The FortiGate 7.6 Administrator FCP_FGT_AD-7.6 (FCP_FGT_AD-7.6)
Passing Fortinet Fortinet Network Security Expert exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard FCP_FGT_AD-7.6 Dumps
In 2026, Fortinet uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Fortinet FCP_FGT_AD-7.6 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
Refer to the exhibits.
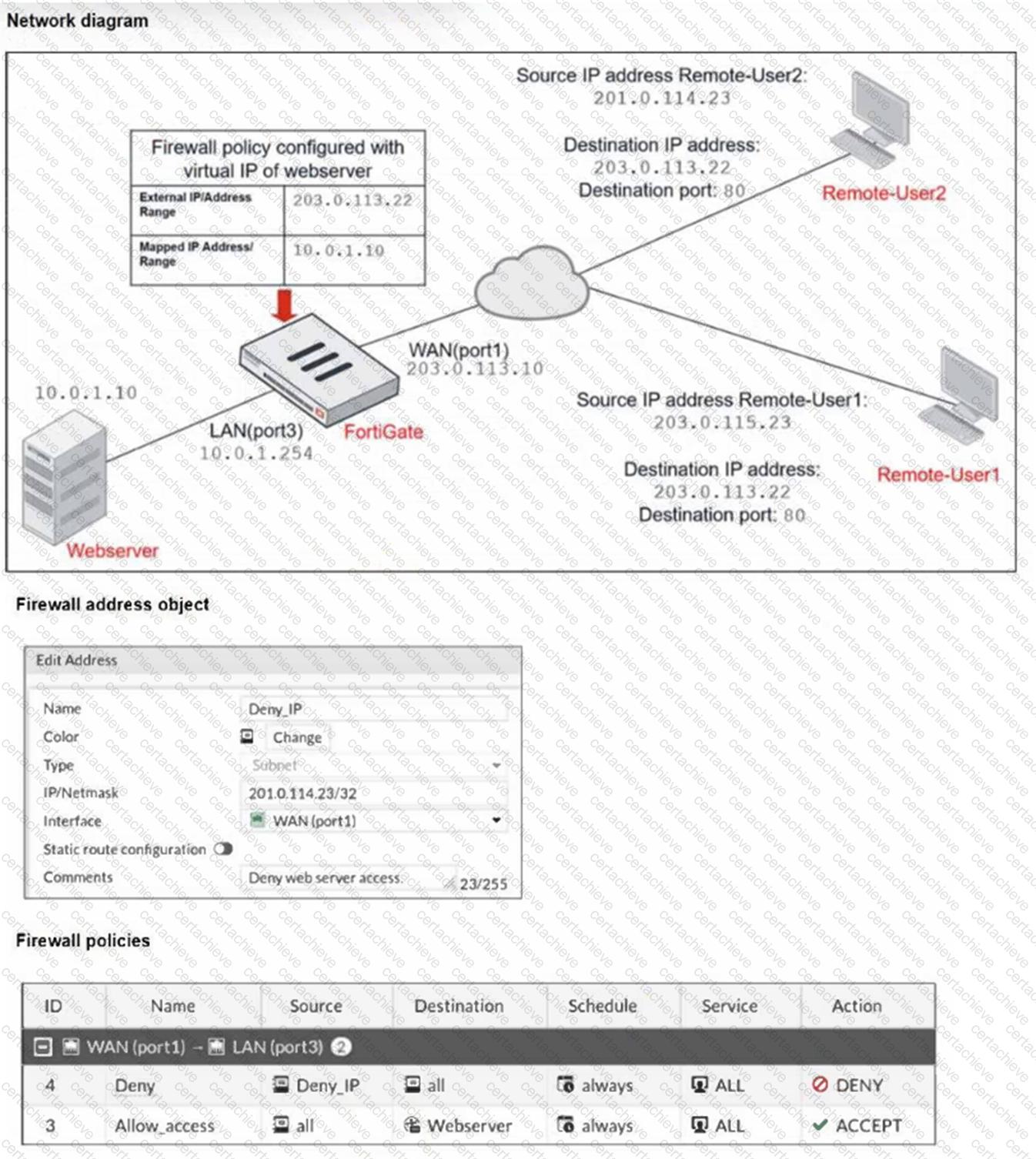
The exhibits show a diagram of a FortiGate device connected to the network, and the firewall configuration.
