The Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator (NSE7_SSE_AD-25)
Passing Fortinet Fortinet Network Security Expert exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard NSE7_SSE_AD-25 Dumps
In 2026, Fortinet uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official Fortinet NSE7_SSE_AD-25 Exam Domains
Our curriculum is meticulously mapped to the Fortinet official blueprint.
SASE Architecture and Integration (0%)
The "Cloud" foundation. Master the core components of the FortiSASE platform and its role in the Security Service Edge (SSE) market. Focus on the integration of FortiSASE into existing on-premises and hybrid networks. In 2026, this includes evaluating multisite deployment scenarios and understanding how the cloud-delivered security layer interacts with the Fortinet Security Fabric.
SASE Deployment and Management (0%)
The "Orchestration" core. Master the rollout of SASE for both branch offices and remote users. Focus on advanced inspection features (SSL/TLS deep inspection), endpoint profile management, and compliance rules. Learn to optimize security policies for diverse user groups and manage the FortiClient EMS integration to ensure consistent security postures across managed and unmanaged devices.
Secure Private Access & ZTNA (0%)
The "Zero Trust" layer. This is the technical heart of the 2026 blueprint. Master the design and implementation of Secure Private Access (SPA) use cases. Focus on deploying SPA with SD-WAN and configuring ZTNA tagging rules. Learn to architect access proxy configurations that verify device health and user identity before granting access to specific applications, eliminating the need for traditional VPNs.
Analytics and Troubleshooting (0%)
The "Resilience" domain. Master the diagnostic tools required to maintain global connectivity. Focus on troubleshooting SIA (Secure Internet Access) tunnels, SPA performance bottlenecks, and endpoint connectivity issues. Learn to analyze FortiView dashboards, security logs, and user traffic reports to identify and remediate security gaps or performance degradation in real-time.
Fortinet NSE7_SSE_AD-25 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
What are two advantages of using zero-trust tags? (Choose two.)
Correct Answer & Rationale:
Answer: A, B
Explanation:
Zero-trust tags are critical in implementing zero-trust network access (ZTNA) policies. Here are the two key advantages of using zero-trust tags:
Access Control (Allow or Deny):
Zero-trust tags can be used to define policies that either allow or deny access to specific network resources based on the tag associated with the user or device.
This granular control ensures that only authorized users or devices with the appropriate tags can access sensitive resources, thereby enhancing security.
Determining Security Posture:
Zero-trust tags can be utilized to assess and determine the security posture of an endpoint.
Based on the assigned tags, FortiSASE can evaluate the device ' s compliance with security policies, such as antivirus status, patch levels, and configuration settings.
Devices that do not meet the required security posture can be restricted from accessing the network or given limited access.
QUESTION DESCRIPTION:
An existing Fortinet SD-WAN customer is reviewing the FortiSASE ordering guide to identify which add-on is needed to allow future FortiSASE remote users to reach private resources. Which add-on should the customer consider to allow private access? (Choose one answer)
Correct Answer & Rationale:
Answer: C
Explanation:
To enable remote users to access internal applications located behind an existing FortiGate SD-WAN hub, the customer must license the FortiSASE Secure Private Access (SPA) add-on .
Secure Private Access (SPA) Use Case: This specific add-on is designed to extend the Fortinet Security Fabric into the SASE cloud, allowing for a hub-and-spoke architecture where the FortiSASE PoPs act as spokes and the customer ' s on-premises FortiGate acts as the hub.
Licensing Requirements: The SPA add-on is a per-hub (per service connection) license. It provides the necessary entitlements to establish IPsec tunnels and BGP peering between the SASE infrastructure and the corporate FortiGate.
Feature Enablement: Once the SPA license is applied, the Configuration > Private Access menu becomes available in the FortiSASE portal. This allows administrators to define " Service Connections " to their private data centers or cloud VPCs.
Analysis of Other Options:
Option A: The Global add-on is typically related to expanding the geographic reach or performance of the SASE PoPs, not specifically for private resource routing.
Option B: The Branch On-Ramp refers to connecting physical office locations (Thin Edge) to SASE, rather than the specific licensing for private application access for remote users.
Option D: Dedicated Public IP Address is used for source IP anchoring (SIA) to ensure remote users egress with a consistent IP for third-party SaaS IP-whitelisting.
