The Implementing and Administering Cisco Solutions (200-301 CCNA) v1.1 (200-301)
Passing Cisco CCNA exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard 200-301 Dumps
In 2026, Cisco uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official Cisco 200-301 Exam Domains
Our curriculum is meticulously mapped to the Cisco official blueprint.
IP Connectivity (25%)
Master OSPFv2 configuration, Static Routing, and Inter-VLAN routing logic.
Network Access (20%)
Detailed coverage of STP, EtherChannel, and Wireless Architectures.
Security Fundamentals (15%)
Mastering WPA3, DHCP Snooping, Dynamic ARP Inspection (DAI), and SSH protocols.
Automation & Programmability (10%)
Understanding JSON, REST APIs, Puppet, Chef, and SDN Controllers.
Cisco 200-301 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
A network engineer is configuring a switch so that it is remotely reachable via SSH. The engineer has already configured the host name on the router. Which additional command must the engineer configure before entering the command to generate the RSA key?
Correct Answer & Rationale:
Answer: C
Explanation:
https://www.cisco.com/c/en/us/solutions/small-business/resource-center/networking/how-to-setup-network-switch.html
QUESTION DESCRIPTION:
What is a function of an endpoint on a network?
Correct Answer & Rationale:
Answer: C
Explanation:
An endpoint is a host that acts as the source or destination of data traffic flowing through a network.
When you are at your PC, editing your CV and uploading it to a file server, you are sitting at an endpoint.
QUESTION DESCRIPTION:
Which security protocol is appropriate for a WPA3 implementation?
Correct Answer & Rationale:
Answer: D
Explanation:
WPA3 uses stronger encryption and security mechanisms than WPA2. The protocol associated with WPA3 is GCMP.
GCMP (Galois/Counter Mode Protocol) is used with WPA3.
It provides stronger security and better performance than older protocols.
A. CCMP: associated mainly with WPA2, not WPA3.
B. MD5: a hashing algorithm, not a WPA3 wireless encryption protocol.
C. TKIP: older and insecure; used with WPA/WPA2 legacy environments, not WPA3.
WPA2 → CCMP
WPA3 → GCMP
Why D is correct:Why the others are incorrect:CCNA takeaway:
QUESTION DESCRIPTION:
Which technology is appropriate for communication between an SDN controller and applications running over the network?
Correct Answer & Rationale:
Answer: A
Explanation:
In an SDN architecture, the SDN controller sits between the network infrastructure and the applications.
There are two main API directions:
Northbound APIs: between the SDN controller and applications
Southbound APIs: between the SDN controller and network devices
Applications communicate with the controller using northbound APIs, and these are commonly implemented as REST APIs.
REST API is the common method used by applications to interact with the SDN controller.
It allows software and orchestration platforms to request network information or make policy changes through HTTP-based calls.
B. OpenFlow: used between the controller and network devices, not applications.
C. Southbound API: this refers to controller-to-device communication, not controller-to-application communication.
D. NETCONF: used for device configuration and management, typically between controllers/management platforms and devices, not primarily for app-to-controller communication.
Why A is correct:Why the others are incorrect:CCNA takeaway:If the question asks about applications talking to the SDN controller, think:
Northbound API → usually REST API
QUESTION DESCRIPTION:
What is used to identify spurious DHCP servers?
Correct Answer & Rationale:
Answer: D
Explanation:
DHCPOFFER is used to identify spurious DHCP servers. A spurious DHCP server is any device that is configured to act as a DHCP server without the network administrator’s knowledge or permission. A spurious DHCP server can cause network problems by assigning incorrect or duplicate IP addresses to clients, or by redirecting traffic to malicious gateways. To prevent such attacks, the DHCP snooping feature can be enabled on switches to filter out invalid or unauthorized DHCP messages from untrusted sources1.
DHCP snooping works by intercepting and validating DHCP messages on a per-VLAN basis. The switch maintains a DHCP snooping binding database that contains information about the trusted hosts with leased IP addresses, such as MAC address, IP address, lease time, binding type, VLAN number, and interface information2. The switch also classifies its ports as trusted or untrusted. Trusted ports are those that connect to authorized DHCP servers or other trusted switches. Untrusted ports are those that connect to untrusted hosts or devices. The switch only allows DHCP messages from trusted ports, and drops any DHCP messages from untrusted ports that do not match the information in the binding database3.
The switch uses DHCPOFFER messages to identify spurious DHCP servers. A DHCPOFFER message is a response from a DHCP server to a client’s request for an IP address. The message contains the offered IP address, subnet mask, default gateway, and other configuration parameters for the client4. When the switch receives a DHCPOFFER message from an untrusted port, it compares the source MAC address and the offered IP address with the binding database. If there is no match, the switch considers the message as coming from a spurious DHCP server and drops it. The switch also logs an error message and increments a counter for the number of dropped messages5.
QUESTION DESCRIPTION:
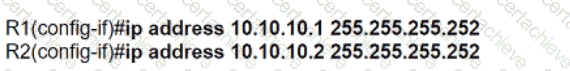
Refer to the exhibit.
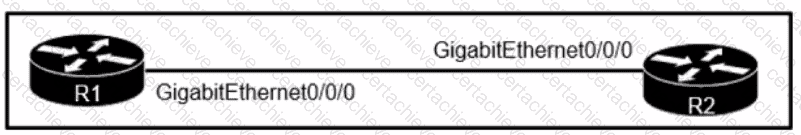
A network engineer must configure the link with these requirements:
• Consume as few IP addresses as possible.
• Leave at least two additional useable IP addresses for future growth.
Which set of configurations must be applied?
