The Fortinet NSE 7 - Enterprise Firewall 7.6 Administrator (FCSS_EFW_AD-7.6)
Passing Fortinet Fortinet Certified Professional Network Security exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard FCSS_EFW_AD-7.6 Dumps
In 2026, Fortinet uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official Fortinet FCSS_EFW_AD-7.6 Exam Domains
Our curriculum is meticulously mapped to the Fortinet official blueprint.
System Configuration & Security Fabric (25%)
Master the foundation of the enterprise network. Focus on implementing the Fortinet Security Fabric, configuring hardware acceleration (NP7/CP9), and managing complex High Availability (HA) clusters with virtual MAC addresses for VDOMs. Learn to design multi-tenant architectures using advanced VLAN and VDOM segmentation.
Security Profiles & Threat Prevention (20%)
Deep dive into the FortiGuard-powered inspection engine. Master SSL/SSH inspection (Deep vs. Certificate inspection) and its performance impact. Focus on fine-tuning IPS profile extensions to reduce false positives, and use the Internet Service Database (ISDB) to enforce layer 3/4 application policies at scale.
Advanced Routing (20%)
Master the service provider-grade routing required for the enterprise core. Focus on OSPF (LSA types, multi-area configuration) and BGP (path selection, confederations, and loopback sourcing). Learn to implement route maps and redistribution logic to ensure seamless traffic flow across hybrid environments.
VPN Architectures & SD-WAN (20%)
Focus on secure connectivity and branch orchestration. Master IPsec VPN IKE version 2 and the implementation of Auto-Discovery VPN (ADVPN) for on-demand spoke-to-spoke tunnels. Learn the latest 2026 standards for SD-WAN path selection and quality-of-service (QoS) for real-time applications.
Central Management & Monitoring (15%)
Master orchestration at scale. Focus on using FortiManager 7.6 for centralized policy deployment and FortiAnalyzer 7.6 for advanced threat hunting and compliance reporting. Learn to automate configuration tasks and verify Security Fabric health via centralized telemetry.
Fortinet FCSS_EFW_AD-7.6 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
During the maintenance window, an administrator must sniff all the traffic going through a specific firewall policy, which is handled by NP6 interfaces. The output of the sniffer trace provides just a few packets.
Why is the output of sniffer trace limited?
Correct Answer & Rationale:
Answer: B
Explanation:
FortiGate devices with NP6 (Network Processor 6) acceleration offload traffic directly to hardware, bypassing the CPU for improved performance. When auto-asic-offload is enabled in a firewall policy, most of the traffic does not reach the CPU, which means it won ' t be captured by the standard sniffer trace command.
Since NP6-accelerated traffic is handled entirely in hardware, only a small portion of initial packets (such as session setup packets or exceptions) might be seen in the sniffer output. To capture all packets, the administrator must disable hardware offloading using:
config firewall policy
edit < policy_ID >
set auto-asic-offload disable
end
Disabling ASIC offload forces traffic to be processed by the CPU, allowing the sniffer tool to capture all packets.
QUESTION DESCRIPTION:
Refer to the exhibit.
A FortiGate segmented into VDOMs is shown. You must ensure effective and accelerated internet access for all of the VDOMs in this enterprise network. How can you achieve this? (Choose one answer)
Correct Answer & Rationale:
Answer: C
Explanation:
Comprehensive and Detailed 150 to 200 words of Explanation From Exact Extract of Enterprise Firewall 7.6 Administrator documents:
According to the FortiOS 7.6 Administration Guide and the FortiGate Infrastructure study materials, inter-VDOM communication can be achieved using either software-based VDOM links or hardware-accelerated NPU VDOM links (vlinks).
While standard VDOM links (Option B) allow traffic to pass between VDOMs, they are processed by the system CPU, which can become a bottleneck in high-throughput environments. To ensure accelerated internet access as specified in the requirements, NPU vlinks (Option C) must be used. NPU vlinks are virtual interfaces created in pairs that allow traffic to be offloaded to the FortiGate’s Network Processor (NP6, NP7, etc.), significantly reducing latency and CPU overhead.
In the provided exhibit, the root VDOM has direct internet access, while VDOM1 and VDOMn do not. By configuring NPU vlinks between the non-root VDOMs and the root VDOM, you create a hardware-accelerated path. Traffic from the internal VDOMs is sent through the vlink to the root VDOM, which then forwards it to the Internet. This " hub-and-spoke " VDOM architecture, powered by NPU acceleration, ensures that all VDOMs share the internet connection without sacrificing performance.
QUESTION DESCRIPTION:
Refer to the exhibit.
A pre-run CLI template that is used in zero-touch provisioning (ZTP) and low-touch provisioning (LTP) with FortiManager is shown.