QUESTION DESCRIPTION:
Which two statements about the Hub Selection Method in FortiSASE Secure Private Access (SPA) are correct? (Choose two answers)
Correct Answer & Rationale:
Answer: A, B
Explanation:
According to the NSE7 SASE Enterprise Guide (Pages 64 & 153) , FortiSASE utilizes an intelligent engine to manage connectivity to private resources through various selection methods:
Hub Health and Priority: FortiSASE incorporates a built-in SD-WAN engine for intelligent routing selection among established IPsec links. The health check IP address periodically receives performance metrics, including jitter, latency, and packet loss, for each service connection. In this mode, FortiSASE evaluates the available hubs and selects the one with the highest priority (the most preferred value) within each POP, provided that the hub meets the defined service-level agreement (SLA) requirements . For this configuration to function correctly, both FortiSASE and the SPA hub must use the same Autonomous System Number (ASN).
BGP Multiple Exit Discriminator (MED): This method leverages the standard BGP MED attribute, which allows an autonomous system to signal its preferred entry point to a peer. FortiSASE learns the MED values advertised by the configured hubs. The architecture is designed so that the lower the MED value , the more preferred the path is to the receiving router. Consistent with the " Zero Trust " and " Secure Access " principles, even when using BGP MED, the selection is gated by the health engine; therefore, the hub is only selected if it also satisfies the configured SLA thresholds .
While SLA thresholds can be configured, the primary logic for hub selection focuses on how priority and dynamic routing attributes (like MED) interact with the real-time health of the tunnel.
QUESTION DESCRIPTION:
A FortiSASE customer has been enforcing always-on VPN for their remote users running FortiClient. What option can be enabled under the customer’s Endpoint Profile to allow them access different resources located in the same L2 network? (Choose one answer)
Correct Answer & Rationale:
Answer: A
Explanation:
In a FortiSASE environment where always-on VPN is enforced, FortiClient typically establishes a full tunnel to a Security Point of Presence (PoP). By default, a full-tunnel configuration instructs the endpoint to send all traffic—including traffic destined for the local network—through the secure tunnel to FortiSASE for inspection.
The Local Access Challenge: When a remote user is at home or in a satellite office, they often need to access local resources such as printers, NAS devices, or other computers on the same Layer 2 (L2) broadcast domain. In a standard full-tunnel setup, these local resources become unreachable because the routing table on the endpoint prioritizes the VPN interface for all non-local-gateway traffic.
Allow Local LAN Access: To resolve this while maintaining the security of the " Always-On " requirement, FortiSASE administrators can enable the Allow Local LAN Access feature within the Endpoint Profile .
Configuration Logic: This setting modifies the FortiClient configuration (often via an XML update pushed from the FortiSASE EMS) to include an exemption for the endpoint ' s locally connected subnet. Specifically, it ensures that traffic destined for the local L2 network does not enter the IPsec or SSL-VPN tunnel, allowing the user to interact with local peripherals while all other internet and corporate-bound traffic remains secured by FortiSASE.
Incorrect Options: * Option B and C: Sandbox and Anti-Virus protections are security features for threat detection and do not influence the routing of local network traffic.
Option D: Network Lockdown actually does the opposite; it restricts network access until a VPN connection is established and typically blocks local LAN access unless specific exemptions are made, making it the incorrect choice for enabling access to local resources.
QUESTION DESCRIPTION:
Refer to the exhibits.
