The Fortinet NSE 4 - FortiOS 7.6 Administrator (NSE4_FGT_AD-7.6)
Passing Fortinet Fortinet Network Security Expert exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard NSE4_FGT_AD-7.6 Dumps
In 2026, Fortinet uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official Fortinet NSE4_FGT_AD-7.6 Exam Domains
Our curriculum is meticulously mapped to the Fortinet official blueprint.
Deployment and System Configuration (22%)
Mastering initial setup, log configuration, and diagnosing resource/connectivity problems. Includes FGCP HA clusters and FortiGate VM deployments in public clouds.
Firewall Policies and Authentication (20%)
Expertise in configuring firewall policies, SNAT/DNAT options, and implementing multiple authentication methods including FSSO.
Content Inspection (26%)
The largest domain - covers encrypted traffic inspection, web filtering modes, application control, antivirus scanning, and IPS threat protection.
Routing (18%)
Configuring static routes and implementing SD-WAN to effectively load balance traffic across multiple WAN links for network resilience.
VPN Implementation (14%)
Mastering the deployment of meshed and partially redundant IPsec VPNs to ensure secure and continuous remote communication.
Fortinet NSE4_FGT_AD-7.6 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
Which two statements about the Security Fabric rating are true? (Choose two answers)
Correct Answer & Rationale:
Answer: B, C
Explanation:
“The Security Rating page is separated into three major scorecards: Security Posture, Fabric Coverage, and Optimization, which provide an executive summary of the three largest areas of security focus in the Security Fabric .” ( Fortinet Document Library )
“On the root FortiGate , go to Security Fabric > Security Rating.” ( Fortinet Document Library )
“The Info and Compliance tab includes the security controls used for the test and links to specific FSBP, PCI, or CIS compliance policies .” ( Fortinet Document Library )
“A new Security Rating Insights feature provides immediate access to crucial security information. Hover over any tested object to reveal a tooltip...” and “Objects, such as firewall policies, with security rating recommendations are highlighted... click Security Rating Insights to display relevant issues.” ( Fortinet Document Library )
Technical Deep Dive:
The correct answers are B and C .
B is correct because Security Rating is viewed from the root FortiGate and its scorecards provide an executive summary for the Security Fabric, not just an isolated downstream unit. The root device is the point from which the Security Fabric summary is presented. ( Fortinet Document Library )
C is correct because the Security Rating results include an Info and Compliance view with references to PCI compliance policies. That means PCI-related compliance results are part of the Security Rating reporting associated with the security categories, including Security Posture. ( Fortinet Document Library )
Why the others are incorrect:
A is incorrect because Fortinet documents state there is a base set of free checks and a separate licensed set of checks. A license is not required just to obtain the executive summary view itself. ( Fortinet Document Library )
D is incorrect because Security Rating Insights are not limited to the Security Rating page. Fortinet documents show they also appear as tooltips and buttons on other GUI objects and pages . ( Fortinet Document Library )
QUESTION DESCRIPTION:
What are three key routing principles in SD-WAN? (Choose three answers)
Correct Answer & Rationale:
Answer: A, C, E
Explanation:
“This slide shows the SD-WAN rule lookup process. SD-WAN rules are essentially policy routes.”
“FortiGate performs a forwarding information base (FIB) lookup for the packet destination IP (dstip). If the resolved interface for the fib-best-match isn’t an SD-WAN member, then FortiGate moves on to the next rule. This behavior follows the key routing principle: SD-WAN rules are skipped if the best route to the destination isn’t an SD-WAN member .”
“If the resolved interface is an SD-WAN member, then FortiGate looks for one or more acceptable members in the oif list... An acceptable member is an alive member that has a route to the destination. This behavior follows the key routing principle: SD-WAN rules are skipped if none of the configured members in the rule have a valid route to the destination .”
“Because regular policy routes have precedence over any other routes...”
“Also note that policy routes have precedence over SD-WAN rules, and over any routes in the FIB.”
Technical Deep Dive:
The correct answers are A, C, and E .
A is correct because an SD-WAN rule is not enough by itself. A selected member must also be alive and have a valid route to the destination. If none of the members referenced by the rule can actually reach the destination, the rule is skipped.
