other Required Settings :
Ensure that SSO (Single Sign-On) is properly configured if it is needed for user authentication.
Verify that Private App steering is enabled for all users, which might already be the case as per the scenario.
References :
Netskope API Documentation: Configuring Private Apps and Real-time Protection Policies.
By following these steps, you ensure that the private app is properly defined and that users are allowed to access it through the appropriate Real-time Protection policies. This approach leverages Netskope ' s capabilities to manage and secure access to private applications seamlessly.
QUESTION DESCRIPTION:
You need to create a service request ticket for a client-related issue using the Netskope client Ul. In this scenario, you generate the client logs by right-clicking on the system tray icon and choosing
Correct Answer & Rationale:
Answer: C
Explanation:
To create a service request ticket for a client-related issue using the Netskope client UI, you need to generate the client logs by right-clicking on the system tray icon and choosing Troubleshoot. This will open a window where you can select the option to Save Logs, which will create a zip file containing the client logs. You can then attach this file to your service request ticket and provide any relevant details about the issue. Choosing Save logs, Configuration, or Help will not generate the client logs, as they perform different functions, such as saving the current configuration, opening the settings menu, or opening the help page. References: [Netskope Client Troubleshooting].
QUESTION DESCRIPTION:
You are required to restrict cloud users from uploading data to any risky cloud storage service as defined by the Cloud Confidence Index. In the Netskope platform, which two policy elements would enable you to implement this control? (Choose two)
Correct Answer & Rationale:
Answer: B, D
Explanation:
To restrict cloud users from uploading data to risky cloud storage services as defined by the Cloud Confidence Index (CCI) in the Netskope platform, you would use the following policy elements:
Category : This policy element allows you to define and restrict actions based on the category of the cloud application. For example, you can categorize cloud storage services and create policies that restrict uploads to any application that falls under this category.
Cloud Confidence Level : This policy element leverages the Cloud Confidence Index (CCI), which rates the risk level of cloud applications. By using the Cloud Confidence Level, you can create policies that restrict uploads to applications with a low confidence level, thereby preventing data uploads to risky cloud storage services.
References :
Using the Netskope Knowledge Portal documentation, specifically under policy configuration and enforcement, which details how to use categories and Cloud Confidence Level in policy creation.
Postman collection and API documentation that describes the usage of these elements in the Netskope API.
=================
QUESTION DESCRIPTION:
Click the Exhibit button.
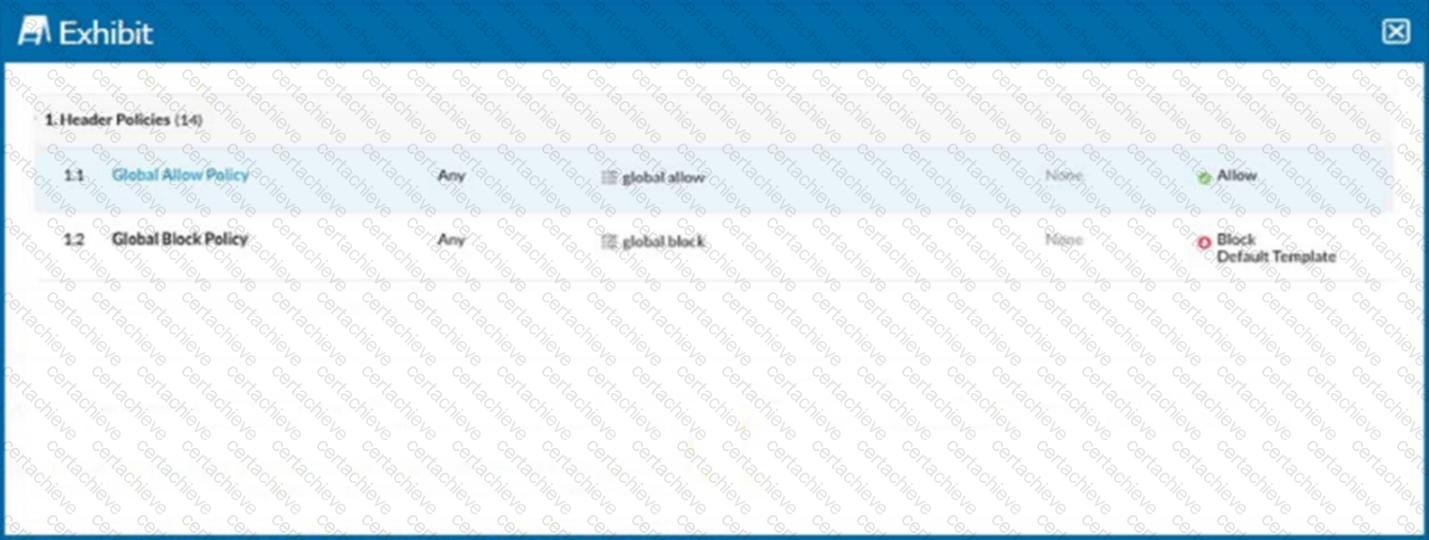
Referring to the exhibit, you have a user reporting that a blocked website is needed for legitimate business reasons. Upon review, you determine that the user has been blocked by the Global Block policy. You need to create an exception forthat domain. You create a custom URL list that includes the domain.