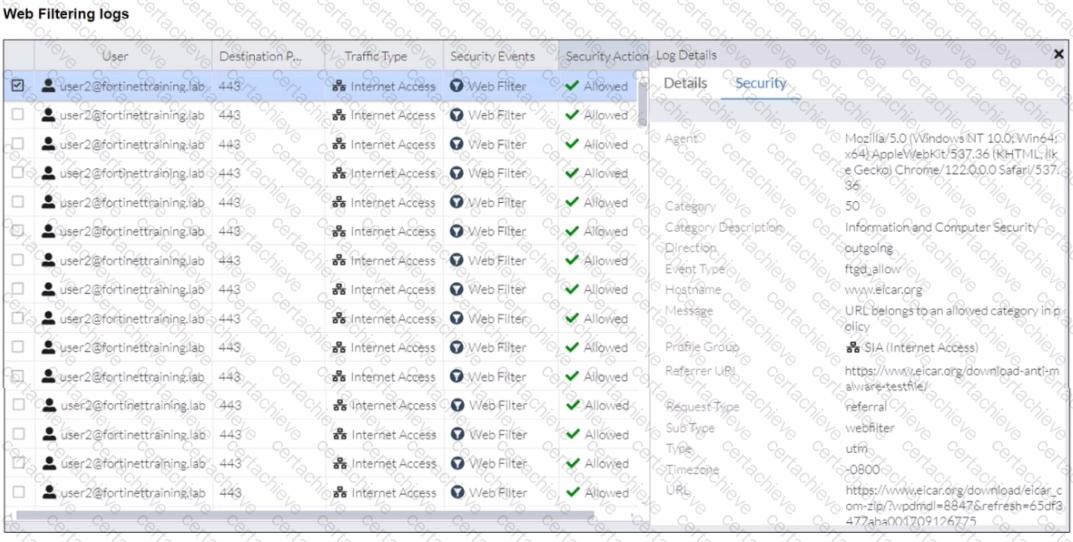
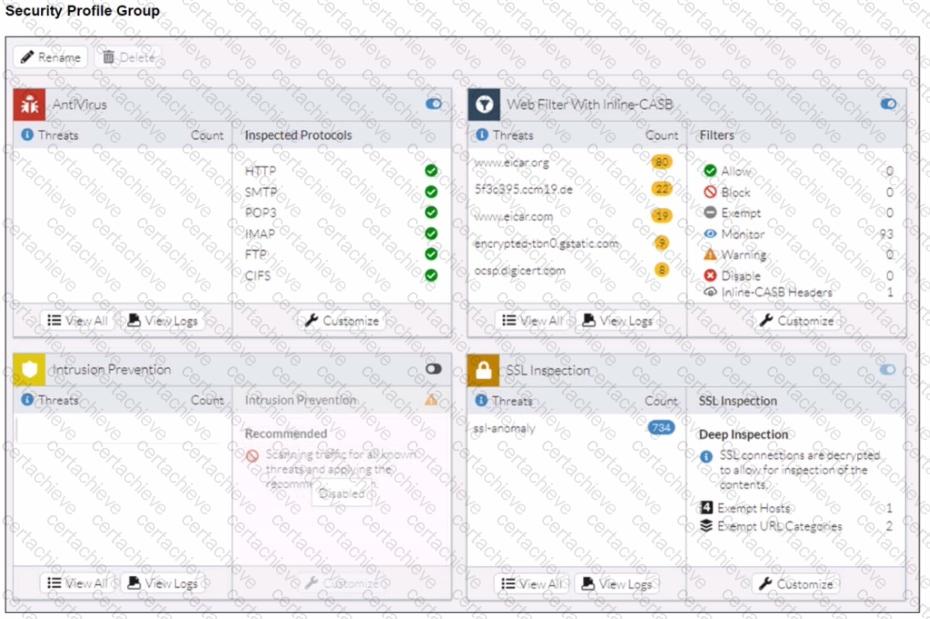
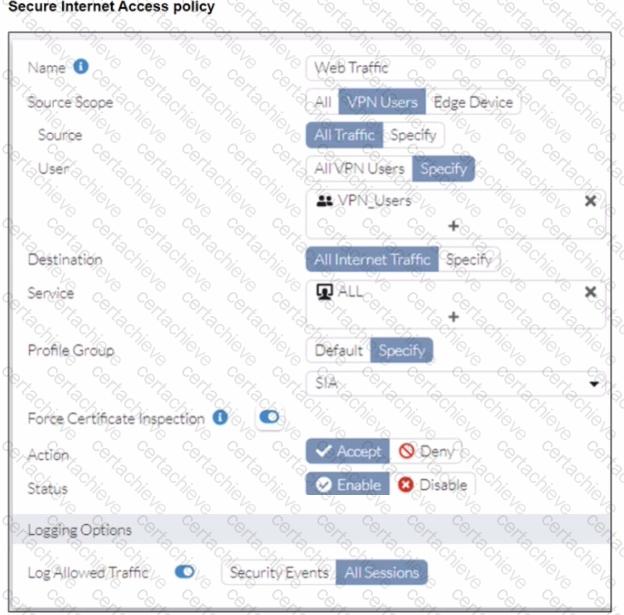
A FortiSASE administrator has configured an antivirus profile in the security profile group and applied it to the internet access policy. Remote users are still able to download the eicar.com-zip file from https://eicar.org. Traffic logs show traffic is allowed by the policy.
