The Microsoft Identity and Access Administrator (SC-300)
Passing Microsoft Microsoft Certified: Identity and Access Administrator Associate exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard SC-300 Dumps
In 2026, Microsoft uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Microsoft SC-300 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
You need to allocate licenses to the new users from A. Datum. The solution must meet thetechnical requirements.
Which type of object should you create?
Correct Answer & Rationale:
Answer: B
Explanation:
In Azure AD, license automation is implemented through group-based licensing . The SC-300 materials explain that “you can assign licenses to a group in Azure Active Directory; when you assign a license to a group, all users who are members of the group are assigned that license” . They also clarify that “dynamic group membership uses rules to automatically add or remove users based on user attributes” , which is the recommended way to on-board new populations without manual effort. For licensing, the guide is explicit that “group-based licensing works with security groups and Microsoft 365 Groups” and that “distribution lists are not supported for license assignment” . Administrative Units are described as “a scoping mechanism for delegating administrative permissions to subsets of users and devices” , not a licensing entity. Likewise, Organizational Units (OUs) are on-premises AD containers and “do not control license assignment in Azure AD” .
Given the requirement to allocate licenses automatically to new A. Datum users as they appear, the least-effort, policy-driven approach is to create an Azure AD Dynamic User security group with a membership rule that targets those users (for example, by domain, company attribute, or a synced attribute), then assign the required Microsoft 365/Azure AD licenses to that group. As the documentation notes, “when users join or leave the group based on the rule, licenses are added or removed automatically.”
QUESTION DESCRIPTION:
You need to sync the ADatum users. The solution must meet the technical requirements.
What should you do?
Correct Answer & Rationale:
Answer: A
Explanation:
The SC-300 coverage of Azure AD Connect explains that when you need to bring in a new set of on-premises users or change what is synchronized (for example, adding an additional domain/OU such as ADatum or adjusting filtering), you reopen the Azure AD Connect wizard and choose “Customize synchronization options.” The guide notes that this path lets you “modify directory/OU filtering, add or remove forests, and enable optional sync features” so that only the intended users are synchronized. It contrasts with operational commands: Start-ADSyncSyncCycle merely triggers an immediate delta/full sync of the current configuration; Set-ADSyncScheduler changes the sync cadence or pause/resume behavior; and “Change user sign-in” alters the authentication method (e.g., PHS vs. PTA) but does not control scoping of which users are synced. To meet a requirement to sync the ADatum users according to technical constraints (such as OU/domain selection or feature toggles), you must first configure the scope by running the wizard and selecting Customize synchronization options, then perform/allow a sync cycle to bring those users into Azure AD as defined.
QUESTION DESCRIPTION:
You need to implement the planned changes and technical requirements for the marketing department.
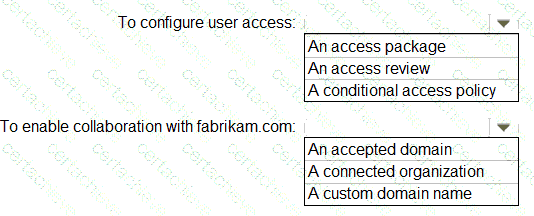
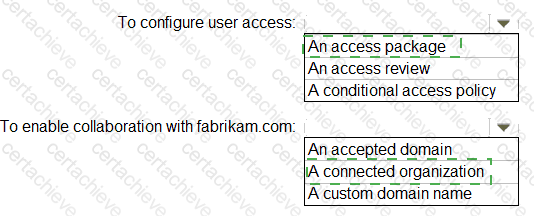
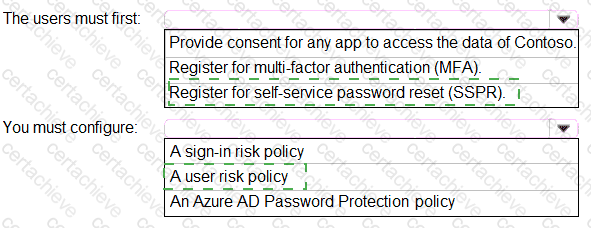
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Correct Answer & Rationale:
Answer:
Explanation:
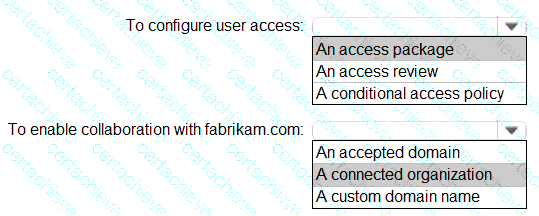
According to the Microsoft SC-300: Identity and Access Administrator official study guide and Microsoft Learn modules on Azure AD Identity Governance , the correct way to manage user access—especially for scenarios involving both internal and external users—is through Entitlement Management in Azure AD Identity Governance .