In this scenario, which two actions would allow this access? (Choose two.)
Correct Answer & Rationale:
Answer: B, C
Explanation:
Identify the Blocked Policy: According to the exhibit, the website is blocked by the " Global Block Policy. "
Create a Custom URL List: To create an exception for the domain, you need to first create a custom URL list that includes the domain in question.
Navigate to the URL List section in the Netskope UI.
Create a new URL list and add the domain that needs to be allowed.
Option B: Create a custom category with the custom URL list as an included URL list and add it to an allow policy above the Global Block policy.
Go to the Policy section in the Netskope UI.
Create a new policy, ensuring it is an " Allow " policy.
Add the custom category to this allow policy.
Position this allow policy above the Global Block policy to ensure it takes precedence.
This ensures that the URLs in the custom list are allowed before the Global Block policy is evaluated.
Option C: Add the custom URL list as an excluded URL list to the category in the Global Block policy.
Edit the existing Global Block policy.
Add the custom URL list to the excluded URL list section of this policy.
This will exclude the URLs in the custom list from being blocked by the Global Block policy.
References:
Refer to the Netskope Knowledge Portal for managing custom URL lists and policy configurations.
QUESTION DESCRIPTION:
Which two controls are covered by Netskope ' s security platform? (Choose two.)
Correct Answer & Rationale:
Answer: A, C
Explanation:
Netskope’s security platform covers two controls: ZTNA and CASB. ZTNA stands for Zero Trust Network Access, which is a solution that provides secure and granular access to private applications without exposing them to the internet or requiring VPNs. CASB stands for Cloud Access Security Broker, which is a solution that provides visibility and control over cloud services and web traffic, as well as data and threat protection for cloud users and devices. References: Netskope Platform Netskope ZTNA Netskope CASB
QUESTION DESCRIPTION:
Which two common security frameworks are used today to assess and validate a vendor ' s security practices? (Choose two.)
Correct Answer & Rationale:
Answer: B, C
Explanation:
The Building Security in Maturity Model (BSIMM) is a framework that measures and compares the security activities of different organizations. It helps organizations to assess their current security practices and identify areas for improvement. ISO 27001 is an international standard that specifies the requirements for establishing, implementing, maintaining, and improving an information security management system. It helps organizations to manage their information security risks and demonstrate their compliance with best practices. Data Science Council of America (DASCA) is not a security framework, but a credentialing body for data science professionals. NIST Cybersecurity Framework (NIST CSF) is a security framework, but it is not commonly used to assess and validate a vendor’s security practices, as it is more focused on improving the cybersecurity of critical infrastructure sectors in the United States. References: [BSIMM], [ISO 27001] , [DASCA], [NIST CSF] .
QUESTION DESCRIPTION:
Click the Exhibit button.