Which configuration on FortiSASE is allowing users to perform the download?
Correct Answer & Rationale:
Answer: D
Explanation:
The core of this issue lies in the difference between Certificate Inspection and Deep SSL Inspection within the FortiSASE security framework.
The Limitation of Certificate Inspection: When " Force Certificate Inspection " is enabled in a FortiSASE firewall policy, the system only inspects the SSL handshake—specifically the SNI (Server Name Indication) and certificate headers. It does not decrypt the actual data payload of the HTTPS session.
Antivirus Scanning Requirements: To detect and block malicious files like the EICAR test file when they are downloaded over an encrypted HTTPS connection (such as https://eicar.org), the FortiSASE antivirus engine must be able to " see " inside the encrypted tunnel. This requires Deep Inspection (Full SSL Inspection), where FortiSASE acts as a " man-in-the-middle " to decrypt, scan, and then re-encrypt the traffic.
Exhibit Analysis: The Secure Internet Access policy exhibit clearly shows the toggle for Force Certificate Inspection is enabled (set to " ON " ). As specified in the Fortinet technical documentation, enabling this option forces the policy to use Certificate Inspection only, overriding any Deep Inspection settings that might be defined in the Profile Group.
Conclusion: Because the traffic is only undergoing certificate-level inspection, the antivirus engine cannot analyze the encrypted eicar.com-zip file payload, allowing the download to proceed even though an antivirus profile is active in the group.
QUESTION DESCRIPTION:
An organization wants to block all video and audio application traffic but grant access to videos from CNN Which application override action must you configure in the Application Control with Inline-CASB?
Correct Answer & Rationale:
Answer: D
Explanation:
To block all video and audio application traffic while granting access to videos from CNN, you need to configure an application override action in the Application Control with Inline-CASB. Here is the step-by-step detailed explanation:
Application Control Configuration:
Application Control is used to identify and manage application traffic based on predefined or custom application signatures.
Inline-CASB (Cloud Access Security Broker) extends these capabilities by allowing more granular control over cloud applications.
Blocking Video and Audio Applications:
To block all video and audio application traffic, you can create a policy within Application Control to deny all categories related to video and audio streaming.
Granting Access to Specific Videos (CNN):
To allow access to videos from CNN specifically, you must create an override rule within the same Application Control profile.
The override action " Exempt " ensures that traffic to specified URLs (such as those from CNN) is not subjected to the blocking rules set for other video and audio traffic.
Configuration Steps:
Navigate to the Application Control profile in the FortiSASE interface.
Set the application categories related to video and audio streaming to " Block. "
Add a new override entry for CNN video traffic and set the action to " Exempt. "
QUESTION DESCRIPTION:
Refer to the exhibit.
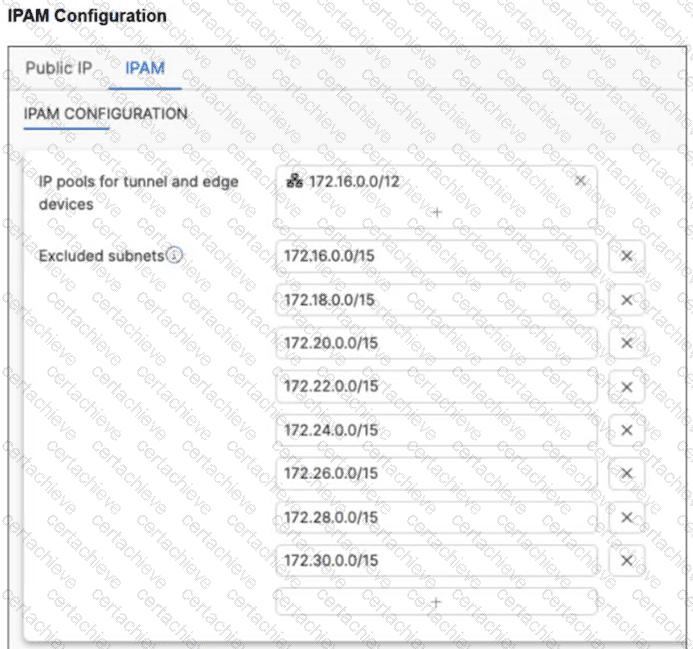
A customer wants to fine-tune network assignments on FortiSASE, so they modified the IPAM configuration as shown in the exhibit. After this configuration, the customer started having connectivity problems and noticed that devices are using excluded ranges. What could be causing the unexpected behavior and connectivity problems? (Choose two answers)
Correct Answer & Rationale:
Answer: A, D
Explanation:
IP Address Management (IPAM) in FortiSASE is responsible for automatically allocating subnets to various services, including VPN tunnels and Edge devices. When an administrator modifies the default IPAM configuration, they must adhere to specific architectural scaling requirements.