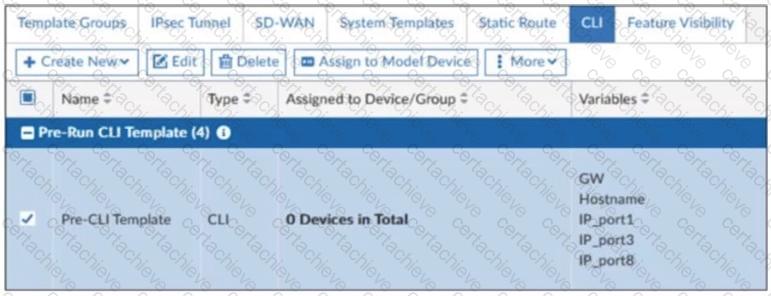
The template is not assigned even though the configuration has already been installed on FortiGate.
What is true about this scenario?
Correct Answer & Rationale:
Answer: B
Explanation:
In FortiManager, pre-run CLI templates are used in Zero-Touch Provisioning (ZTP) and Low-Touch Provisioning (LTP) to configure a FortiGate device before it is fully managed by FortiManager.
These templates apply configurations when a device is initially provisioned. Once the pre-run CLI template is executed, FortiManager automatically unassigns it from the device because it is not meant to persist like other policy configurations. This prevents conflicts and ensures that the FortiGate configuration is not repeatedly applied after the initial setup.
QUESTION DESCRIPTION:
An administrator is checking an enterprise network and sees a suspicious packet with the MAC address e0:23:ff:fc:00:86.
What two conclusions can the administrator draw? (Choose two.)
Correct Answer & Rationale:
Answer: A, D
Explanation:
According to the FortiOS 7.6 Infrastructure study guide and High Availability (HA) documentation, FortiGate units in an HA cluster use a virtual MAC address to ensure seamless failover. The structure of this virtual MAC address is strictly defined by the Fortinet HA protocol.
For a standard HA cluster, the virtual MAC address format is 00:09:0f:09: < group-id_hex > : < vcluster_port_hex > . However, when VDOMs are enabled, the virtual MAC address prefix changes to e0:23:ff to accommodate the additional complexity of multiple virtual domains. Therefore, the prefix e0:23:ff in the suspicious MAC address e0:23:ff:fc:00:86 confirms that the packet originated from a cluster with VDOMs enabled (Option A).
Regarding the interface identification, the last byte (86) is calculated as follows:
The 0x80 bit indicates virtual-cluster 2 (vcluster 2). Since $0x86 = 0x80 + 0x06$, we know the packet is from vcluster 2.
The remaining value 0x06 represents the interface index. In FortiOS, the index starts at 0 (port1 = 0, port2 = 1, port3 = 2, port4 = 3, port5 = 4, port6 = 5, port7 = 6). Therefore, the index 6 corresponds exactly to port 7 (Option D).
The fourth byte (fc) represents the HA Group ID (252 in decimal). While this is indeed lower than 255, the specific logic of the virtual MAC composition in a VDOM-enabled environment points specifically to the port identification and vcluster status as the primary diagnostic conclusions.
QUESTION DESCRIPTION:
Refer to the exhibit, which shows a command output.
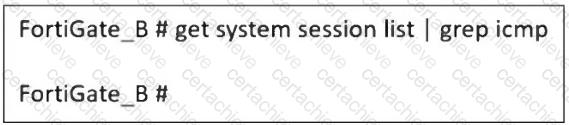
FortiGate_A and FortiGate_B are members of an FGSP cluster in an enterprise network.
While testing the cluster using the ping command, the administrator monitors packet loss and found that the session output on FortiGate_B is as shown in the exhibit.
What could be the cause of this output on FortiGate_B?
Correct Answer & Rationale:
Answer: B
Explanation:
The Fortinet FGSP (FortiGate Session Life Support Protocol) cluster allows session synchronization between two FortiGate devices to provide seamless failover. However, ICMP (ping) is a connectionless protocol, and by default, FortiGate does not synchronize connectionless sessions unless explicitly enabled.
In the exhibit:
● The command get system session list | grep icmp on FortiGate_B returns no output, meaning that ICMP sessions are not being synchronized from FortiGate_A.
● If session-pickup-connectionless is disabled, FortiGate_B will not receive ICMP sessions, causing packet loss during failover.
QUESTION DESCRIPTION:
A company ' s users on an IPsec VPN between FortiGate A and B have experienced intermittent issues since implementing VXLAN. The administrator suspects that packets exceeding the 1500-byte default MTU are causing the problems.
