The Implementing and Operating Cisco Security Core Technologies (SCOR 350-701) (350-701)
Passing Cisco CCNP Security exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard 350-701 Dumps
In 2026, Cisco uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official Cisco 350-701 Exam Domains
Our curriculum is meticulously mapped to the Cisco official blueprint.
Security Concepts (25%)
The highest-weighted domain. Master the high-level philosophy of defense. Focus on Zero Trust architecture, the CIA triad, and risk management. Learn to identify modern attack vectors (exfiltration, reconnaissance) and understand the role of AI/ML in automated threat detection and remediation.
Network Security (20%)
Deep dive into the infrastructure. Master the implementation of Cisco Secure Firewall (FTD/FMC), Next-Generation IPS, and Site-to-Site/Remote Access VPNs. Focus on network segmentation using TrustSec, NetFlow analysis for visibility, and securing the data plane and management plane.
Cloud Security (15%)
Focus on the borderless enterprise. Master Cisco Umbrella (DNS/SIG), Cloudlock (CASB), and securing public cloud workloads in AWS and Azure. Deep dive into the Cisco Secure Access (SSE) platform and how to implement secure web gateways in a decentralized environment.
Content Security (15%)
Mastering the delivery vectors. Focus on Cisco Secure Email (formerly ESA) and Secure Web Appliance (formerly WSA). Learn to configure anti-spam, anti-malware, and DLP (Data Loss Prevention) policies, along with implementing Umbrella-based content filtering.
Endpoint Protection and Detection (15%)
Protecting the "Last Mile." Master Cisco Secure Endpoint (formerly AMP for Endpoints). Focus on file trajectory, retrospective analysis, and EDR (Endpoint Detection and Response) workflows. Learn to manage the Cisco Secure Client (formerly AnyConnect) for posture assessment and secure connectivity.
Secure Network Access, Visibility, and Enforcement (10%)
Bringing it all together. Master Cisco ISE (Identity Services Engine) for 802.1X and MAB. Focus on visibility using Cisco Secure Network Analytics (formerly Stealthwatch) and orchestrating policy enforcement across the entire fabric.
Cisco 350-701 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
Which product allows Cisco FMC to push security intelligence observable to its sensors from other products?
Correct Answer & Rationale:
Answer: B
Explanation:
The product that allows Cisco FMC to push security intelligence observable to its sensors from other products is Threat Intelligence Director (TID). TID is a feature of Cisco FMC that enables you to integrate third-party threat intelligence feeds into your security policies. TID collects, aggregates, and correlates observables from multiple sources, such as Cisco Talos Intelligence, Cisco Umbrella, and other external providers. TID then pushes the observables to the sensors that are managed by FMC, such as Firepower Threat Defense (FTD) devices, Firepower appliances, and Cisco Secure Firewall Cloud Native. The sensors can then use the observables to block or monitor traffic based on the reputation and threat level of the IP addresses, URLs, and domains12.
1: Firepower Management Center Configuration Guide, Version 6.6 - Threat Intelligence Director [Cisco Secure Firewall Management Center] - Cisco 2: Cisco Firepower Threat Defense Configuration Guide for Firepower Device Manager, Version 6.6 - Threat Intelligence Director [Cisco Firepower NGFW] - Cisco
QUESTION DESCRIPTION:
Which ID store requires that a shadow user be created on Cisco ISE for the admin login to work?
Correct Answer & Rationale:
Answer: C
Explanation:
Active Directory (AD) is an ID store that requires that a shadow user be created on Cisco ISE for the admin login to work. A shadow user is a user account that is defined in the ISE internal database, but has the password set to external. This means that the user authentication is performed against an external identity source, such as AD, while the user authorization is based on the ISE admin group membership. A shadow user is useful when the admin wants to assign different roles or permissions to specific AD users, rather than using AD groups. To create a shadow user, the admin must check the External checkbox in the ISE admin user configuration, and make sure that the username matches the AD username. The shadow user must also be assigned to an ISE admin group that has the Type set to External123. References := 1: ISE Admin User Shadow AD Account Issue 2: ISE Admin user authentication from AD 3: Which ID store requires that a shadow user be created on Cisco ISE for the admin login to work?
QUESTION DESCRIPTION:
How does Cisco Stealthwatch Cloud provide security for cloud environments?
Correct Answer & Rationale:
Answer: A
Explanation:
Explanation
Cisco Stealthwatch Cloud: Available as an SaaS product offer to provide visibility and threat detection within public cloud infrastructures such as Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP).
QUESTION DESCRIPTION:
Refer to the exhibit.