Subnet Requirements per PoP: FortiSASE architecture requires a minimum amount of address space to be available for each provisioned Security Point of Presence (PoP) to handle internal routing and endpoint assignments. For the IPAM engine to function correctly and distribute unique subnets across the global infrastructure, the pool must provide at least one /20 subnet per security PoP . If the available space is smaller than this per-PoP requirement, the allocation logic may fail or produce unpredictable routing behavior.
Impact of Excessive Exclusions: In the exhibit (image_578940.png), the customer has defined a large summary pool of 172.16.0.0/12. However, they have configured eight separate /15 excluded subnets: 172.16.0.0/15, 172.18.0.0/15, 172.20.0.0/15, 172.22.0.0/15, 172.24.0.0/15, 172.26.0.0/15, 172.28.0.0/15, and 172.30.0.0/15.
Calculating the Exhaustion: A /12 network contains exactly eight /15 blocks. By excluding all eight /15 ranges listed in the exhibit, the customer has effectively excluded 100% of the available addresses from the primary 172.16.0.0/12 pool.
Connectivity Problems: When the IPAM pool is exhausted or overly restricted, FortiSASE cannot assign valid, non-overlapping subnets to the PoPs. This leads to connectivity problems for remote users and can cause the system to " fall back " to ranges it believes are available, even if they were intended to be excluded, or simply fail to establish tunnels entirely.
To resolve this, the administrator must ensure that the excluded subnets do not consume the entire pool and that the remaining unexcluded space is large enough to provide a /20 block for every active PoP in their subscription.
QUESTION DESCRIPTION:
What are the two key features and benefits of Fortinet SOCaaS when integrated with FortiSASE? (Choose two answers)
Correct Answer & Rationale:
Answer: C, D
Explanation:
Integrating Fortinet SOCaaS (Security Operations Center as a Service) with FortiSASE provides a managed extension of your security team, combining automated AI/ML-driven triage with human expertise to secure remote and on-premises users.
Consistent Security Monitoring and Dashboards (C): Fortinet SOCaaS ensures that your security posture remains robust through seamless integration. This is achieved by configuring FortiSASE to forward pertinent security logs to the SOCaaS cloud, ensuring that analysts have the necessary data to detect anomalies across your network. The service provides verified threat notifications with detailed response guidance and mitigation recommendations. Furthermore, a built-in portal offers intuitive dashboards to track threats and manage escalated alerts.
24x7x365 Expert-Led Monitoring (D): This feature addresses the cybersecurity skills gap by providing around-the-clock vigilance. A global team of Fortinet Security Analysts works 24x7x365 to monitor logs and investigate events. The platform leverages AI and Machine Learning for automated alert triage, while human experts perform in-depth analysis to eliminate false positives and validate threats.
Operational Efficiency: By offloading tedious manual work and triage to Fortinet experts, your internal security team can reduce burnout and focus on higher-value tasks while maintaining a superior security posture for both SASE and on-premises environments.
QUESTION DESCRIPTION:
You have configured FortiSASE Secure Private Access (SPA) deployment. Which statement is true about traffic flows? (Choose two answers)
Correct Answer & Rationale:
Answer: C, D
Explanation:
FortiSASE Secure Private Access (SPA) offers two distinct architectural methods for connecting remote users to private applications: SD-WAN-based SPA and ZTNA-based SPA . Each utilizes a different traffic flow to balance security and performance requirements.