Entitlement Management uses access packages to define and automate how users obtain access to resources such as groups, SharePoint sites, and applications. Access packages contain policies that specify who can request access (internal users, external users, or both) and how that access is approved and periodically reviewed. The guide clearly states:
“Access packages provide a structured method to configure and automate access for users, ensuring that access assignments follow the organization’s policy and compliance requirements.”
To enable external collaboration with another organization (such as fabrikam.com ), Microsoft documentation emphasizes that you must create a connected organization . A connected organization represents an external directory or domain whose users can be invited to request access packages or participate in identity governance workflows. The connected organization defines trust boundaries for cross-tenant collaboration, without requiring domain federation or acceptance.
In summary:
Access packages configure and automate user access.
QUESTION DESCRIPTION:
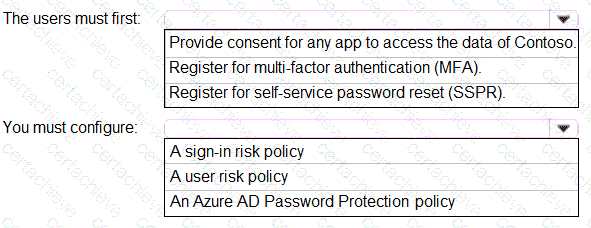
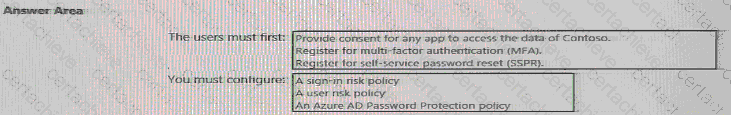
You need to meet the technical requirements for the probability that user identities were compromised.
What should the users do first, and what should you configure? To answer, select the appropriate options in the answer area.
NOTE:Each correct selection is worth one point.
Correct Answer & Rationale:
Answer:
Explanation:
According to the Microsoft Identity and Access Administrator (SC-300) official study guide and Microsoft Learn module “Implement and manage user risk policies”, the scenario where “users must be forced to change their password if there is a probability that their identity was compromised” directly maps to the Azure AD Identity Protection “User risk policy.”
In Azure AD Identity Protection, user risk represents the likelihood that an account’s credentials have been compromised. When Azure AD detects a high user risk (for example, leaked credentials, atypical sign-in behavior, or sign-ins from unfamiliar locations), the User Risk Policy can be configured to automatically block access or require the user to reset their password upon the next sign-in.
Before a user can reset their password or complete remediation, they must have a registered authentication method (for password reset and MFA). Therefore, users must first register for multi-factor authentication (MFA) — this registration enables the authentication methods (like phone number or authenticator app) that are also used during password reset verification.
The SC-300 documentation specifically highlights:
“To enforce a password change when a user’s identity risk is high, the user must be registered for MFA, and a user risk policy must be configured to require password change.”
Thus, the correct configuration is:
Users must first register for MFA — to ensure they have verified methods available.
Configure a user risk policy — to automatically trigger password reset upon detection of compromised credentials.
