The Cisco Certified Support Technician (CCST) Cybersecurity (100-160)
Passing Cisco CCST exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard 100-160 Dumps
In 2026, Cisco uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Cisco 100-160 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
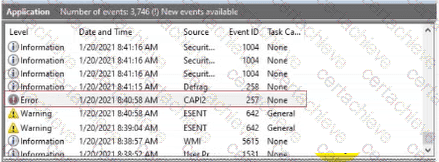
You are reviewing the Application log on a Windows computer. You see an event with an error-level message as shown.
What can you determine about the application that generated the event message?
Correct Answer & Rationale:
Answer: B
Explanation:
In the CCST Cybersecurity course, Windows Event Viewer Error events in the Application log indicate a severe problem that caused an application or component to fail. This usually requires investigation or repair.
"Error events indicate a significant problem such as a loss of functionality in an application or system component. Errors are often critical and need immediate attention."
(CCST Cybersecurity, Incident Handling , Event Logging and Analysis section, Cisco Networking Academy)
A is incorrect: Performance slowness would usually generate warnings, not errors.
B is correct: An "Error" level in Event Viewer means the application failed in some way.
C is incorrect: That describes an "Information" event, not an error.
D is incorrect: That also corresponds to an "Information" event.
QUESTION DESCRIPTION:
During an incident response, the security team needs to isolate a compromised server from the rest of the network but still allow forensic analysis. Which action should they take?
Correct Answer & Rationale:
Answer: B
Explanation:
The CCST Cybersecurity course notes that isolation is a key part of the containment phase of incident response. The goal is to prevent the compromised system from communicating with the attacker or spreading malware, while preserving it for analysis.
"Containment often involves removing an affected system from the production network and connecting it to a controlled forensic environment to preserve evidence and prevent further compromise."
(CCST Cybersecurity, Incident Handling , Containment Procedures section, Cisco Networking Academy)
QUESTION DESCRIPTION:
The company web server collects information through a form. The form is accessed by using port 80. The form content is transferred to an encrypted database for storage. You are investigating a complaint that the form content has been compromised.
What is the cause of the security breach?
Correct Answer & Rationale:
Answer: C
Explanation:
The CCST Cybersecurity Study Guide explains that HTTP (port 80) transmits data in cleartext, making it susceptible to interception. Even if data is stored securely in an encrypted database, sensitive information can be compromised during transmission if HTTPS (port 443) is not used.
"When HTTP is used instead of HTTPS, all form inputs and transmitted data are sent in plaintext over the network, where they can be intercepted by attackers."
(CCST Cybersecurity, Basic Network Security Concepts , Secure Protocols section, Cisco Networking Academy)
QUESTION DESCRIPTION:
You work for a hospital that stores electronic protected health information (ePHI) in an online portal. Authorized employees can use their mobile devices to access patient ePHI.
You need to ensure that employees’ mobile devices comply with HIPAA regulations.
Which safeguard should you develop and implement?
Correct Answer & Rationale:
Answer: D
Explanation:
The CCST Cybersecurity Study Guide notes that HIPAA (Health Insurance Portability and Accountability Act) requires that ePHI be protected both in storage and when devices are decommissioned or repurposed. This includes implementing data removal policies for mobile devices.
"HIPAA requires procedures for the removal of electronic protected health information (ePHI) from devices before disposal, reuse, or reassignment."
(CCST Cybersecurity, Essential Security Principles , Regulatory Compliance section, Cisco Networking Academy)
QUESTION DESCRIPTION:
You are planning to work from home. Your company requires that you connect to the company network through a VPN.
Which three critical functions do VPNs provide to remote workers? (Choose 3.)
Correct Answer & Rationale:
Answer: C, D, E
Explanation:
The CCST Cybersecurity material states that a Virtual Private Network (VPN) provides secure communication over an untrusted network, typically by ensuring:
Authentication → verifying the identity of the user/device
Confidentiality → encrypting the data so it cannot be read by unauthorized parties
Integrity → ensuring that transmitted data has not been altered in transit
"VPNs secure remote access by authenticating users, encrypting data for confidentiality, and ensuring integrity through cryptographic checks."
(CCST Cybersecurity, Basic Network Security Concepts , VPNs section, Cisco Networking Academy)
A is incorrect: WAN management is a network administration function, not a VPN feature.
B is incorrect: Authorization is related but not a primary VPN security function.
C is correct: Integrity is preserved through cryptographic hashing.
D is correct: Authentication verifies user identity.
E is correct: Confidentiality is provided via encryption.
F is incorrect: Password management is separate from VPN functions.
QUESTION DESCRIPTION:
Which two basic metrics should be taken into consideration when assigning a severity to a vulnerability during an assessment? (Choose 2.)
Correct Answer & Rationale:
Answer: A, B
Explanation:
The CCST Cybersecurity course describes that risk scoring for vulnerabilities often involves likelihood and impact — similar to the CVSS (Common Vulnerability Scoring System) model.
"When prioritizing vulnerabilities, assess both the likelihood of exploitation and the potential impact to the organization. Likelihood measures how easy or probable it is for an adversary to exploit the weakness, while impact measures the consequences to confidentiality, integrity, and availability if exploitation occurs."