An administrator created a Deny policy with default settings to deny Webserver access for Remote-User2 .
The policy should work such that Remote-User1 must be able to access the Webserver while preventing Remote-User2 from accessing the Webserver .
Which additional configuration can the administrator add to a deny firewall policy, beyond the default behavior, to block Remote-User2 from accessing the Webserver ?
Correct Answer & Rationale:
Answer: C
Explanation:
To block Remote-User2 ' s access to the Webserver, the deny policy must explicitly specify the Webserver as the destination address; otherwise, it denies traffic to all destinations, which is not the desired behavior.
QUESTION DESCRIPTION:
Which three statements explain a flow-based antivirus profile? (Choose three.)
Correct Answer & Rationale:
Answer: A, B, D
Explanation:
Flow-based antivirus buffers the entire file while simultaneously transmitting data to the client to minimize latency.
Flow-based inspection combines multiple scanning techniques from proxy-based modes for efficient detection.
Flow-based inspection provides better performance by processing traffic on the fly without full proxy overhead.
QUESTION DESCRIPTION:
Refer to the exhibit.
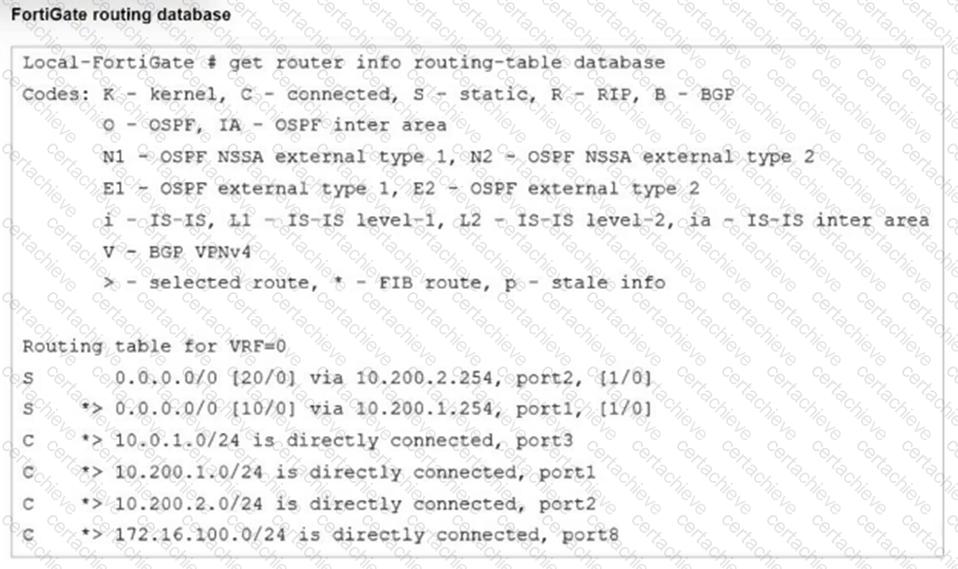
Which two statements are true about the routing entries in this database table? (Choose two.)
Correct Answer & Rationale:
Answer: C, D
Explanation:
The routing table in the exhibit shows two default routes (0.0.0.0/0) with different administrative distances:
The default route through port2 has an administrative distance of 20.
The default route through port1 has an administrative distance of 10.
Administrative distance determines the priority of the route; a lower value is preferred. Here, the route through port1 with an administrative distance of 10 is the preferred route. The route through port2 with an administrative distance of 20 acts as a standby or backup route. If the primary route ( port1 ) fails or is unavailable, traffic will then be routed through port2 .
Regarding the statement that the port2 interface is marked as inactive, there is no indication in the routing table that port2 is inactive. Similarly, all the routes displayed are not necessarily installed in the FortiGate routing table, as the table could include both active and backup routes.