Correct Answers:
Users must first: Register for multi-factor authentication (MFA).
You must configure: A user risk policy.
QUESTION DESCRIPTION:
You need to locate licenses to the A. Datum users. The solution must need the technical requirements.
Which type of object should you create?
Correct Answer & Rationale:
Answer: A
Explanation:
According to the Microsoft SC-300: Identity and Access Administrator official study guide and the Microsoft Learn module “Manage user and group licenses in Microsoft Entra ID (Azure AD)”, when you need to automatically assign licenses to users based on specific attributes (such as department, location, or a custom attribute like LWLicenses ), you should use a Dynamic User Security Group in Azure Active Directory (Entra ID).
In the scenario, Litware wants to:
“Manage the assignment of Azure AD licenses by modifying the value of the LWLicenses attribute. Users who have the appropriate value for LWLicenses must be added automatically to the Microsoft 365 group that has the appropriate license assigned.”
This requirement directly maps to a Dynamic User security group, which supports dynamic membership rules that automatically include users when their attributes meet defined conditions (for example, user.extensionAttribute15 -eq " E5 " ). When a license is assigned to this dynamic group, Azure AD automatically provisions or removes licenses for members based on their attribute values — eliminating manual license management.
Per Microsoft documentation:
“You can assign licenses to a group that has dynamic membership. When a user’s attributes change, Azure AD automatically adds or removes them from the group, which updates their license assignments accordingly.”
Now, analyzing the other options:
B. An OU (Organizational Unit): Used in on-premises Active Directory, not Azure AD. It cannot manage cloud-based license assignments.
C. A Distribution Group: Used for email distribution in Exchange Online; cannot be used for license assignment.
D. An Administrative Unit: Used for scoping administrative permissions, not for license assignment.
Therefore, the only object type that satisfies both the technical and automation requirements is a Dynamic User Security Group.
✅ Correct Answer: A. A Dynamic User security group
QUESTION DESCRIPTION:
You need to meet the planned changes and technical requirements for App1.
What should you implement?
Correct Answer & Rationale:
Answer: D
Explanation:
According to the Microsoft SC-300: Identity and Access Administrator Study Guide and the Microsoft Learn module “Publish on-premises apps for remote access using Azure AD Application Proxy”, Azure AD Application Proxy enables secure remote access to internal, on-premises web applications without requiring VPN access.
In the scenario, App1 is an on-premises application hosted within the Litware network, and the technical requirements specify that it must be securely accessible to both internal and external users — including Fabrikam guest accounts — through Azure AD authentication.
Microsoft’s official documentation states:
“Azure AD Application Proxy provides secure remote access to on-premises web applications, integrating with Azure AD for single sign-on (SSO) and conditional access policies.”
Given that the environment already includes a server (SERVER1) running the Azure AD Application Proxy connector, and that Litware wants to enforce Azure AD Conditional Access and MFA for App1, Azure AD Application Proxy is the correct implementation.
The other options are not suitable:
A. Policy set in Microsoft Endpoint Manager: Used for device compliance and app management, not for publishing on-premises apps.
B. App configuration policy in Endpoint Manager: Used for mobile app configuration (e.g., MAM policies), not for access publishing.
C. App registration in Azure AD: Used for modern cloud or SaaS apps integration, but App1 is on-premises and needs proxy access.
Correct Answer: D. Azure AD Application Proxy
QUESTION DESCRIPTION:
You need to meet the planned changes for the User administrator role.
What should you do?
