The Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR) (300-215)
Passing Cisco CyberOps Professional exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard 300-215 Dumps
In 2026, Cisco uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Cisco 300-215 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
What can the blue team achieve by using Hex Fiend against a piece of malware?
Correct Answer & Rationale:
Answer: A
Explanation:
Hex Fiend is a hex editor that allows analysts to examine the raw byte content of files. One key use case is identifying and extracting byte-level patterns or signatures that can be translated into YARA rules for detecting malware. These hex patterns can be used to define precise signature-based detections.
QUESTION DESCRIPTION:
An employee receives an email from a “trusted” person containing a hyperlink that is malvertising. The employee clicks the link and the malware downloads. An information analyst observes an alert at the SIEM and engages the cybersecurity team to conduct an analysis of this incident in accordance with the incident response plan. Which event detail should be included in this root cause analysis?
Correct Answer & Rationale:
Answer: A
Explanation:
The root cause analysis in incident response focuses on identifying the initial trigger or root cause of the incident to understand how it started and how to prevent recurrence. In this scenario, the phishing email sent to the victim (A) is the initial trigger that led to the employee’s action of clicking the malvertising link, resulting in the malware download.
The other options represent later stages in the incident response cycle, such as detection (SIEM alert, cybersecurity team’s alert) or supporting evidence (email header information), but they do not address the root cause, which is the phishing email itself .
This aligns with the CyberOps Technologies (CBRFIR) 300-215 study guide , which states that identifying the initial vector of compromise is critical to the root cause analysis phase of incident response (Chapter: Incident Response Techniques, page 410-412).
QUESTION DESCRIPTION:
Which type of record enables forensics analysts to identify fileless malware on Windows machines?
Correct Answer & Rationale:
Answer: C
Explanation:
Fileless malware operates in memory and often leverages legitimate tools such as PowerShell to avoid traditional file-based detection. Since these threats don ' t leave typical file traces, analysts must rely on PowerShell event logs to trace suspicious or unauthorized script execution.
The Cisco CyberOps Associate guide explicitly states:
“PowerShell logs provide insight into script block execution and can reveal indicators of fileless attacks that reside in memory.”
Hence, PowerShell event logs are the most effective forensic source for detecting fileless malware activity on Windows systems.
QUESTION DESCRIPTION:
Over the last year, an organization’s HR department has accessed data from its legal department on the last day of each month to create a monthly activity report. An engineer is analyzing suspicious activity alerted by a threat intelligence platform that an authorized user in the HR department has accessed legal data daily for the last week. The engineer pulled the network data from the legal department’s shared folders and discovered above average-size data dumps. Which threat actor is implied from these artifacts?
Correct Answer & Rationale:
Answer: C
Explanation:
A “malicious insider” is someone within the organization who has authorized access but intentionally misuses that access to extract or exfiltrate data. In this case:
The HR user has legitimate access but deviates from their normal behavior pattern (accessing legal data daily instead of monthly).
The presence of large data dumps and the alert from a threat intelligence platform suggest intentional misuse rather than accidental behavior.
According to the Cisco CyberOps Associate guide, insider threats are identified by behavioral anomalies, especially involving sensitive data access patterns inconsistent with role-based access and historical usage profiles.
QUESTION DESCRIPTION:
Refer to the exhibit.
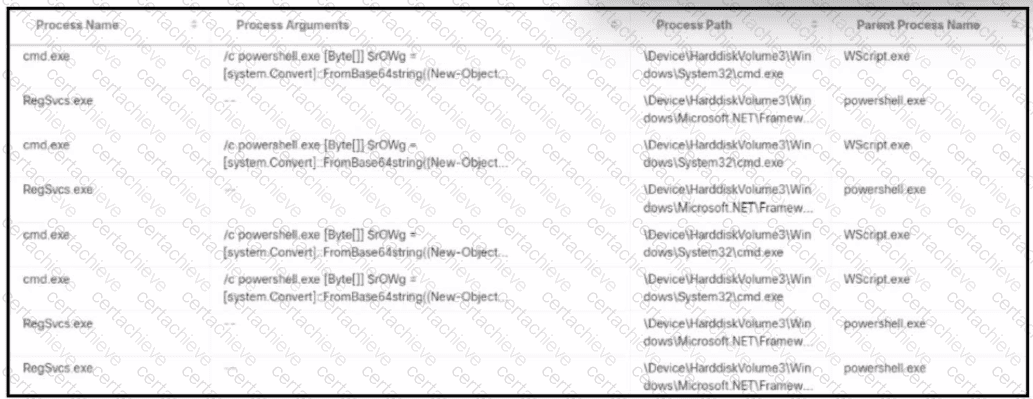
An alert came with a potentially suspicious activity from a machine in HR department. Which two IOCs should the security analyst flag? (Choose two.)