(CCST Cybersecurity, Vulnerability Assessment and Risk Management , Risk Assessment and Prioritization section, Cisco Networking Academy)
A is correct: Likelihood is a fundamental part of severity assessment.
B is correct: Impact determines how damaging an exploit would be.
C is incorrect: Time to choose replacement software is an operational consideration, not a severity metric.
D is incorrect: Hardware age may influence performance but does not directly define vulnerability severity.
QUESTION DESCRIPTION:
A SOC analyst notices repeated failed login attempts from a foreign IP address followed by a successful login to a privileged account. What is the most appropriate next step?
Correct Answer & Rationale:
Answer: A
Explanation:
The CCST Cybersecurity course highlights that signs of brute-force attacks followed by successful access require immediate account security actions and an investigation to determine if other systems were accessed.
"When suspicious login activity is detected, immediate containment steps such as password resets and log analysis are necessary to limit damage and identify the extent of the compromise."
(CCST Cybersecurity, Incident Handling , Account Compromise Response section, Cisco Networking Academy)
QUESTION DESCRIPTION:
What should you create to prevent spoofing of the internal network?
Correct Answer & Rationale:
Answer: B
Explanation:
The CCST Cybersecurity Study Guide states that Access Control Lists (ACLs) can be used to filter traffic based on IP addresses and block packets that appear to originate from the internal network but arrive from external interfaces (IP spoofing).
"ACLs can prevent spoofing by dropping traffic from external sources that claim to have an internal source address. Configuring ACLs on the perimeter firewall or router is a common countermeasure for IP spoofing."
(CCST Cybersecurity, Basic Network Security Concepts , ACLs and Traffic Filtering section, Cisco Networking Academy)
A (NAT rule) changes IP addresses but does not inherently prevent spoofing.
B (ACL) is correct because it can enforce anti-spoofing filters.
C (host file) only affects name resolution locally.
D (DNS record) is for domain mapping, not spoofing prevention.
QUESTION DESCRIPTION:
An employee accidentally sends an email containing sensitive corporate information to an external email address.
Which type of threat does this scenario describe?
Correct Answer & Rationale:
Answer: D
Explanation:
The CCST Cybersecurity Study Guide explains that an insider threat is any threat to an organization that comes from people within the organization—employees, contractors, or business partners—who have inside information concerning the organization's security practices, data, and systems. Insider threats may be intentional or unintentional.
"An insider threat can be malicious or accidental. Employees may unintentionally cause data breaches by mishandling sensitive information, such as sending it to the wrong recipient."
(CCST Cybersecurity, Essential Security Principles , Threat Actor Types section, Cisco Networking Academy)
A (Logic bomb) is malicious code triggered by conditions.
B (Malware) is malicious software, unrelated to accidental email leaks.
C (Phishing) is an external social engineering attack.
D is correct: This is an unintentional insider threat .
QUESTION DESCRIPTION:
You need a software solution that performs the following tasks:
Compiles network data
Logs information from many sources
Provides orchestration in the form of case management
Automates incident response workflows
What product should you use?
Correct Answer & Rationale:
Answer: B
Explanation:
The CCST Cybersecurity Study Guide explains that SOAR (Security Orchestration, Automation, and Response) platforms integrate data from multiple tools and sources, support case management, and automate security workflows for faster incident response.
"SOAR solutions provide orchestration, automation, and response capabilities. They collect security data from multiple systems, enable analysts to manage incidents, and automate repetitive tasks in the response process."
(CCST Cybersecurity, Incident Handling , Security Automation Tools section, Cisco Networking Academy)
A (SIEM) collects and correlates security logs but lacks full orchestration and automated response capabilities.
B is correct: SOAR adds orchestration, case management, and automated incident response.
C (NextGen IPS) focuses on intrusion prevention, not orchestration.
D (Snort) is an open-source intrusion detection/prevention tool, not an orchestration platform.
A Stepping Stone for Enhanced Career Opportunities
Your profile having CCST certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Cisco 100-160 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Cisco Exam 100-160
Achieving success in the 100-160 Cisco exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in 100-160 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam 100-160!
In the backdrop of the above prep strategy for 100-160 Cisco exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding 100-160 exam prep. Here's an overview of Certachieve's toolkit:
Cisco 100-160 PDF Study Guide
This premium guide contains a number of Cisco 100-160 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Cisco 100-160 study guide pdf free download is also available to examine the contents and quality of the study material.
Cisco 100-160 Practice Exams
Practicing the exam 100-160 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Cisco 100-160 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Cisco 100-160 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning 100-160 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Cisco 100-160 CCST FAQ
There are only a formal set of prerequisites to take the 100-160 Cisco exam. It depends of the Cisco organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Cisco 100-160 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Cisco 100-160 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Cisco 100-160 exam dumps to enhance your readiness for the exam.
Like any other Cisco Certification exam, the CCST is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do 100-160 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The 100-160 Cisco exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Cisco 100-160 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Cisco has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Cisco changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