QUESTION DESCRIPTION:
You have configured an application control profile, set peer-to-peer traffic to Block under the Categories tab, and applied it to the firewall policy. However, your peer-to-peer traffic on known ports is passing through the FortiGate without being blocked.
What FortiGate settings should you check to resolve this issue?
Correct Answer & Rationale:
Answer: C
Explanation:
Network Protocol Enforcement settings control how FortiGate inspects and enforces protocols on traffic, including peer-to-peer applications on known ports. If not properly enabled, peer-to-peer traffic may bypass blocking despite the application control profile.
QUESTION DESCRIPTION:
When configuring a FortiGate in a multi-WAN setup, why would an administrator enable session preservation on an interface?
Correct Answer & Rationale:
Answer: D
Explanation:
Session preservation keeps active sessions, such as SSL VPNs, tied to the original interface to prevent disruption when WAN routes change.
QUESTION DESCRIPTION:
Refer to the exhibits.
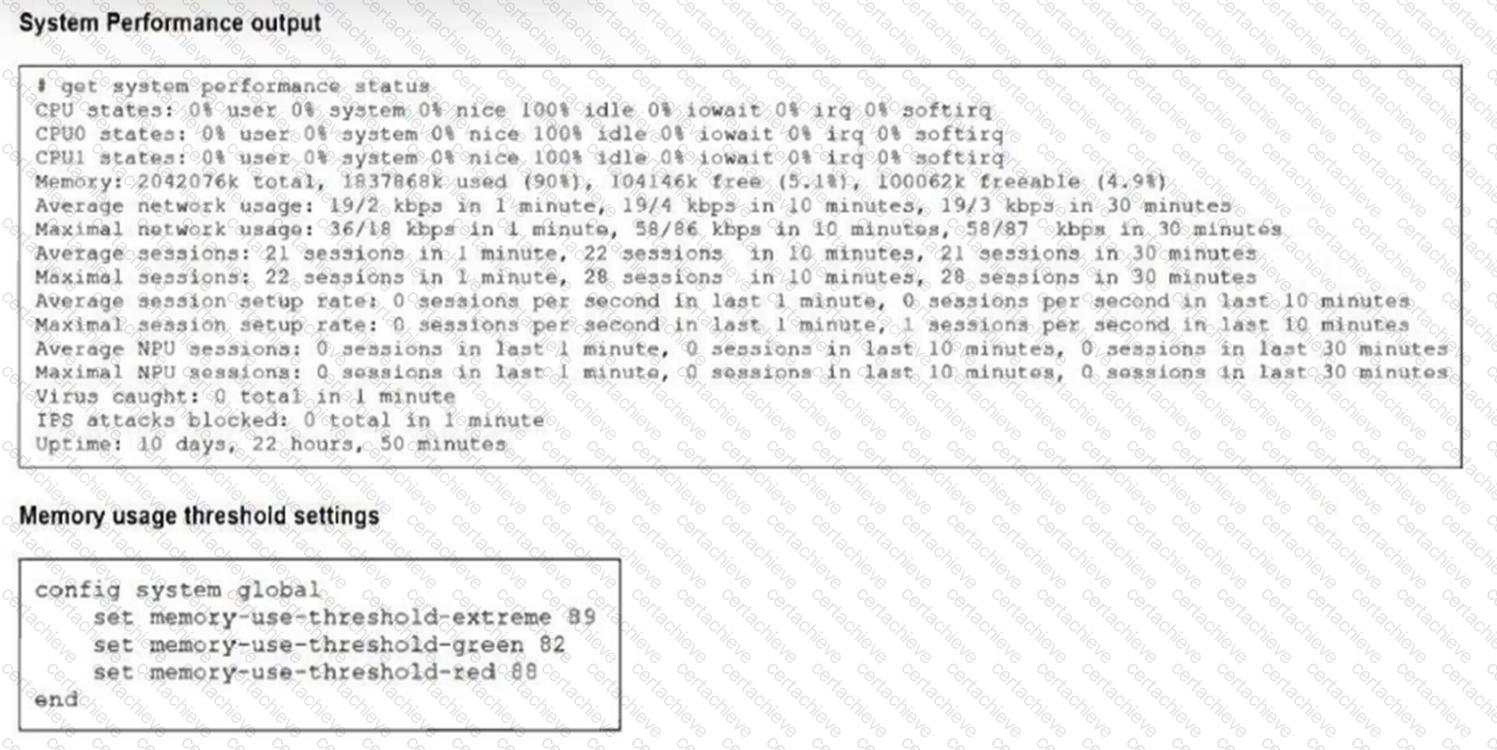
The exhibits show the system performance output and default configuration of high memory usage thresholds on a FortiGate device.
