The Fortinet NSE 7 - Public Cloud Security 7.6.4 Architect (NSE7_CDS_AR-7.6)
Passing Fortinet Fortinet Network Security Expert exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard NSE7_CDS_AR-7.6 Dumps
In 2026, Fortinet uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Fortinet NSE7_CDS_AR-7.6 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
Refer to the exhibit.
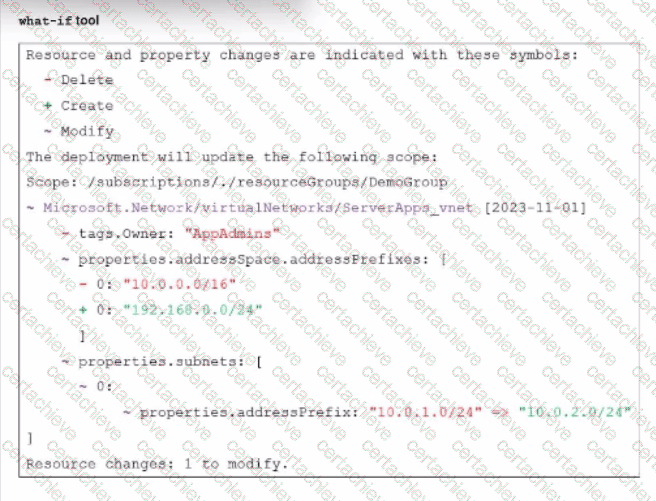
An administrator used the what-if tool to preview changes to an Azure Bicep file.
What will happen if the administrator decides to apply these changes in Azure?
Correct Answer & Rationale:
Answer: B
Explanation:
Based on the Fortinet NSE 7 - Public Cloud Security 7.4/7.6 curriculum and Azure Resource Manager (ARM) deployment logic, the what-if tool provides a predictive analysis of infrastructure changes.
Analyzing the Modification Symbols (Option B): The exhibit shows several critical changes being attempted simultaneously on the ServerApps_vnet.
VNet Address Space Change: The symbol - (Delete) is next to the address space 10.0.0.0/16, and + (Create) is next to 192.168.0.0/24.
Subnet Modification: Further down, the symbol ~ (Modify) indicates an attempt to change the prefix of an existing subnet from 10.0.1.0/24 to 10.0.2.0/24.
Azure Deployment Constraints: According to the FortiOS 7.6 Azure Administration Guide , Azure networking has strict dependencies. You cannot delete or modify an address space that contains active subnets or resources.
Why the deployment fails: The what-if output shows the administrator is trying to remove the 10.0.0.0/16 address range. However, the existing subnet 10.0.1.0/24 is still " resident " within that range during the transaction. Because the subnet is currently attached to the address space being deleted, Azure Resource Manager will reject the deployment as an invalid operation. The attempt to add a new 192.168.0.0/24 range does not resolve the conflict of removing the active range.
Why other options are incorrect:
Option A: The tool shows that 10.0.1.0/24 is being changed to 10.0.2.0/24, not that one is replacing the other as a new entity.
Option C: The symbols show a modification (~) of an existing subnet (index 0:), not the creation (+) of an entirely new subnet.
Option D: The VNet name ServerApps_vnet is not being changed; only its internal properties (tags, address space, and subnets) are being modified.
QUESTION DESCRIPTION:
An AWS administrator must ensure that each member of the cloud deployment team has the correct permissions to deploy and manage resources using CloudFormation. The administrator is researching which tasks must be executed with CloudFormation and therefore require CloudFormation permissions.
Which task is run using CloudFormation?
Correct Answer & Rationale:
Answer: C
Explanation:
Comprehensive and Detailed Explanation From FortiOS 7.6, FortiWeb 7.4 Exact Extract study guide:
Based on the Fortinet NSE 7 - Public Cloud Security 7.4/7.6 study materials and the FortiOS 7.6 AWS Administration Guide , understanding the underlying mechanisms of AWS deployment tools is essential for permission management.