Correct Answer & Rationale:
Answer: D, E
Explanation:
The exhibit shows a series of process executions that form a suspicious chain involving scripting engines and obfuscated commands:
One critical indicator is cmd.exe executing PowerShell with obfuscated (Base64-encoded) arguments . The use of Base64 is a known method used by attackers to mask malicious commands. This aligns with attack techniques defined under MITRE ATT & CK T1059 (Command and Scripting Interpreter) and T1086 (PowerShell abuse). Therefore, option D is valid.
Another important IOC is WScript.exe acting as a parent of cmd.exe , which is abnormal in typical business environments. This indicates potential misuse of Windows Script Host (WSH) to launch commands, often seen in phishing or malware dropper scenarios. Thus, option E is also valid.
Options A and B by themselves are not definitive IOCs—PowerShell and cmd.exe are legitimate administrative tools and frequently used in Windows environments.
Option C is not supported by the exhibit—the reverse (powershell.exe initiated by WScript.exe) is what ' s seen, not the other way around.
These patterns align with the CyberOps Technologies (CBRFIR) 300-215 study guide, which specifies that chaining of interpreters (e.g., WScript → cmd → PowerShell) with encoded commands is a key indicator of compromise during forensic analysis.
QUESTION DESCRIPTION:
Which two tools conduct network traffic analysis in the absence of a graphical user interface? (Choose two.)
Correct Answer & Rationale:
Answer: B, C
Explanation:
TCPdump is a CLI-based packet capture tool that is widely used for real-time traffic inspection and analysis on Unix/Linux systems.
TCPshark is a variant CLI tool used similarly for packet analysis.
Although Wireshark is a powerful network protocol analyzer, it requires a GUI. Therefore, it is not suitable for environments without a graphical interface.
QUESTION DESCRIPTION:
Which technique is used to evade detection from security products by executing arbitrary code in the address space of a separate live operation?
Correct Answer & Rationale:
Answer: A
Explanation:
Process injection is a tactic where malicious code is inserted into the memory space of another process, enabling it to run with the privileges and context of a legitimate application. The Cisco study guide explains that this method allows malware to " hide in plain sight " within trusted processes and evade endpoint detection and response (EDR) tools.
It specifically notes: " Process injection techniques allow malware to execute within the memory space of a legitimate process, avoiding detection and taking advantage of the process ' s permissions. " .
QUESTION DESCRIPTION:
An investigator is analyzing an attack in which malicious files were loaded on the network and were undetected. Several of the images received during the attack include repetitive patterns. Which anti-forensic technique was used?
Correct Answer & Rationale:
Answer: D
Explanation:
The use of repetitive patterns in images is a known indicator of steganography, which is an anti-forensics technique used to hide malicious code or files inside seemingly benign content such as image or audio files. The repetitive patterns suggest that the image may contain embedded hidden data. This technique is particularly difficult to detect through conventional scanning or antivirus software.
According to the CyberOps Technologies (CBRFIR) 300-215 study guide, steganography is defined as “concealing malicious content or instructions within ordinary files such as .jpg, .png, or audio files, allowing the content to bypass security filters and reach the target system without detection”.
—
QUESTION DESCRIPTION:
What are two features of Cisco Secure Endpoint? (Choose two.)