Based on the system performance output, what are the two possible outcomes? (Choose two.)
Correct Answer & Rationale:
Answer: C, D
Explanation:
Since memory usage is at 90%, exceeding the red threshold (88%), FortiGate enters a state where configuration changes are still allowed.
In this state, FortiGate drops new sessions to preserve resources and maintain stability.
QUESTION DESCRIPTION:
Refer to the exhibit, which shows an SD-WAN zone configuration on the FortiGate GUI.

Based on the exhibit, which statement is true?
Correct Answer & Rationale:
Answer: B
Explanation:
The Underlay zone is the default SD-WAN zone, typically representing the physical interfaces in the SD-WAN configuration before overlay or virtual links are added.
QUESTION DESCRIPTION:
Refer to the exhibits.
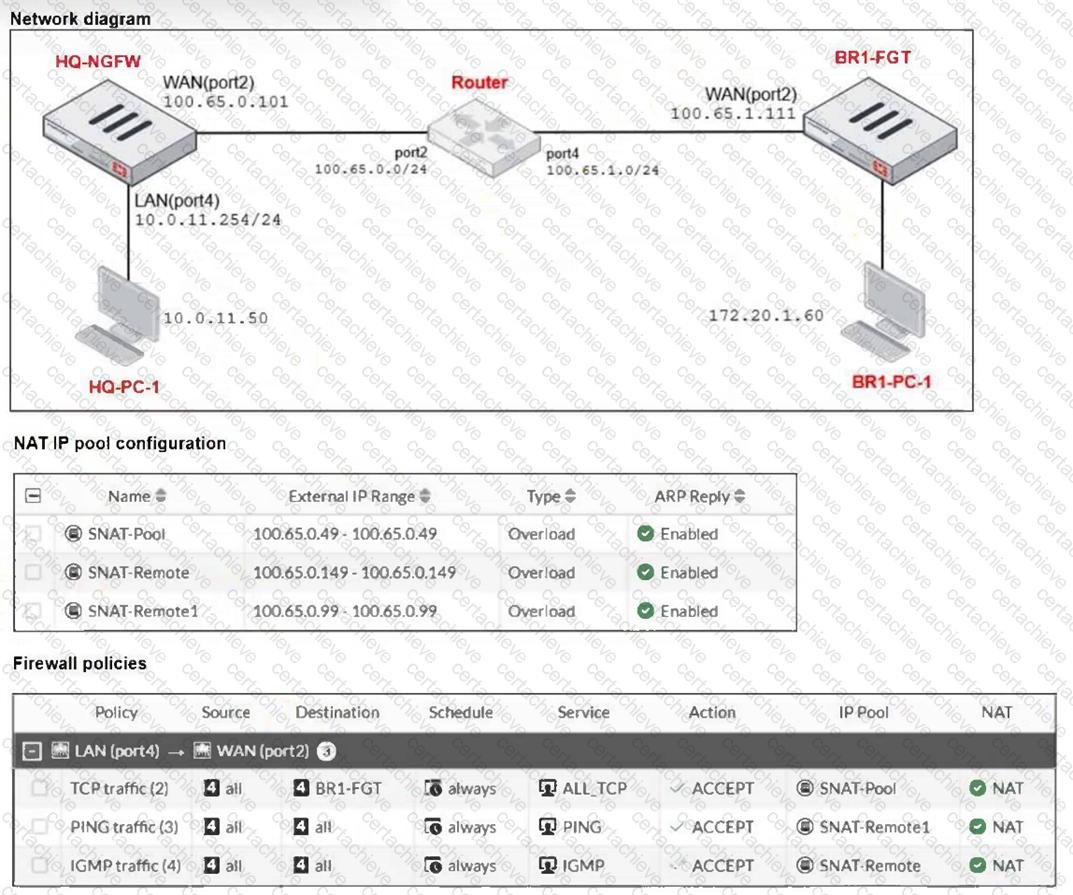
The exhibits show a diagram of a FortiGate device connected to the network, as well as the IP pool configuration and firewall policy objects.