Infrastructure as Code and eksctl (Option C): In the context of Amazon EKS, the eksctl command-line tool is the official CLI for creating and managing clusters on EKS. When an administrator executes the eksctl create cluster command, eksctl does not interact with the EKS API directly to provision infrastructure; instead, it generates and executes AWS CloudFormation stacks to provision the necessary VPC, IAM roles, and the EKS control plane. Therefore, users running this command must have explicit permissions to create and manage CloudFormation stacks.
Resource Provisioning via Stacks: CloudFormation is AWS ' s native service for Infrastructure as Code (IaC), allowing users to define resources in JSON or YAML templates. Commands like eksctl leverage these templates to ensure repeatable and organized deployments of complex architectures, such as those required for a FortiGate or FortiWeb cloud integration.
Why other options are incorrect:
Option A: The kubectl command interacts directly with the Kubernetes API server inside the cluster to manage pods and services; it does not trigger AWS CloudFormation processes.
Option B: Helm is a package manager for Kubernetes. While it manages " releases " within the EKS cluster, the installation of a Helm chart for a FortiWeb ingress controller happens at the Kubernetes software layer and does not utilize AWS CloudFormation stacks.
Option D: Changing the node count via CloudShell using the AWS CLI or kubectl typically modifies an Auto Scaling Group or a Kubernetes Deployment/DaemonSet directly, rather than initiating a new CloudFormation stack execution.
QUESTION DESCRIPTION:
Refer to the exhibit.
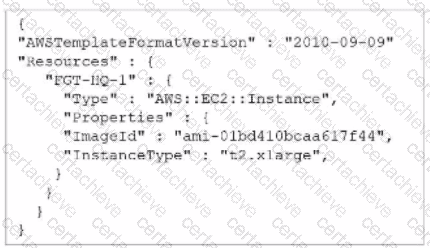
A senior administrator in a multinational organization needs to include a comment in the template shown in the exhibit to ensure that administrators from other regions change the Amazon Machine Image (AMI) ID to one that is valid in their location.
How can the administrator add the required comment in that section of the file?
Correct Answer & Rationale:
Answer: B
Explanation:
According to the FortiOS 7.6 AWS Administration Guide and the Fortinet 7.4 Public Cloud Security study materials regarding infrastructure as code (IaC) for cloud deployments:
JSON Format Limitations (Option B): The exhibit shows an AWS CloudFormation template in JSON (JavaScript Object Notation) format. JSON, by its official specification, does not support comments . There is no native syntax (like // or /* */) to include remarks that are ignored by the CloudFormation parser.
YAML Support: To add descriptive comments—such as instructing other regional administrators to update the AMI ID—the administrator must convert the template into YAML format. YAML is a superset of JSON and specifically supports comments using the # character.
Best Practice for Multinational Deployments: For organizations operating across multiple AWS regions, using YAML is the recommended standard because it allows for inline documentation, making templates more maintainable and easier for different teams to understand regional requirements.
Why other options are incorrect:
Option A: Comments are part of the template file itself, not a parameter or flag within the aws cloudformation update-stack CLI command.
Option C: While # is the correct character for comments in YAML, it is invalid syntax in JSON and would cause the CloudFormation stack creation to fail with a parsing error.
Option D: The AWSTemplateFormatVersion " 2010-09-09 " is currently the only valid version for CloudFormation templates; updating it does not add JSON comment support.
QUESTION DESCRIPTION:
Exhibit.
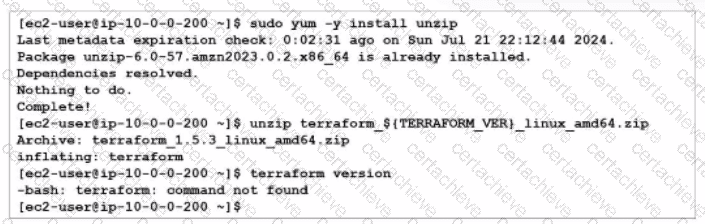
You are tasked with deploying FortiGate using Terraform. When you run the terraform version command during the Terraform installation, you get an error message.
What could you do to resolve the command not found error?