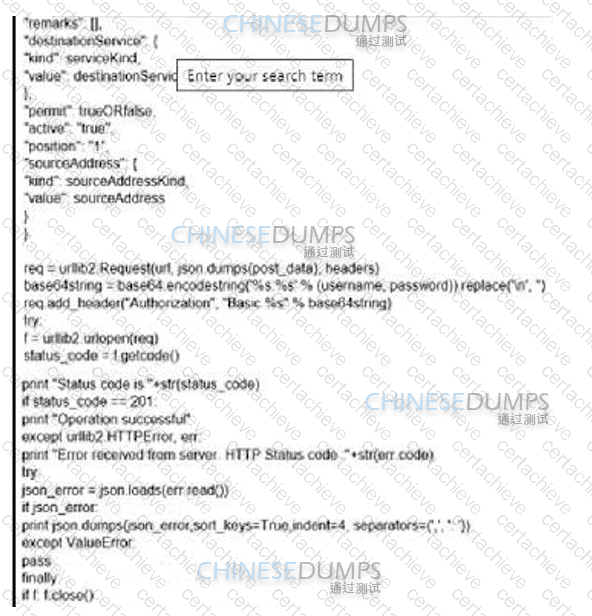
What is the function of the Python script code snippet for the Cisco ASA REST API?
Correct Answer & Rationale:
Answer: A
Explanation:
The Python script code snippet for the Cisco ASA REST API is used to add a global rule into policies. The script uses the urllib2 module to create an HTTP request with the URL, headers, and post_data. The post_data is a JSON object that contains the parameters for the global rule, such as the destination service, the source address, the permit value, and the position. The script also uses the base64 module to encode the username and password for authentication. The script then sends the request to the ASA REST API and prints the status code and the response. If the status code is 201, it means the operation was successful and the global rule was added. If the status code is not 201, it means there was an error and the script prints the JSON error message. The script also handles any HTTP errors and value errors that might occur during the execution. References:
Cisco ASA REST API Quick Start Guide
Configure Secure Access to Use REST API with Python
GitHub - timwukp/Cisco-ASA-REST-API
QUESTION DESCRIPTION:
A network engineer has been tasked with adding a new medical device to the network. Cisco ISE is being used as the NAC server, and the new device does not have a supplicant available. What must be done in order to securely connect this device to the network?
Correct Answer & Rationale:
Answer: A
Explanation:
Explanation
Explanation
As the new device does not have a supplicant, we cannot use 802.1X.
MAC Authentication Bypass (MAB) is a fallback option for devices that don’t support 802.1x. It is virtually
always used in deployments in some way shape or form. MAB works by having the authenticator take the
connecting device’s MAC address and send it to the authentication server as its username and password. The authentication server will check its policies and send back an Access-Accept or Access-Reject just like it would with 802.1x.
Cisco ISE Profiling Services provides dynamic detection and classification of endpoints connected to the
network. Using MAC addresses as the unique identifier, ISE collects various attributes for each network
endpoint to build an internal endpoint database. The classification process matches the collected attributes to prebuilt or user-defined conditions, which are then correlated to an extensive library of profiles. These profiles include a wide range of device types, including mobile clients (iPads, Android tablets, Chromebooks, and so
on), desktop operating systems (for example, Windows, Mac OS X, Linux, and others), and numerous non-user systems such as printers, phones, cameras, and game consoles.
Once classified, endpoints can be authorized to the network and granted access based on their profile. For example, endpoints that match the IP phone profile can be placed into a voice VLAN using MAC Authentication Bypass (MAB) as the authentication method. Another example is to provide differentiated network access to users based on the device used. For example, employees can get full access when accessing the network from their corporate workstation but be granted limited network access when accessing the network from their personal iPhone.
QUESTION DESCRIPTION:
An organization is using DNS services for their network and want to help improve the security of the DNS infrastructure. Which action accomplishes this task?
Correct Answer & Rationale:
Answer: D
Explanation:
DNSSEC (Domain Name System Security Extensions) is a technology that protects DNS from cache poisoning and spoofing attacks by digitally signing DNS data with cryptographic keys. DNSSEC ensures the integrity and authenticity of DNS responses, preventing attackers from redirecting traffic to malicious domains. Cisco Umbrella supports DNSSEC by performing validation on queries sent from Umbrella resolvers to upstream authorities. This means that Umbrella will only accept DNS responses that are signed and verified by the authoritative servers for each domain. To enable DNSSEC validation, the organization needs to configure Cisco Umbrella and use DNSSEC for domain authentication to authoritative servers. This will ensure that Umbrella resolvers will reject any forged or tampered DNS responses and provide secure DNS resolution for the organization’s network. References :=
Some possible references are:
Implementing and Operating Cisco Security Core Technologies (SCOR) v1.0, Module 2: Network Security, Lesson 2.5: Implement DNS Security
What is DNSSEC and Why Is It Important? - Cisco Umbrella
DNSSEC General Availability – Cisco Umbrella
QUESTION DESCRIPTION:
A company is experiencing exfiltration of credit card numbers that are not being stored on-premise. The
company needs to be able to protect sensitive data throughout the full environment. Which tool should be used
to accomplish this goal?