The WAN (port2) interface has the IP address 100.65.0.101/24 .
The LAN (port4) interface has the IP address 10.0.11.254/24 .
Which IP address will be used to source NAT (SNAT) the traffic, if the user on
HQ-PC-1 ( 10.0.11.50 ) pings the IP address of BR-FGT ( 100.65.1.111 )
Correct Answer & Rationale:
Answer: C
Explanation:
The ping traffic policy uses the IP pool named SNAT-Remote1, which has the external IP range 100.65.0.99. Therefore, traffic matching this policy (ping from HQ-PC-1 to BR1-FGT) will use 100.65.0.99 for source NAT.
QUESTION DESCRIPTION:
What is the primary FortiGate election process when the HA override setting is enabled?
Correct Answer & Rationale:
Answer: A
Explanation:
When HA override is enabled, FortiGate uses the following election order: number of connected monitored ports, then device priority, followed by HA uptime, and finally FortiGate serial number as a tiebreaker.
QUESTION DESCRIPTION:
A network administrator is reviewing firewall policies in both Interface Pair View and By Sequence View. The policies appear in a different order in each view.
Why is the policy order different in these two views?
Correct Answer & Rationale:
Answer: D
Explanation:
Interface Pair View organizes policies grouped by source and destination interfaces, whereas By Sequence View displays policies in the exact order they are processed by the firewall.
A Stepping Stone for Enhanced Career Opportunities
Your profile having Fortinet Network Security Expert certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Fortinet FCP_FGT_AD-7.6 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Fortinet Exam FCP_FGT_AD-7.6
Achieving success in the FCP_FGT_AD-7.6 Fortinet exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in FCP_FGT_AD-7.6 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam FCP_FGT_AD-7.6!
In the backdrop of the above prep strategy for FCP_FGT_AD-7.6 Fortinet exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding FCP_FGT_AD-7.6 exam prep. Here's an overview of Certachieve's toolkit:
Fortinet FCP_FGT_AD-7.6 PDF Study Guide
This premium guide contains a number of Fortinet FCP_FGT_AD-7.6 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Fortinet FCP_FGT_AD-7.6 study guide pdf free download is also available to examine the contents and quality of the study material.
Fortinet FCP_FGT_AD-7.6 Practice Exams
Practicing the exam FCP_FGT_AD-7.6 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Fortinet FCP_FGT_AD-7.6 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Fortinet FCP_FGT_AD-7.6 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning FCP_FGT_AD-7.6 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Fortinet FCP_FGT_AD-7.6 Fortinet Network Security Expert FAQ
There are only a formal set of prerequisites to take the FCP_FGT_AD-7.6 Fortinet exam. It depends of the Fortinet organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Fortinet FCP_FGT_AD-7.6 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Fortinet FCP_FGT_AD-7.6 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Fortinet FCP_FGT_AD-7.6 exam dumps to enhance your readiness for the exam.
Like any other Fortinet Certification exam, the Fortinet Network Security Expert is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do FCP_FGT_AD-7.6 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The FCP_FGT_AD-7.6 Fortinet exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Fortinet FCP_FGT_AD-7.6 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Fortinet has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Fortinet changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