Correct Answer & Rationale:
Answer: A
Explanation:
https://github.com/fortinet/fortigate-terraform-deploy
According to the Terraform documentation for installing Terraform on Linux, you need to download a zip archive that contains a single binary file called terraform. You need to unzip the archive and move the binary file to a directory that is included in your system ' s PATH environment variable, such as /usr/local/bin. This way, you can run the terraform command from any directory without specifying the full path.
If you do not move the binary file to the bin directory, you will get a command not found error when you try to run the terraform version command, as shown in the screenshot. To fix this error, you need to move the binary file to the bin directory or specify the full path of the binary file when running the command.
QUESTION DESCRIPTION:
Refer to the exhibit.
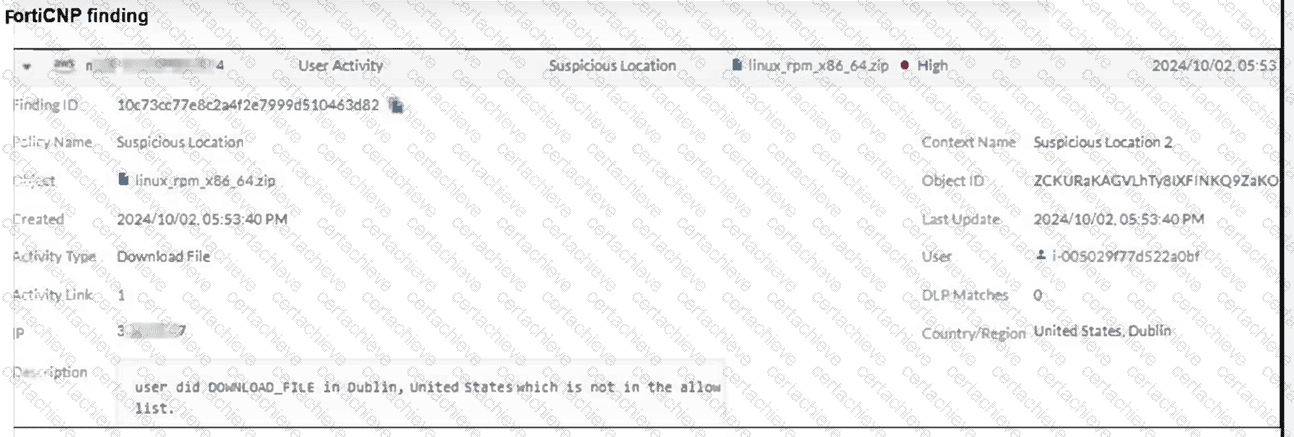
Which FortiCNP policy type generated the finding shown in the exhibit? (Choose one answer)
Correct Answer & Rationale:
Answer: B
Explanation:
Comprehensive and Detailed Explanation From FortiOS 7.6, FortiWeb 7.4 Exact Extract study guide:
Based on the FortiCNP 22.4/24.4 Administration Guide and the Fortinet Cloud Security Study Guide , findings in FortiCNP are categorized by the specific policy type that triggered the alert.
Threat Detection Policy (Option B): This policy category is designed to monitor and alert on anomalous User Activity and Network threats. Specifically, " Suspicious Location " is a predefined threat detection rule that triggers when a user performs an action (such as a Download File as seen in the exhibit) from a geographic location or IP address that is not on the organization ' s allow list or deviates from established behavioral baselines. The exhibit explicitly shows the " Activity Type " as " Download File " and the " Policy Name " as " Suspicious Location, " both of which fall under the Threat Detection > User Activity policy tab.
Policy Hierarchy and Finding Types:
Threat Detection: Includes User Activity (Suspicious Location, Suspicious Time, Suspicious Movement) and Network findings.
Data Scan Policy (Option A): These policies are used for content-level inspection, such as searching for Malware or Data Loss Prevention (DLP) patterns like credit card numbers within files.
Risk Management Policy (Option C): These policies focus on Cloud Security Posture Management (CSPM), alerting on misconfigurations such as unencrypted buckets or disabled logging (e.g., CloudTrail).
File Collection (Option D): While " File Collection " is a configuration object used to define a group of files for monitoring, it is not the policy type that generates a behavioral alert like " Suspicious Location " .