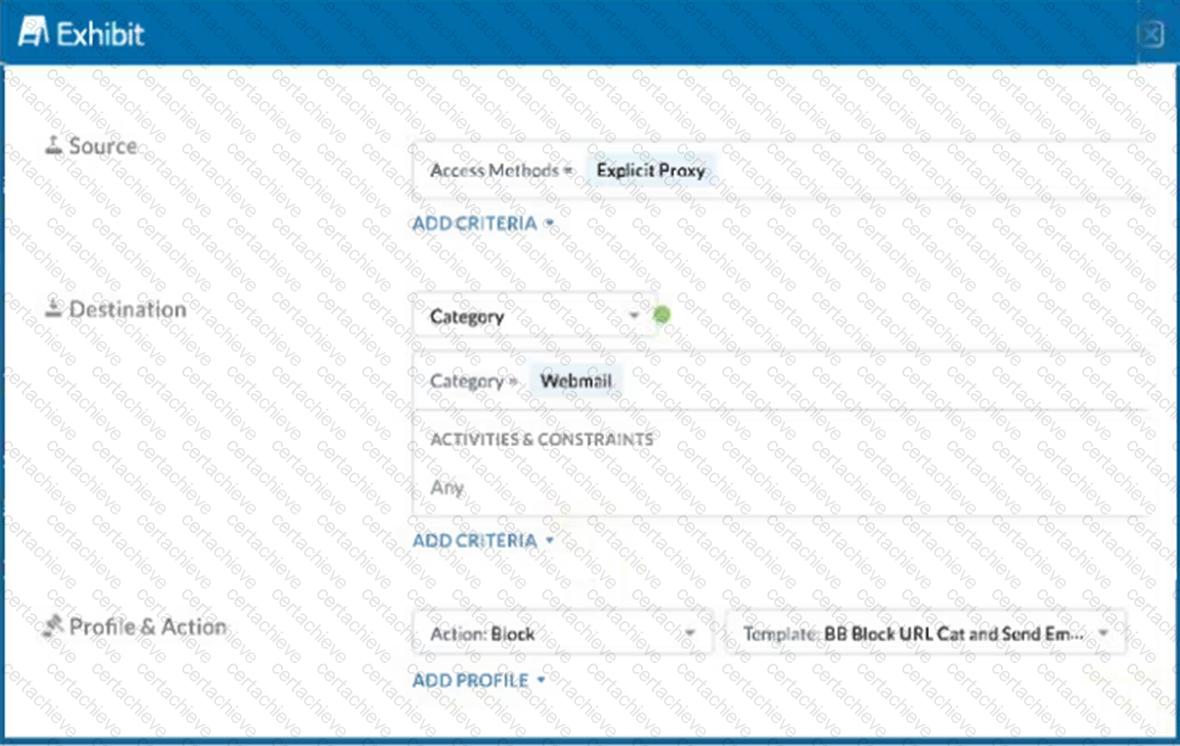
A user has the Netskope Client enabled with the correct steering configuration applied. The exhibit shows an inline policy that has a predefined webmail category blocked. However the user is still able to access Yahoo mail.
Which statement is correct in this scenario?
Correct Answer & Rationale:
Answer: C
Explanation:
The given exhibit shows an inline policy blocking the predefined webmail category via an explicit proxy. However, the user can still access Yahoo Mail, indicating that Yahoo Mail is not included in the webmail category when using an explicit proxy.
Policy Configuration:
The policy is set to block access to the webmail category through an explicit proxy.
The action for this policy is ' Block ' .
Understanding the Webmail Category:
Netskope ' s predefined categories may not always cover all services under a category, especially when it comes to specific configurations like explicit proxy.
The webmail category in the policy might not have included Yahoo Mail when using explicit proxy configurations.
Checking the Category Definitions:
It is important to verify what URLs or services are included under the " webmail " category in the Netskope administration console.
Administrators can check the category definitions and manually add Yahoo Mail if it ' s not included by default.
References:
REST API v2 Overview - Netskope Knowledge Portal
Using the REST API v2 dataexport Iterator Endpoints - Netskope Knowledge Portal
Using the REST API v2 UCI Impact Endpoints - Netskope Knowledge Portal
netskopesdk · PyPI
Netskope Rest APIv2(OAS 3.1) - Postman Collection
QUESTION DESCRIPTION:
Which two functions are available for both inline and API protection? (Choose two.)
Correct Answer & Rationale:
Answer: B, C
Explanation:
Netskope provides both inline and API protection for cloud applications and web traffic. Inline protection refers to the real-time inspection and enforcement of policies on the traffic between users and cloud applications, using Netskope’s inline proxy mode. API protection refers to the retrospective inspection and enforcement of policies on the data that is already stored in cloud applications, using Netskope’s API connectors. Two functions that are available for both inline and API protection are threat protection and DLP. Threat protection is the capability to detect and block malware, ransomware, phishing, and other cyber threats that may compromise cloud data or users. DLP is the capability to detect and protect sensitive data, such as personal information, intellectual property, or regulated data, that may be exposed or leaked through cloud applications. References: Netskope Inline Proxy Mode Netskope API Protection Netskope Threat Protection Netskope DLP Engine
QUESTION DESCRIPTION:
Click the Exhibit button.