In which situation would adjusting the interface’s maximum MTU value help resolve issues caused by protocols that add extra headers to IP packets?
Correct Answer & Rationale:
Answer: C
Explanation:
When using IPsec VPNs and VXLAN, additional headers are added to packets, which can exceed the default 1500-byte MTU. This can lead to fragmentation issues, dropped packets, or degraded performance.
To resolve this, the MTU (Maximum Transmission Unit) should be adjusted only if all devices in the network path support it. Otherwise, some devices may still drop or fragment packets, leading to continued issues.
Why adjusting MTU helps:
● VXLAN adds a 50-byte overhead to packets.
● IPsec adds additional encapsulation (ESP, GRE, etc.), increasing the packet size.
● If packets exceed the MTU, they may be fragmented or dropped, causing intermittent connectivity issues.
● Lowering the MTU on interfaces ensures packets stay within the supported size limit across all network devices.
QUESTION DESCRIPTION:
Refer to the exhibit.
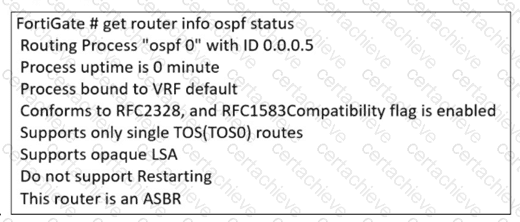
The partial output of an OSPF command is shown. You are checking the OSPF status of a FortiGate device when you receive the output shown in the exhibit. Based on the output, which two statements about FortiGate are correct? (Choose two answers)
Correct Answer & Rationale:
Answer: B, D
Explanation:
Comprehensive and Detailed 150 to 200 words of Explanation From Exact Extract of Enterprise Firewall 7.6 Administrator documents:
Based on the FortiOS 7.6 Infrastructure study guide and official documentation regarding OSPF monitoring, the command output get router info ospf status provides critical details about the OSPF process.
Injecting External Information (Option D): The last line of the exhibit explicitly states, " This router is an ASBR " (Autonomous System Boundary Router). By definition in the OSPF protocol, an ASBR is a router that connects the OSPF network to another routing domain (such as BGP, Static, or Connected routes) and is responsible for injecting external routing information into the OSPF domain.
OSPF ECMP Support (Option B): The output indicates that the OSPF process " Conforms to RFC2328 " . RFC 2328 is the standard for OSPFv2, which includes the capability for Equal-Cost Multi-Path (ECMP). In FortiOS, the OSPF engine supports multi-path routing by default, allowing the device to utilize multiple paths to the same destination if they share the same cost.
Option A is incorrect because the output does not indicate the router ' s DR/BDR election status on a specific segment. Option C is incorrect because " ID 0.0.0.5 " refers to the Router ID, not the OSPF Area ID.
QUESTION DESCRIPTION:
Refer to the exhibit, which shows an OSPF network.
Which configuration must the administrator apply to optimize the OSPF database?
Correct Answer & Rationale:
Answer: B
Explanation:
The OSPF database optimization is necessary to reduce unnecessary routing information and improve network performance. In the given topology, Area 0.0.0.1 is a non-backbone area connected to Area 0.0.0.0 (the backbone area) through an Area Border Router (ABR).
To optimize OSPF in this scenario, configuring Area 0.0.0.1 as a Stub Area will:
● Reduce the size of the OSPF database by preventing external routes (from outside OSPF) from being injected into Area 0.0.0.1.
● Allow only intra-area and inter-area routes, meaning routers in Area 0.0.0.1 will rely on a default route for external destinations.
● Improve convergence time and reduce router processing load since fewer LSAs (Link-State Advertisements) are exchanged.
QUESTION DESCRIPTION:
An administrator is designing an ADVPN network for a large enterprise with spokes that have varying numbers of internet links. They want to avoid a high number of routes and peer connections at the hub.
Which method should be used to simplify routing and peer management?
Correct Answer & Rationale:
Answer: C
Explanation:
When designing an ADVPN (Auto-Discovery VPN) network for a large enterprise with spokes that have varying numbers of internet links, the main challenge is to minimize the number of peer connections and routes at the hub while maintaining scalability and efficiency.
Using a dynamic routing protocol (such as BGP or OSPF) with loopback interfaces helps in several ways:
● Reduces the number of peer connections at the hub by using a single loopback address per spoke instead of individual physical interfaces.
● Enables simplified route advertisement by dynamically learning and propagating routes instead of manually configuring static routes.
● Supports multiple internet links per spoke efficiently, as dynamic routing can automatically adjust to the best available path.
● Allows seamless failover if a spoke’s internet link fails, ensuring continuous connectivity.
QUESTION DESCRIPTION:
Refer to the exhibit.