Correct Answer & Rationale:
Answer: B
Explanation:
In Azure AD Privileged Identity Management (PIM) for Azure AD roles, the exam materials describe that you tailor how a role (for example, User administrator) is used by editing its Role settings. These settings control activation behavior, including require multi-factor authentication, justification, approval, assignment/activation durations, and notifications . The guide states that administrators can “configure activation requirements and time-bound eligibility on a per-role basis” and “enforce approval workflows and MFA at activation.” Access reviews are used to periodically verify who still needs a role , but they do not implement the operational changes to how the role is activated. Active assignments simply shows and changes who currently holds active/eligible assignments; it does not set policy for the role’s activation behavior. Administrative units scope certain directory tasks, but they are not how you change PIM activation/approval/MFA requirements. Therefore, to meet planned changes for the User administrator role (such as least privilege activation with approval, justification, and MFA), you update PIM → Azure AD roles → User administrator → Role settings. This aligns with the SC-300 objective to “configure PIM settings and policies for Azure AD roles,” ensuring governance by policy rather than ad-hoc assignment.
QUESTION DESCRIPTION:
You need to meet the technical requirements for the probability that user identifies were compromised.
What should the users do first, and what should you configure? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Correct Answer & Rationale:
Answer:
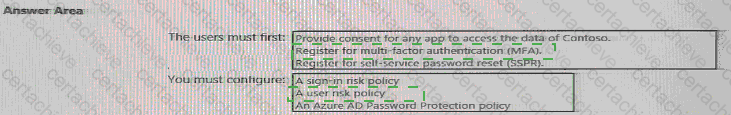
Explanation:
The users must first: Register for multi-factor authentication (MFA)
You must configure: A user risk policy
According to Microsoft SC-300 official learning materials and Exam Ref SC-300: Microsoft Identity and Access Administrator , when the requirement is to address the probability that user identities were compromised, the appropriate feature is Azure AD Identity Protection. Identity Protection detects risky sign-ins and risky users through continuous analysis of login behavior, location, device, and credential exposure signals.
Two types of policies can be created:
Sign-in risk policy – Triggers actions based on suspicious sign-in behavior (for example, unfamiliar location).
User risk policy – Triggers actions when the user’s overall identity is deemed at risk (for example, compromised credentials).
The documentation specifies:
“When user risk is detected, the policy can require the user to change their password to remediate the risk. Users must first be registered for MFA to perform secure password change operations.”
Therefore, before the user risk policy can be enforced, users must be enrolled in multi-factor authentication (MFA). MFA is used during the remediation step (password change) to verify the user’s identity securely.
Thus, to meet the requirement for “the probability that user identities were compromised,” you configure a user risk policy in Azure AD Identity Protection, and ensure that users first register for MFA so that they can complete password change or verification flows when risks are detected.
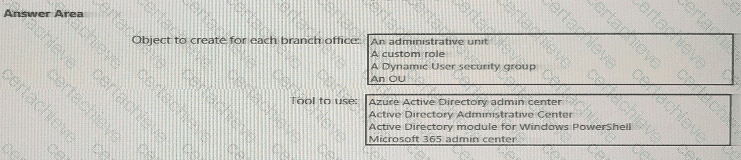
QUESTION DESCRIPTION:
You need to meet the technical requirements for license management by the helpdesk administrators.
What should you create first, and which tool should you use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Correct Answer & Rationale:
Answer:
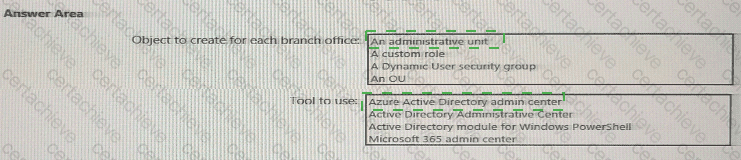
Explanation:
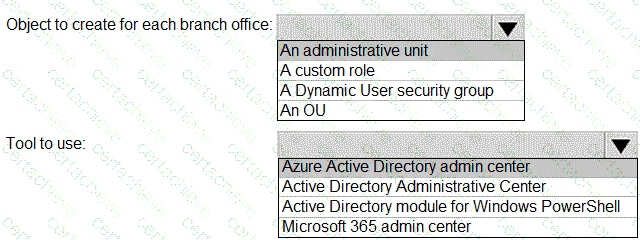
As per the Microsoft SC-300: Identity and Access Administrator official study materials and Microsoft Learn documentation on “Manage administrative units in Azure Active Directory” , Administrative Units (AUs) are designed to delegate administrative permissions within large organizations based on divisions such as geography or department. They provide scoped administrative control —allowing helpdesk or user administrators to manage users only within a specific subset of the directory, such as a branch office or department.