QUESTION DESCRIPTION:
What are two main features in Amazon Web Services (AWS) network access control lists (NACLs)? (Choose two answers)
Correct Answer & Rationale:
Answer: A, C
Explanation:
Comprehensive and Detailed Explanation From FortiOS 7.6, FortiWeb 7.4 Exact Extract study guide:
As per the FortiOS 7.6 AWS Administration Guide and FortiWeb 7.4 cloud deployment documentation, understanding the AWS infrastructure layer is critical for integrating Fortinet virtual appliances. The two features that define AWS Network Access Control Lists (NACLs) are:
Stateless Nature (Option A): Unlike Security Groups, which are stateful (automatically allowing return traffic), NACLs are stateless . This means that if you allow inbound traffic on a specific port, you must also explicitly configure an outbound rule to allow the response traffic to leave the subnet. NACLs evaluate inbound and outbound traffic independently.
Default Configuration (Option C): Every VPC comes with a default NACL . By default, this NACL is configured to allow all inbound and outbound traffic . This is designed to ensure connectivity is not blocked until a custom security posture is defined. However, any custom NACL created manually starts by denying all traffic until rules are added.
Why other options are incorrect:
Option B: NACLs are associated at the subnet level , not the instance level. Security Groups are the components tied directly to an instance’s Elastic Network Interface (ENI).
Option D: NACLs and Security Groups provide defense-in-depth and are designed to be used simultaneously. Traffic must pass through the NACL (subnet level) and then the Security Group (instance level) to reach its destination.
QUESTION DESCRIPTION:
A customer would like to use FortiGate fabric integration with FortiCNP. When adding a FortiGate VM to FortiCNP, which three mandatory configuration steps must you follow on FortiGate? (Choose three answers)
Correct Answer & Rationale:
Answer: C, D, E
Explanation:
Comprehensive and Detailed Explanation From FortiOS 7.6, FortiWeb 7.4 Exact Extract study guide:
According to the FortiCNP 24.x Administration Guide and the FortiOS 7.6 Security Fabric Integration documentation, integrating a FortiGate-VM with FortiCNP requires specific local configurations on the FortiGate to ensure the cloud security platform can ingest and analyze traffic data.
Configuring Logging (Option C): Before adding the FortiGate VM to FortiCNP, the administrator must Enable Send Logs on the FortiGate. This allows the FortiGate to forward the necessary security telemetry and traffic logs to the FortiCNP cloud endpoint for threat correlation and risk analysis.
Policy and Inspection Setup (Option D): The integration relies on the FortiGate ' s ability to identify and block threats at the network layer. Specifically, the administrator must Create a FortiGate IPS Sensor and Create a FortiGate Firewall Policy . The IPS sensor detects malicious patterns, while the firewall policy dictates which traffic is subjected to this inspection.
Deep Packet Inspection (Option E): To provide visibility into encrypted traffic—which is critical for identifying threats hidden in HTTPS flows—the administrator must Create an SSL/SSH Inspection Profile on the FortiGate. Without this profile, FortiCNP would lose significant visibility into potential attack vectors utilizing encrypted channels.
Why other options are incorrect:
Option A: While pre-shared keys are used in VPN and some Fabric setups, they are not listed as one of the specific mandatory steps for the initial FortiGate-to-FortiCNP fabric integration workflow.
Option B: While certificate exchange is part of the overall trust relationship, the primary " mandatory configuration steps on FortiGate " defined in the official setup guide focus on the logging and security profile components required to generate the data FortiCNP needs.
QUESTION DESCRIPTION:
Refer to the exhibit.