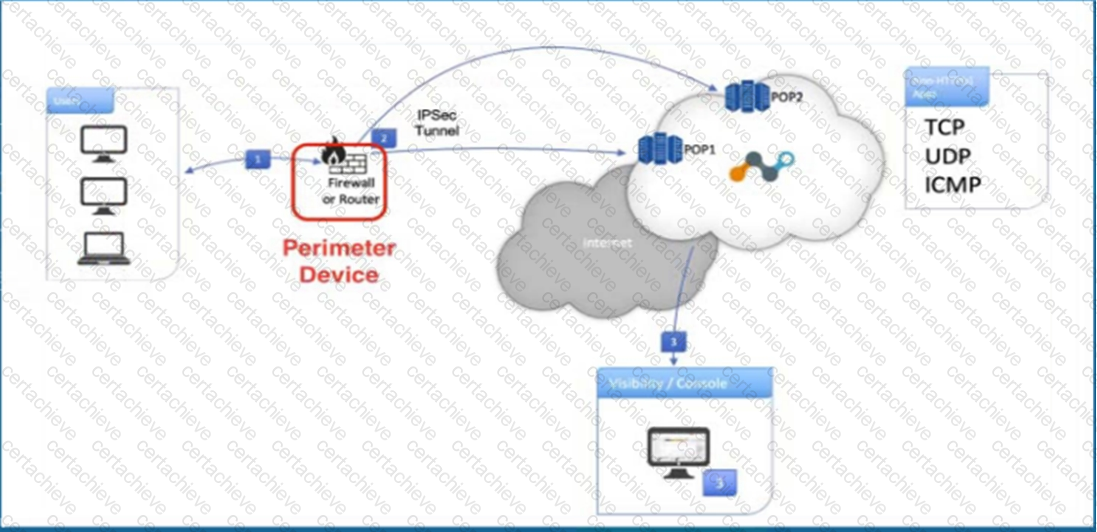
Referring to the exhibit, what are two recommended steps to be set on the perimeter device to monitor IPsec tunnels to a Netskope data plane? (Choose two.)
Correct Answer & Rationale:
Answer: A, B
Explanation:
To monitor IPsec tunnels to a Netskope data plane, it is essential to ensure the stability and responsiveness of the tunnels. The recommended steps involve enabling monitoring mechanisms that detect and respond to tunnel failures. Here’s a detailed explanation of the two recommended steps:
Enable IKE Dead Peer Detection (DPD) for each tunnel:
Explanation: IKE Dead Peer Detection (DPD) is a method used to detect if the peer (remote endpoint of the tunnel) is no longer available or reachable. By enabling DPD, the device can automatically detect and tear down the IPsec tunnel if the peer does not respond, allowing for quick re-establishment of the tunnel if needed.
Implementation: Configure DPD in the IPsec settings of the perimeter device. This ensures that if the Netskope data plane is unreachable, the tunnel is automatically terminated and re-negotiated.
Send ICMP requests to the Netskope location ' s Probe IP:
Explanation: Sending ICMP requests (ping) to the Netskope location ' s Probe IP helps in monitoring the availability and latency of the connection to the Netskope data plane. If the ICMP requests fail, it indicates a potential issue with the connectivity.
Implementation: Set up regular ICMP requests (ping) from the perimeter device to the Netskope Probe IPs. This allows for continuous monitoring of the tunnel’s health and immediate detection of connectivity issues.
References:
REST API v2 Overview - Netskope Knowledge Portal
Using the REST API v2 dataexport Iterator Endpoints - Netskope Knowledge Portal
Using the REST API v2 UCI Impact Endpoints - Netskope Knowledge Portal
A Stepping Stone for Enhanced Career Opportunities
Your profile having NCCSA certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Netskope NSK101 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Netskope Exam NSK101
Achieving success in the NSK101 Netskope exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in NSK101 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam NSK101!
In the backdrop of the above prep strategy for NSK101 Netskope exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding NSK101 exam prep. Here's an overview of Certachieve's toolkit:
Netskope NSK101 PDF Study Guide
This premium guide contains a number of Netskope NSK101 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Netskope NSK101 study guide pdf free download is also available to examine the contents and quality of the study material.
Netskope NSK101 Practice Exams
Practicing the exam NSK101 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Netskope NSK101 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Netskope NSK101 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning NSK101 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Netskope NSK101 NCCSA FAQ
There are only a formal set of prerequisites to take the NSK101 Netskope exam. It depends of the Netskope organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Netskope NSK101 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Netskope NSK101 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Netskope NSK101 exam dumps to enhance your readiness for the exam.
Like any other Netskope Certification exam, the NCCSA is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do NSK101 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The NSK101 Netskope exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Netskope NSK101 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Netskope has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Netskope changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