C is correct because a regular policy route is evaluated before SD-WAN rules. This is a classic exam trap. FortiGate treats SD-WAN steering like policy-route logic, but standard policy routes still win if they match and are valid.
E is correct because FortiGate first checks the FIB best match . If that best route resolves to an interface that is not an SD-WAN member, FortiGate skips the SD-WAN rule and continues.
Why the others are wrong:
B is false because SD-WAN rules do not have precedence over everything; regular policy routes do.
D is false because the number of available routes is not the deciding rule. Even with only one route, SD-WAN can still steer traffic if the routing and member conditions are met.
Operationally, think of SD-WAN routing in this order: policy route check → SD-WAN rule lookup → standard FIB fallback . On FortiGate, the practical validation commands are:
get router info routing-table all
diagnose sys sdwan service
diagnose firewall proute list
That combination lets you confirm whether a packet is being captured by a policy route, whether an SD-WAN rule has acceptable members, and what the FIB currently resolves for the destination.
QUESTION DESCRIPTION:
Refer to the exhibits.
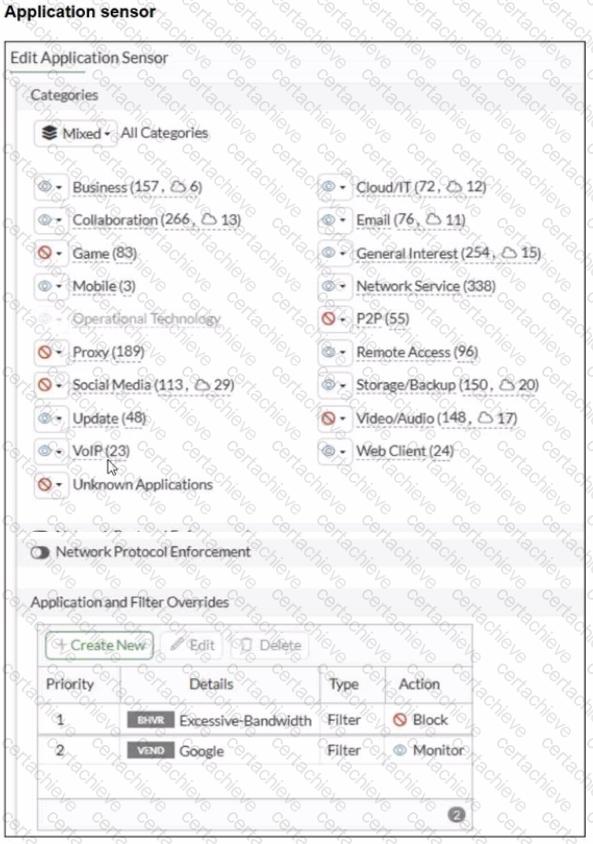
You have implemented the application sensor and the corresponding firewall policy as shown in the exhibits.
Which two factors can you observe from these configurations? (Choose two.)
Correct Answer & Rationale:
Answer: A, B
Explanation:
From the exhibits:
The Application Control sensor has these key settings:
Application and Filter Overrides
Priority 1: Excessive-Bandwidth (Type: Filter) with Action Block
Priority 2: Google (Type: Filter) with Action Monitor
Category actions shown include Social Media set to Block (this category includes Facebook).