Correct Answer & Rationale:
Answer: A, C
Explanation:
Cisco Secure Endpoint (formerly AMP for Endpoints) offers features like:
File trajectory: to track file behavior and spread across endpoints.
Orbital Advanced Search: for querying endpoint data to detect threats in real time.
QUESTION DESCRIPTION:
Which scripts will search a log file for the IP address of 192.168.100.100 and create an output file named parsed_host.log while printing results to the console?
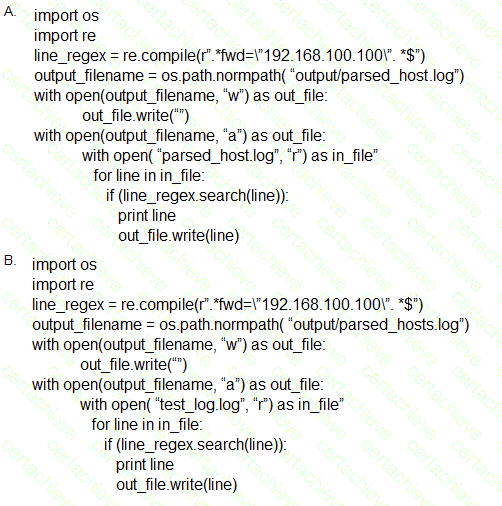
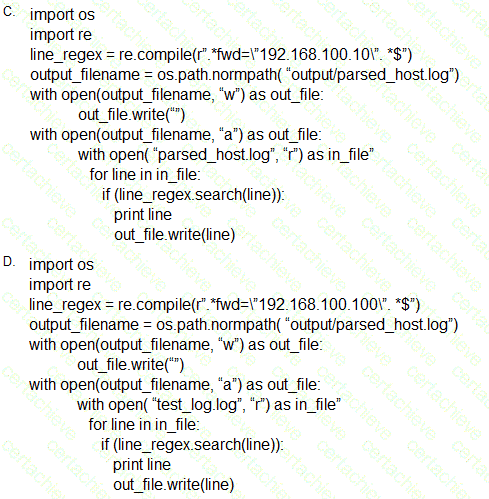
Correct Answer & Rationale:
Answer: B
Explanation:
To determine the correct script, we evaluate the following requirements:
The script must search for the IP address 192.168.100.100.
The output should be written to a file named parsed_host.log.
The matching lines should be printed to the console.
Analysis of the options:
Option A: Correct IP regex used and correct output filename, but reads from parsed_host.log instead of a source log file like test_log.log (not ideal for initial parsing).
Option C: The IP address used is 192.168.100.101 instead of 192.168.100.100 — incorrect.
Option D: Same IP address and logic as Option B, but uses print statement without parentheses, which is not valid in Python 3 unless using Python 2 — not ideal.
✅ Option B:
Uses correct IP: " 192.168.100.100 "
Reads from test_log.log (presumably the source log file).
Writes to output/parsed_host.log.
Prints each matching line and writes to output file — satisfying all conditions.
A Stepping Stone for Enhanced Career Opportunities
Your profile having CyberOps Professional certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Cisco 300-215 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Cisco Exam 300-215
Achieving success in the 300-215 Cisco exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in 300-215 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam 300-215!
In the backdrop of the above prep strategy for 300-215 Cisco exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding 300-215 exam prep. Here's an overview of Certachieve's toolkit:
Cisco 300-215 PDF Study Guide
This premium guide contains a number of Cisco 300-215 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Cisco 300-215 study guide pdf free download is also available to examine the contents and quality of the study material.
Cisco 300-215 Practice Exams
Practicing the exam 300-215 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Cisco 300-215 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Cisco 300-215 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning 300-215 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Cisco 300-215 CyberOps Professional FAQ
There are only a formal set of prerequisites to take the 300-215 Cisco exam. It depends of the Cisco organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Cisco 300-215 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Cisco 300-215 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Cisco 300-215 exam dumps to enhance your readiness for the exam.
Like any other Cisco Certification exam, the CyberOps Professional is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do 300-215 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The 300-215 Cisco exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Cisco 300-215 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Cisco has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Cisco changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