In this scenario, Contoso’s technical requirement states:
“The helpdesk administrators must be able to manage licenses for only the users in their respective office.”
To fulfill this, you must create an administrative unit for each branch office (e.g., Montreal, London, Seattle) and assign helpdesk administrators scoped to those AUs. This ensures that each helpdesk admin can only manage licenses for the users within their respective office, enforcing the principle of least privilege.
The Azure Active Directory admin center is the correct tool for creating and managing administrative units. SC-300 guidance clarifies that administrative units are Azure AD objects , not on-premises Active Directory objects like Organizational Units (OUs). Therefore, they are created and managed exclusively through the Azure portal , Microsoft Graph , or PowerShell for Azure AD , but the most straightforward interface for exam purposes is the Azure AD admin center .
QUESTION DESCRIPTION:
You create a Log Analytics workspace.
You need to implement the technical requirements for auditing.
What should you configure in Azure AD?
Correct Answer & Rationale:
Answer: B
Explanation:
To meet auditing and monitoring requirements, Azure AD must send sign-in logs and audit logs to an external location such as a Log Analytics workspace, Azure Storage account, or Event Hub. This is configured using Diagnostics settings in Azure AD.
According to Microsoft documentation in “Monitor Azure Active Directory activity logs in Azure Monitor” and the SC-300 learning objective “Implement and monitor identity governance” , you must enable diagnostic settings to stream directory logs to a Log Analytics workspace.
The scenario specifies:
“You create a Log Analytics workspace. You need to implement the technical requirements for auditing.”
By configuring Azure AD’s Diagnostics settings, you can:
Send Sign-in logs, Audit logs, and Provisioning logs to Log Analytics.
Correlate identity events with security insights in Azure Sentinel or Microsoft Defender for Cloud Apps.
Microsoft documentation confirms:
“To collect and analyze Azure AD sign-in and audit data, configure diagnostic settings to send logs to Log Analytics.”
Other options do not meet the requirement:
A. Company branding: Only affects login pages, not logging or auditing.
C. External Identities: Controls guest access, not logging.
D. App registrations: Used for app integration, not auditing.
A Stepping Stone for Enhanced Career Opportunities
Your profile having Microsoft Certified: Identity and Access Administrator Associate certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Microsoft SC-300 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Microsoft Exam SC-300
Achieving success in the SC-300 Microsoft exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in SC-300 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam SC-300!
In the backdrop of the above prep strategy for SC-300 Microsoft exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding SC-300 exam prep. Here's an overview of Certachieve's toolkit:
Microsoft SC-300 PDF Study Guide
This premium guide contains a number of Microsoft SC-300 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Microsoft SC-300 study guide pdf free download is also available to examine the contents and quality of the study material.
Microsoft SC-300 Practice Exams
Practicing the exam SC-300 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Microsoft SC-300 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Microsoft SC-300 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning SC-300 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Microsoft SC-300 Microsoft Certified: Identity and Access Administrator Associate FAQ
There are only a formal set of prerequisites to take the SC-300 Microsoft exam. It depends of the Microsoft organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Microsoft SC-300 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Microsoft SC-300 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Microsoft SC-300 exam dumps to enhance your readiness for the exam.
Like any other Microsoft Certification exam, the Microsoft Certified: Identity and Access Administrator Associate is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do SC-300 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The SC-300 Microsoft exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Microsoft SC-300 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Microsoft has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Microsoft changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor