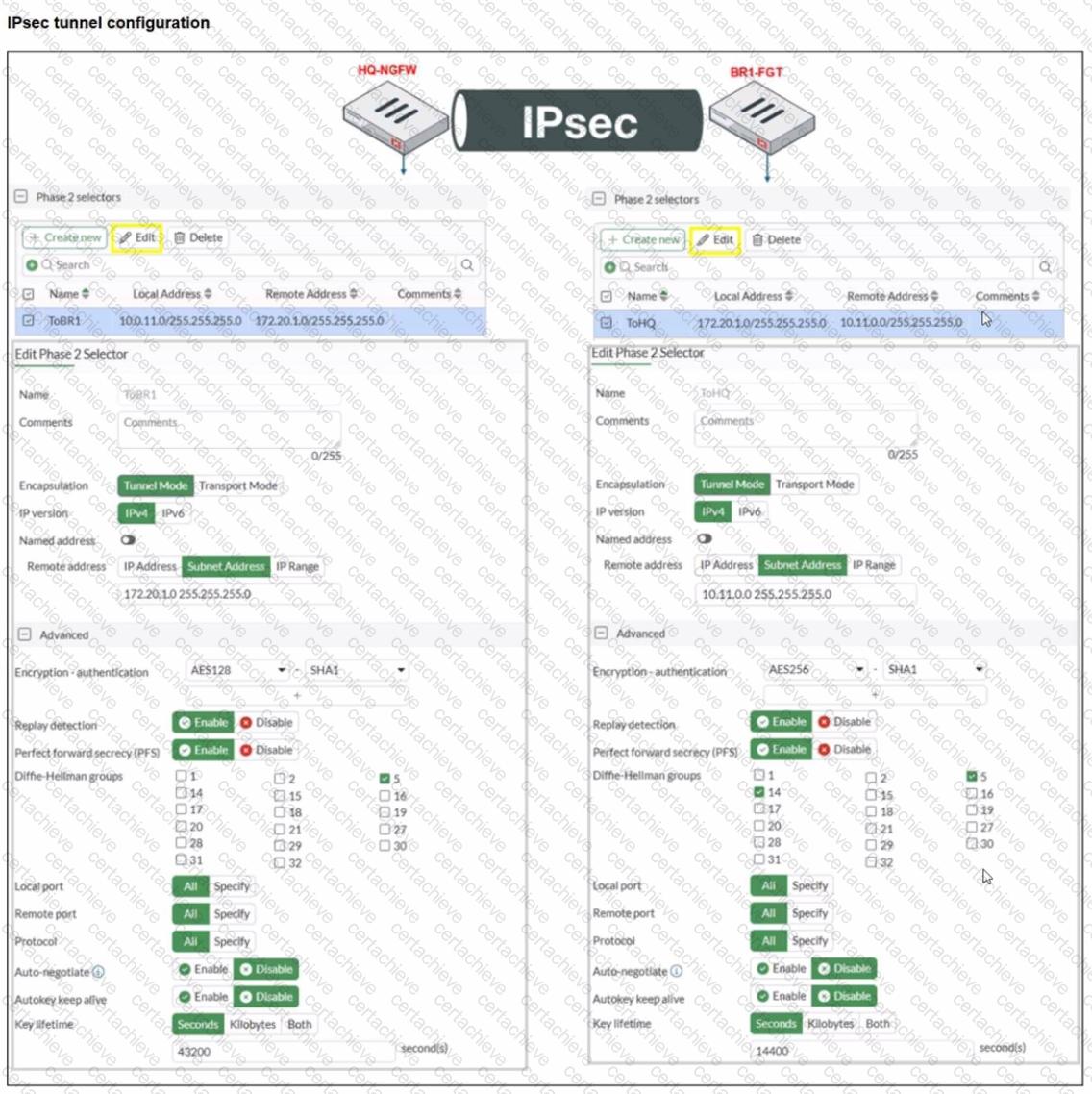
The firewall policy is using:
Flow-based inspection
Application control enabled (profile: default)
Deep inspection enabled (helps identify applications inside HTTPS)
Logging enabled
FortiOS applies Application Control as follows (top-down within the Application Control profile):
Overrides are evaluated by priority (highest priority first).
The first matching override determines the action (block/monitor/allow) for that traffic.
Category-based actions apply to applications that fall into those categories unless an override matches first.
Why A is correct
A. YouTube access is blocked based on Excessive-Bandwidth Application and Filter override settings.
The profile explicitly blocks the Excessive-Bandwidth behavior filter at the highest override priority.
When YouTube traffic is detected as matching the Excessive-Bandwidth behavior, FortiGate will apply the Block action due to the override.
Because this is a priority override, it is enforced before lower-priority entries.
Why B is correct
B. Facebook access is blocked based on the category filter settings.
The Application Sensor shows Social Media configured with a Block action.
Facebook is categorized under Social Media, so it will be blocked when matched by Application Control.
Why C is not correct
C. Facebook access is allowed but you cannot play Facebook videos...
Since the Social Media category is set to Block, Facebook would be blocked at the category level (not merely video playback).
Why D is not correct
D. YouTube search is allowed based on the Google override...
The Google override action is Monitor, not Allow.
“Monitor” logs/detects but does not override a block condition to “allow” traffic.
Also, YouTube traffic is not guaranteed to be treated as “Google” in a way that would permit it, and any matching block condition (such as Excessive-Bandwidth) would still take precedence.
QUESTION DESCRIPTION:
An administrator wanted to configure an IPS sensor to block traffic that triggers the signature set number of times during a specific time period. How can the administrator achieve the objective?
Correct Answer & Rationale:
Answer: C
Explanation:
“ Rate-based IPS signatures also allows you to detect anomalies, which are unusual behaviors in the network...”
“There are two ways to add predefined signatures to an IPS sensor. One way is to select the signatures individually... The second way to add a signature to a sensor is using filters.”
“ You can also add rate-based signatures to block specific traffic when the threshold is exceeded. On the CLI, If you set the command rate-mode to periodical, FortiGate triggers the action when the threshold is reached during the configured Duration time period. ”
Technical Deep Dive:
The correct answer is C. Use IPS signatures, rate-mode periodical option.
The guide is explicit that this behavior belongs to rate-based IPS signatures . The question asks for blocking traffic when a signature is triggered a certain number of times within a defined interval. That is exactly what rate-mode periodical does: it evaluates the trigger count over the configured duration window and then applies the configured IPS action when the threshold is met.
Why the other options are wrong:
A is wrong because rate-mode 60 is not the documented syntax or method.
B is wrong because packet logging records packets; it does not implement threshold-based blocking logic.
D is wrong because the guide ties rate-mode periodical to rate-based signatures , not to IPS filters as the mechanism for this threshold behavior.
Operationally, this is used for anomaly-style detection, similar in concept to lightweight rate-based protection. A typical CLI pattern is along these lines:
config ips sensor
edit " custom-ips "
config entries
edit 1
set rule < signature_id >
set rate-mode periodical
set rate-count < threshold >
set rate-duration < seconds >
set action block
next
end
next
end
This works best when applied only to relevant protocols and signatures, because broad use of rate-based signatures can consume more resources and increase false-positive risk.
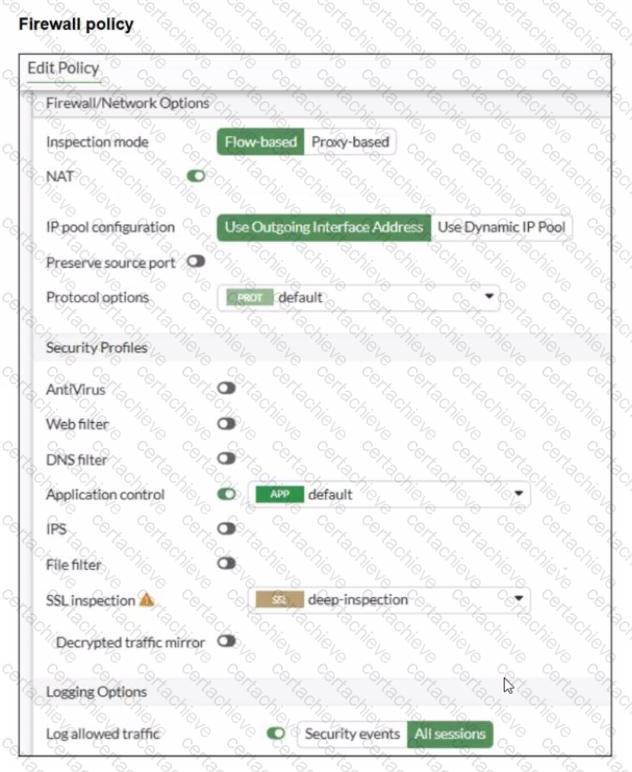
QUESTION DESCRIPTION:
Refer to the exhibit.
A RADIUS server configuration is shown.
An administrator added a configuration for a new RADIUS server While configuring, the administrator enabled Include in every user group What is the impact of enabling Include in every user group in a RADIUS configuration?
Correct Answer & Rationale:
Answer: A
Explanation:
Based on the FortiOS 7.6 Authentication and User Group documentation, the correct answer is A.
Meaning of “Include in every user group” (FortiOS 7.6)
When configuring a RADIUS server on FortiGate, enabling Include in every user group has a very specific and documented effect:
The configured RADIUS server object is automatically added to all FortiGate user groups.
As a result, any user who successfully authenticates against that RADIUS server becomes a valid member of every FortiGate user group, unless additional group filtering (such as RADIUS attributes) is applied.
This simplifies configuration when the same external authentication source must be accepted across multiple firewall policies that reference different user groups.
This behavior is explicitly described in the FortiOS 7.6 Administrator Guide under RADIUS authentication servers and user groups.
Why Option A is Correct
FortiGate user groups can include:
Local users
LDAP servers
RADIUS servers
Enabling Include in every user group causes FortiGate to:
Insert the RADIUS server into all existing and future FortiGate user groups
Therefore, all users authenticating via this RADIUS server are implicitly allowed in every FortiGate user group.
This is exactly what option A describes.
Why the Other Options Are Incorrect
B: FortiGate does not push users or groups into the RADIUS server. Authentication is always initiated by FortiGate toward RADIUS.
C: FortiGate does not manage or modify RADIUS-side group definitions.
D: LDAP and RADIUS user groups are separate authentication mechanisms; this setting does not merge or affect LDAP groups.
QUESTION DESCRIPTION:
Which two statements are correct when FortiGate enters conserve mode? (Choose two answers)
Correct Answer & Rationale:
Answer: B, D
Explanation:
According to the FortiOS 7.6 Study Guide and technical documentation, conserve mode is a protective state triggered when memory utilization reaches the Extreme Threshold (typically 95% by default). When this occurs, the FortiGate implements several measures to prioritize system stability over new functionality. One of the primary restrictions is that the FortiGate refuses to accept configuration changes (Statement B). This prevents the system from initiating new processes or allocating additional memory that could lead to a total system crash.
Regarding traffic handling, the behavior is determined by specific " fail-open " settings. For the IPS engine, if the fail-open global setting is enabled, the FortiGate continues to transmit packets without IPS inspection (Statement D). This ensures that network connectivity is maintained even when the system lacks the memory resources to perform deep packet inspection. In contrast, Statement A is incorrect because the system may skip non-essential actions to save memory. Statement C is incorrect because conserve mode is designed to avoid a system halt; the device remains operational and will automatically exit conserve mode once memory usage drops below the Release Threshold (typically 82%).
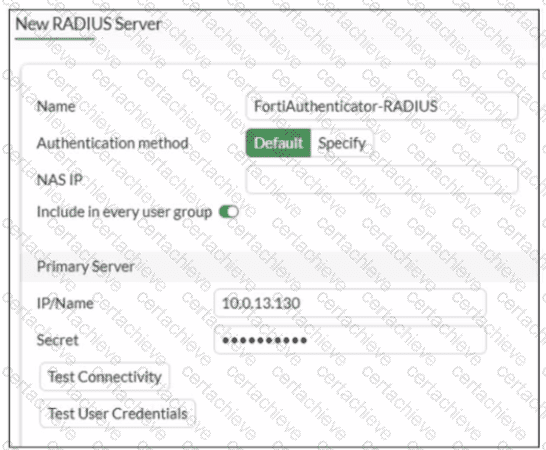
QUESTION DESCRIPTION:
Refer to the exhibit.
A network administrator is troubleshooting an IPsec tunnel between two FortiGate devices. The administrator has determined that phase 1 status is up, but phase 2 fails to come up.
Based on the phase 2 configuration shown in the exhibit, which two configuration changes will bring phase 2 up? (Choose two.)
Correct Answer & Rationale:
Answer: A, D
Explanation:
Phase 1 being up confirms the two FortiGate devices can authenticate and build the IKE SA. Phase 2 failing indicates the IPsec (Quick Mode) SA negotiation is failing due to mismatched Phase 2 parameters.
From the exhibit, the Phase 2 mismatches that would prevent SA establishment are:
1) Phase 2 selectors must mirror each other (Proxy IDs)
HQ-NGFW Phase 2 selector shows:
Local: 10.0.11.0/24
Remote: 172.20.1.0/24
BR1-FGT Phase 2 selector shows:
Local: 172.20.1.0/24
Remote: 10.11.0.0/24 ⟵ does not match HQ’s local subnet (10.0.11.0/24)
In FortiOS, Phase 2 comes up only when the peers’ selectors (proxy IDs) match as opposite pairs (local on one side = remote on the other).
✅ Fix: A. On BR1-FGT, set Remote Address to 10.0.11.0/255.255.255.0.
2) Phase 2 proposal must match (encryption/authentication)
HQ-NGFW shows encryption AES128 (with SHA1)
BR1-FGT shows encryption AES256 (with SHA1)
For Phase 2 to establish, both peers must have at least one common proposal (same encryption and authentication settings). With one side set to AES128 and the other to AES256, there is no match.
✅ Fix: D. On HQ-NGFW, set Encryption to AES256.
Why the other options are not correct
B. Enable Diffie-Hellman Group 2: The exhibit’s mismatch is not resolved by adding DH group 2, and DH group must match when PFS is enabled. This option does not align the peers based on what’s shown.
C. Set Seconds to 43200: Phase 2 lifetime mismatches typically do not prevent Phase 2 from coming up (the negotiated lifetime can be adjusted by the peers). The hard blockers here are the selectors and proposal mismatch.
QUESTION DESCRIPTION:
Which two features of IPsec IKEv1 authentication are supported by FortiGate? (Choose two.)
Correct Answer & Rationale:
Answer: C, D
Explanation:
“Authentication-wise, both versions support PSK and certificate signature . Although only IKEv1 supports XAuth ...”
“Now, you will learn about the Authentication section in phase 1 configuration:
• Method: FortiGate supports two authentication methods: Pre-shared Key and Signature. When you select Pre-shared Key, you must configure both peers with the same pre-shared key. When you select Signature, phase 1 authentication is based on digital certificate signatures.”
“The purpose of phase 1 is to authenticate peers and set up a secure channel... To authenticate each other, the peers use two methods: pre-shared key or digital signature . You can also enable an additional authentication method, XAuth, to enhance authentication. ”
“A common use of the IPsec wizard is for configuring a remote access VPN for FortiClient users. The wizard enables IKE mode config, XAuth , and other appropriate settings for FortiClient users.”
Technical Deep Dive:
The correct answers are C and D .
D is correct because FortiGate supports the two primary IKEv1 authentication methods: pre-shared key and certificate signature . That is explicitly stated in the study guide.
C is also correct because FortiGate supports XAuth with IKEv1 as an additional authentication mechanism. In practice, XAuth is used to request extra user credentials such as a username and password , especially in remote-access VPN deployments such as FortiClient.
Why the other options are incorrect:
A is incorrect because when using Signature , certificate-based authentication is in use. The study guide states that digital signature validation depends on the relevant certificates and CA trust chain being present. It is not a certificate-free method.
B is incorrect because “fewer packets are exchanged” is a characteristic of aggressive mode , not XAuth. XAuth enhances authentication; it is not the feature that makes IKE negotiation faster.
So the two supported IKEv1 authentication features are:
Extended authentication (XAuth) to request the remote peer to provide a username and password
Pre-shared key and certificate signature as authentication methods
QUESTION DESCRIPTION:
What are two characteristics of HA cluster heartbeat IP addresses in a FortiGate device? (Choose two.)
Correct Answer & Rationale:
Answer: A, C
Explanation:
In FortiOS 7.6, HA cluster heartbeat IP addresses are automatically managed by FortiGate and play a critical role in cluster communication and synchronization.
Correct statements
A. Heartbeat IP addresses are used to distinguish between cluster members.
Correct
FortiGate assigns unique heartbeat IP addresses (link-local addresses in the 169.254.0.0/16 range) to each HA member.