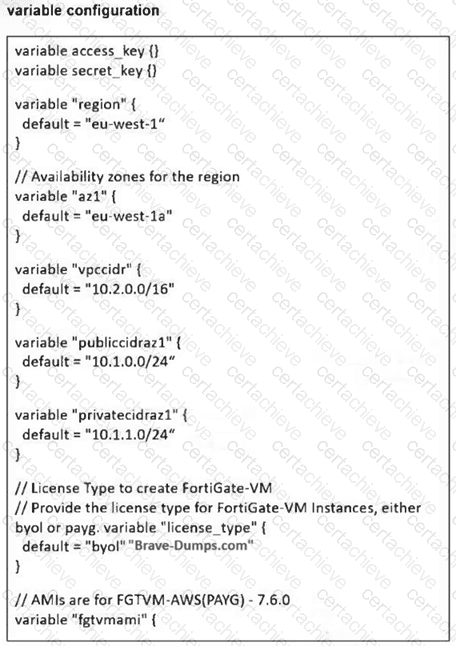
You are tasked to deploy a FortiGate VM with private and public subnets in Amazon Web Services (AWS). You examined the variables.tf file. Assume that all the other terraform files are in place. What will be the final result after running the terraform init and terraform apply commands? (Choose one answer)
Correct Answer & Rationale:
Answer: A
Explanation:
Comprehensive and Detailed Explanation From FortiOS 7.6, FortiWeb 7.4 Exact Extract study guide:
Based on the FortiOS 7.6 AWS Administration Guide and the Fortinet 7.4 Public Cloud Security documentation regarding Terraform deployments:
Variable Validation and Logic (Option A): The variables.tf file contains a logic error that prevents a successful deployment.
Specifically, the variable license_type has a default value defined as " byol " " Brave-Dumps.com " .
In Terraform HCL (HashiCorp Configuration Language), a variable ' s default attribute can only hold a single value string (e.g., " byol " ). The inclusion of the secondary string " Brave-Dumps.com " within the same default assignment is a syntax error.
Impact on Execution: When terraform apply is executed, the Terraform engine performs a validation check on all loaded files. Because of this syntax error in the variable definition, the validation will fail, and Terraform will stop execution with an error message before any resources—including the FortiGate VM—are created in AWS.
Network Mismatch: Additionally, the variable vpccidr is set to 10.2.0.0/16, while the public (10.1.0.0/24) and private (10.1.1.0/24) subnets are defined within a completely different address space (10.1.x.x). Even if the syntax error were fixed, the deployment would likely fail at the infrastructure level because subnets must reside within the CIDR block of their parent VPC.
Why other options are incorrect:
Option B, C, & D: None of these successful deployment outcomes can occur because the Terraform parser will identify the invalid syntax in the variables.tf file and abort the process entirely.
A Stepping Stone for Enhanced Career Opportunities
Your profile having Fortinet Network Security Expert certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Fortinet NSE7_CDS_AR-7.6 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Fortinet Exam NSE7_CDS_AR-7.6
Achieving success in the NSE7_CDS_AR-7.6 Fortinet exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in NSE7_CDS_AR-7.6 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam NSE7_CDS_AR-7.6!
In the backdrop of the above prep strategy for NSE7_CDS_AR-7.6 Fortinet exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding NSE7_CDS_AR-7.6 exam prep. Here's an overview of Certachieve's toolkit:
Fortinet NSE7_CDS_AR-7.6 PDF Study Guide
This premium guide contains a number of Fortinet NSE7_CDS_AR-7.6 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Fortinet NSE7_CDS_AR-7.6 study guide pdf free download is also available to examine the contents and quality of the study material.
Fortinet NSE7_CDS_AR-7.6 Practice Exams
Practicing the exam NSE7_CDS_AR-7.6 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Fortinet NSE7_CDS_AR-7.6 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Fortinet NSE7_CDS_AR-7.6 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning NSE7_CDS_AR-7.6 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Fortinet NSE7_CDS_AR-7.6 Fortinet Network Security Expert FAQ
There are only a formal set of prerequisites to take the NSE7_CDS_AR-7.6 Fortinet exam. It depends of the Fortinet organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Fortinet NSE7_CDS_AR-7.6 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Fortinet NSE7_CDS_AR-7.6 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Fortinet NSE7_CDS_AR-7.6 exam dumps to enhance your readiness for the exam.
Like any other Fortinet Certification exam, the Fortinet Network Security Expert is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do NSE7_CDS_AR-7.6 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The NSE7_CDS_AR-7.6 Fortinet exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Fortinet NSE7_CDS_AR-7.6 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Fortinet has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Fortinet changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