SD-WAN Private Access (Hub-and-Spoke): In this model, the FortiSASE Security Points of Presence (PoPs) act as spokes in a traditional hub-and-spoke VPN topology. When a remote user attempts to access a private network, the traffic is first steered to the closest FortiSASE PoP . The PoP then routes that traffic over a persistent IPsec tunnel to the corporate FortiGate hub (or SPA hub). This ensures that all traffic, regardless of protocol (TCP/UDP), can be inspected by the SASE security stack before entering the private network.
Zero Trust Network Access (ZTNA): Unlike the SD-WAN approach, ZTNA is designed for a " shortest path " connection. While FortiSASE manages the endpoint ' s posture and issues certificates, the actual application traffic (the data plane) bypasses the FortiSASE PoP . Instead, the FortiClient agent on the endpoint establishes a direct HTTPS or TCP-forwarding connection to the ZTNA Access Proxy configured on the corporate FortiGate. This significantly reduces latency and is ideal for high-performance TCP-based applications.
According to the FortiSASE 25 Secure Internet Access Architecture Guide , " In FortiSASE, ZTNA refers to traffic that is destined directly to private resources using the FortiGate ZTNA access proxy traffic flow, " whereas for SD-WAN SPA, the PoPs " rely on IPsec overlays... to secure and route traffic between PoPs and the networks behind an organization’s SD-WAN hubs. "
QUESTION DESCRIPTION:
An organization needs to resolve internal hostnames using its internal rather than public DNS servers for remotely connected endpoints. Which two components must be configured on FortiSASE to achieve this? (Choose two.)
Correct Answer & Rationale:
Answer: B, C
Explanation:
To resolve internal hostnames using internal DNS servers for remotely connected endpoints, the following two components must be configured on FortiSASE:
Split DNS Rules:
Split DNS allows the configuration of specific DNS queries to be directed to internal DNS servers instead of public DNS servers.
This ensures that internal hostnames are resolved using the organization ' s internal DNS infrastructure, maintaining privacy and accuracy for internal network resources.
Split Tunneling Destinations:
Split tunneling allows specific traffic (such as DNS queries for internal domains) to be routed through the VPN tunnel while other traffic is sent directly to the internet.
By configuring split tunneling destinations, you can ensure that DNS queries for internal hostnames are directed through the VPN to the internal DNS servers.
A Stepping Stone for Enhanced Career Opportunities
Your profile having Fortinet Network Security Expert certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Fortinet NSE7_SSE_AD-25 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Fortinet Exam NSE7_SSE_AD-25
Achieving success in the NSE7_SSE_AD-25 Fortinet exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in NSE7_SSE_AD-25 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam NSE7_SSE_AD-25!
In the backdrop of the above prep strategy for NSE7_SSE_AD-25 Fortinet exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding NSE7_SSE_AD-25 exam prep. Here's an overview of Certachieve's toolkit:
Fortinet NSE7_SSE_AD-25 PDF Study Guide
This premium guide contains a number of Fortinet NSE7_SSE_AD-25 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Fortinet NSE7_SSE_AD-25 study guide pdf free download is also available to examine the contents and quality of the study material.
Fortinet NSE7_SSE_AD-25 Practice Exams
Practicing the exam NSE7_SSE_AD-25 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Fortinet NSE7_SSE_AD-25 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Fortinet NSE7_SSE_AD-25 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning NSE7_SSE_AD-25 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Fortinet NSE7_SSE_AD-25 Fortinet Network Security Expert FAQ
There are only a formal set of prerequisites to take the NSE7_SSE_AD-25 Fortinet exam. It depends of the Fortinet organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Fortinet NSE7_SSE_AD-25 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Fortinet NSE7_SSE_AD-25 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Fortinet NSE7_SSE_AD-25 exam dumps to enhance your readiness for the exam.
Like any other Fortinet Certification exam, the Fortinet Network Security Expert is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do NSE7_SSE_AD-25 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The NSE7_SSE_AD-25 Fortinet exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Fortinet NSE7_SSE_AD-25 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Fortinet has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Fortinet changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