A)
B)
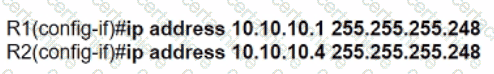
C)
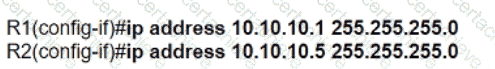
D)
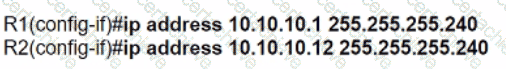
Correct Answer & Rationale:
Answer: B
Explanation:
We have to configure the link which will need 2 IP addresses, 1 for each port on each Router. We also need 2 spare IPs for future growth, so overall we need 4 usable IP addresses. If we consider using the /30 (255.255.255.252) mask, it will give us 2^2 (=4) i.e., total 4 IPs and 2 usable IPs, which doesn’t fulfil the given requirements. So, we can consider using the next /29 (255.255.255.248) mask, which gives us 2^3 (=8) i.e., total 8 IP address and 6 usable IP addresses, which perfectly fulfil the given requirements.
QUESTION DESCRIPTION:
Which REST method updates an object in the Cisco DNA Center Intent API?
Correct Answer & Rationale:
Answer: D
Explanation:
PUT is most-often utilized for **update** capabilities, PUT-ing to a known resource URI with the request body containing the newly-updated representation of the original resource.
However, PUT can also be used to create a resource in the case where the resource ID is chosen by the client instead of by the server. In other words, if the PUT is to a URI that contains the value of a non-existent resource ID. Again, the request body contains a resource representation. Many feel this is convoluted and confusing. Consequently, this method of creation should be used sparingly, if at all.
Alternatively, use POST to create new resources and provide the client-defined ID in the body representation—presumably to a URI that doesn’t include the ID of the resource (see POST below).
On successful update, return 200 (or 204 if not returning any content in the body) from a PUT. If using PUT for create, return HTTP status 201 on successful creation. A body in the response is optional—providing one consumes more bandwidth. It is not necessary to return a link via a Location header in the creation case since the client already set the resource ID.
PUT is not a safe operation, in that it modifies (or creates) state on the server, but it is idempotent. In other words, if you create or update a resource using PUT and then make that same call again, the resource is still there and still has the same state as it did with the first call.
If, for instance, calling PUT on a resource increments a counter within the resource, the call is no longer idempotent. Sometimes that happens and it may be enough to document that the call is not idempotent. However, it’s recommended to keep PUT requests idempotent. It is strongly recommended to use POST for non-idempotent requests.
Examples:
https://www.restapitutorial.com/lessons/httpmethods.html
QUESTION DESCRIPTION:
Which device separates networks by security domains?
Correct Answer & Rationale:
Answer: A
Explanation:
Firewalls are devices that are used to separate networks into different security domains. They act as a barrier between two networks and control the flow of traffic between them. Firewalls use a set of rules to determine what types of traffic are allowed to pass through and what is blocked. This helps protect a network from malicious traffic and unauthorized access. Additionally, firewalls can be configured to log traffic and provide additional security measures such as packet filtering and stateful inspection.
QUESTION DESCRIPTION:
Which IPsec encryption mode is appropriate when the destination of a packet differs from the security termination point?
Correct Answer & Rationale:
Answer: B
Explanation:
IPsec encryption mode is the way IPsec secures the data packets that are sent over an IP network. There are two main modes of IPsec encryption: tunnel mode and transport mode1. Tunnel mode encrypts the entire IP packet, including the original header, and adds a new IP header with the source and destination addresses of the security gateways (routers, firewalls, or VPN servers) that perform the encryption and decryption2. Transport mode encrypts only the payload (data) of the IP packet, leaving the original header intact, and uses the original source and destination addresses of the endpoints that generate and consume the data3. Therefore, transport mode is appropriate when the destination of a packet differs from the security termination point, as it does not change the original IP header information. Tunnel mode is more suitable when the security termination point is also the destination of the packet, as it provides more protection for the original IP header information.
QUESTION DESCRIPTION:
Which virtual MAC address is used by VRRP group 1?
Correct Answer & Rationale:
Answer: C
Explanation:
The virtual router MAC address associated with a virtual router is an
IEEE 802 MAC Address in the following format:
00-00-5E-00-01-{VRID} (in hex in internet standard bit-order)
A Stepping Stone for Enhanced Career Opportunities
Your profile having CCNA certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Cisco 200-301 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Cisco Exam 200-301
Achieving success in the 200-301 Cisco exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in 200-301 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam 200-301!
In the backdrop of the above prep strategy for 200-301 Cisco exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding 200-301 exam prep. Here's an overview of Certachieve's toolkit:
Cisco 200-301 PDF Study Guide
This premium guide contains a number of Cisco 200-301 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Cisco 200-301 study guide pdf free download is also available to examine the contents and quality of the study material.
Cisco 200-301 Practice Exams
Practicing the exam 200-301 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Cisco 200-301 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Cisco 200-301 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning 200-301 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Jack
Mar 11, 2026
Noah
Mar 11, 2026
Oliver
Mar 11, 2026
James
Mar 11, 2026
Cisco 200-301 CCNA FAQ
There are only a formal set of prerequisites to take the 200-301 Cisco exam. It depends of the Cisco organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Cisco 200-301 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Cisco 200-301 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Cisco 200-301 exam dumps to enhance your readiness for the exam.
Like any other Cisco Certification exam, the CCNA is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do 200-301 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The 200-301 Cisco exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Cisco 200-301 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Cisco has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Cisco changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor
Verified Performance Reports
Authentic score reports from candidates who cleared the 200-301 exam.