These addresses are used for:
Cluster member identification
Health checks
Synchronization traffic
This allows FortiGate units to uniquely identify and communicate with each other inside the HA cluster.
C. A change in the heartbeat IP address happens when a FortiGate device joins or leaves the cluster.
Correct
Heartbeat IPs are dynamically assigned.
When:
A new FortiGate joins the cluster, or
A member leaves or fails,
FortiGate may reassign heartbeat IP addresses to maintain unique identification among members.
This behavior is documented in the FortiOS HA operation and troubleshooting guides.
Why the other options are incorrect
B. The heartbeat interface of the primary device is always assigned IP address 169.254.0.1.
Incorrect
There is no fixed or guaranteed heartbeat IP (such as 169.254.0.1) for the primary unit.
Heartbeat IP assignment is dynamic, not role-based.
D. Heartbeat interfaces have virtual IP addresses that are manually assigned.
Incorrect
Heartbeat IP addresses are:
Automatically assigned
Link-local
Administrators do not manually configure heartbeat IP addresses.
QUESTION DESCRIPTION:
Which two components are part of the secure internet access (SIA) agent-based mode on FortiSASE? (Choose two.)
Correct Answer & Rationale:
Answer: A, C
Explanation:
In FortiSASE Secure Internet Access (SIA) agent-based mode, traffic steering and security enforcement rely on components integrated with the FortiClient agent.
Components used in SIA agent-based mode
A. FortiSASE Firewall-as-a-Service (FWaaS)
Correct.
FWaaS is a core security component of FortiSASE.
It enforces firewall policies, security inspection, and access control for agent-based users.
All user traffic tunneled by the agent is inspected by FWaaS.
C. VPN policies
Correct.
In agent-based mode, the FortiClient establishes a secure tunnel to FortiSASE.
VPN policies define:
Authentication
Access control
Traffic steering
These policies are fundamental to agent-based connectivity.
Why the other options are incorrect
B. Proxy auto-configuration (PAC) filePAC files are used in agentless or proxy-based modes, not agent-based SIA.
D. FortiExtenderFortiExtender is a WAN extension device and is unrelated to FortiSASE SIA agent-based architecture.
A Stepping Stone for Enhanced Career Opportunities
Your profile having Fortinet Network Security Expert certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Fortinet NSE4_FGT_AD-7.6 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Fortinet Exam NSE4_FGT_AD-7.6
Achieving success in the NSE4_FGT_AD-7.6 Fortinet exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in NSE4_FGT_AD-7.6 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam NSE4_FGT_AD-7.6!
In the backdrop of the above prep strategy for NSE4_FGT_AD-7.6 Fortinet exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding NSE4_FGT_AD-7.6 exam prep. Here's an overview of Certachieve's toolkit:
Fortinet NSE4_FGT_AD-7.6 PDF Study Guide
This premium guide contains a number of Fortinet NSE4_FGT_AD-7.6 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Fortinet NSE4_FGT_AD-7.6 study guide pdf free download is also available to examine the contents and quality of the study material.
Fortinet NSE4_FGT_AD-7.6 Practice Exams
Practicing the exam NSE4_FGT_AD-7.6 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Fortinet NSE4_FGT_AD-7.6 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Fortinet NSE4_FGT_AD-7.6 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning NSE4_FGT_AD-7.6 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Fortinet NSE4_FGT_AD-7.6 Fortinet Network Security Expert FAQ
There are only a formal set of prerequisites to take the NSE4_FGT_AD-7.6 Fortinet exam. It depends of the Fortinet organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Fortinet NSE4_FGT_AD-7.6 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Fortinet NSE4_FGT_AD-7.6 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Fortinet NSE4_FGT_AD-7.6 exam dumps to enhance your readiness for the exam.
Like any other Fortinet Certification exam, the Fortinet Network Security Expert is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do NSE4_FGT_AD-7.6 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The NSE4_FGT_AD-7.6 Fortinet exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Fortinet NSE4_FGT_AD-7.6 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Fortinet has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Fortinet changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