Correct Answer & Rationale:
Answer: B
Explanation:
Explanation
Cisco Cloudlock is a cloud-native cloud access security broker (CASB) that helps you move to the cloud safely. It protects your cloud users, data, and apps. Cisco Cloudlock provides visibility and compliance checks, protects data against misuse and exfiltration, and provides threat protections against malware like ransomware.
QUESTION DESCRIPTION:
Which Cisco security solution integrates with cloud applications like Dropbox and Office 365 while protecting data from being exfiltrated?
Correct Answer & Rationale:
Answer: C
Explanation:
Cisco Cloudlock is a cloud-native cloud access security broker (CASB) that helps you move to the cloud safely. It protects your cloud users, data, and apps. Cloudlock’s simple, open, and automated approach uses APIs to manage the risks in your cloud app ecosystem. Cloudlock integrates with cloud applications like Dropbox and Office 365 by providing visibility, compliance, threat protection, and data security. Cloudlock can detect and prevent data exfiltration by applying data loss prevention (DLP) policies, encrypting sensitive data, and alerting or blocking unauthorized activities. Cloudlock also supports cloud app discovery and risk assessment, user and entity behavior analytics (UEBA), and cloud app firewall12. References: 1: Cisco Cloudlock - Cisco 2: Cisco Cloudlock Privacy Data Sheet
QUESTION DESCRIPTION:
Which system facilitates deploying microsegmentation and multi-tenancy services with a policy-based container?
Correct Answer & Rationale:
Answer: D
Explanation:
Contiv is an open source container networking fabric that supports heterogeneous container deployments across virtual machines, bare-metal, and public or private clouds. Contiv facilitates deploying microsegmentation and multi-tenancy services with a policy-based container by allowing cloud architects and IT admins to create, manage, and enforce operational policies such as traffic isolation, bandwidth prioritization, latency requirements, and policies for L4-L7 network services. Contiv also integrates natively with Cisco infrastructure and provides consistent networking across any platform (Docker Swarm, Kubernetes, or OpenShift) and any networking backend (Layer 2, Layer 3, Overlays, or ACI mode)123. References := 1: Introducing Contiv 1.0 - The Most Powerful Container Networking Fabric 2: contivpp 3: Contiv · GitHub
QUESTION DESCRIPTION:
An organization wants to reduce their attach surface for cloud applications. They want to understand application communications, detect abnormal application Behavior, and detect vulnerabilities within the applications. Which action accomplishes this task?
Correct Answer & Rationale:
Answer: A
Explanation:
Cisco Secure Workload (formerly Tetration) is a solution that provides visibility, segmentation, and security for cloud applications. It can monitor application communications, detect abnormal application behavior, and identify vulnerabilities within the applications. Cisco Secure Workload can also enforce granular policies to control the traffic between applications and prevent unauthorized access. References: Implementing and Operating Cisco Security Core Technologies (SCOR) v1.0, Module 6: Cloud and Content Security, Lesson 6.2: Cisco Cloud Security Solutions, Topic 6.2.2: Cisco Secure Workload
A Stepping Stone for Enhanced Career Opportunities
Your profile having CCNP Security certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Cisco 350-701 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Cisco Exam 350-701
Achieving success in the 350-701 Cisco exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in 350-701 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam 350-701!
In the backdrop of the above prep strategy for 350-701 Cisco exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding 350-701 exam prep. Here's an overview of Certachieve's toolkit:
Cisco 350-701 PDF Study Guide
This premium guide contains a number of Cisco 350-701 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Cisco 350-701 study guide pdf free download is also available to examine the contents and quality of the study material.
Cisco 350-701 Practice Exams
Practicing the exam 350-701 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Cisco 350-701 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Cisco 350-701 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning 350-701 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Cisco 350-701 CCNP Security FAQ
There are only a formal set of prerequisites to take the 350-701 Cisco exam. It depends of the Cisco organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Cisco 350-701 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Cisco 350-701 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Cisco 350-701 exam dumps to enhance your readiness for the exam.
Like any other Cisco Certification exam, the CCNP Security is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do 350-701 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The 350-701 Cisco exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Cisco 350-701 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Cisco has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Cisco changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