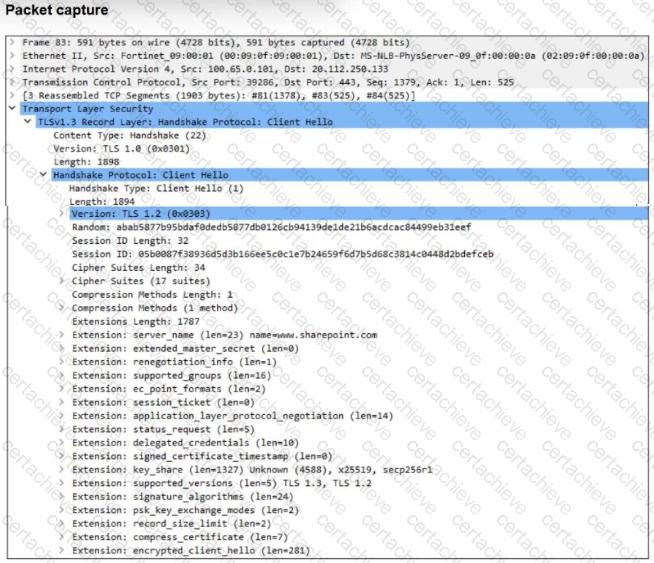
The packet capture output of a client hello message is shown.
You are updating a firewall policy that includes SSL certificate inspection. You are capturing packets from the traffic passing through this firewall policy.
Which two statements about the packet capture are correct? (Choose two.)
Correct Answer & Rationale:
Answer: B, D
Explanation:
Based on the packet capture provided in the exhibit and Fortinet ' s Enterprise Firewall 7.6 inspection standards:
Web Filtering Effectiveness (B): The exhibit shows the Server Name Indication (SNI) extension within the Client Hello, specifically indicating the hostname www.fortinet.com. When a firewall policy is configured for SSL Certificate Inspection , the FortiGate does not decrypt the payload but instead relies on the SNI or the certificate ' s Subject/SAN fields to identify the website. Therefore, a web filtering profile can effectively categorize and block/allow this traffic based on the domain name found in the SNI.
TLS Version Support (D): The supported_versions extension is a feature introduced with TLS 1.3 to negotiate the version of the handshake. In the exhibit, the extension explicitly lists two versions: TLS 1.3 (0x0304) and TLS 1.2 (0x0303) . This tells the FortiGate exactly which protocols the client is capable of using for this session.
Why A is incorrect: Antivirus profiles require Deep SSL Inspection (full decryption) to scan the actual files and payload of the session. Since the policy is using Certificate Inspection , the FortiGate cannot see the cleartext data, rendering the antivirus profile ineffective for this encrypted traffic.
Why C is incorrect: While the Subject Alternative Name (SAN) is a common way to identify a site, it is found in the server ' s certificate. In this specific capture, the SNI (Server Name Indication) is already present in the Client Hello, which allows the FortiGate to apply security profiles even before the server ' s certificate is seen.
A Stepping Stone for Enhanced Career Opportunities
Your profile having Fortinet Certified Professional Network Security certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Fortinet FCSS_EFW_AD-7.6 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Fortinet Exam FCSS_EFW_AD-7.6
Achieving success in the FCSS_EFW_AD-7.6 Fortinet exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in FCSS_EFW_AD-7.6 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam FCSS_EFW_AD-7.6!
In the backdrop of the above prep strategy for FCSS_EFW_AD-7.6 Fortinet exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding FCSS_EFW_AD-7.6 exam prep. Here's an overview of Certachieve's toolkit:
Fortinet FCSS_EFW_AD-7.6 PDF Study Guide
This premium guide contains a number of Fortinet FCSS_EFW_AD-7.6 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Fortinet FCSS_EFW_AD-7.6 study guide pdf free download is also available to examine the contents and quality of the study material.
Fortinet FCSS_EFW_AD-7.6 Practice Exams
Practicing the exam FCSS_EFW_AD-7.6 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Fortinet FCSS_EFW_AD-7.6 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Fortinet FCSS_EFW_AD-7.6 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning FCSS_EFW_AD-7.6 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Fortinet FCSS_EFW_AD-7.6 Fortinet Certified Professional Network Security FAQ
There are only a formal set of prerequisites to take the FCSS_EFW_AD-7.6 Fortinet exam. It depends of the Fortinet organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Fortinet FCSS_EFW_AD-7.6 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Fortinet FCSS_EFW_AD-7.6 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Fortinet FCSS_EFW_AD-7.6 exam dumps to enhance your readiness for the exam.
Like any other Fortinet Certification exam, the Fortinet Certified Professional Network Security is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do FCSS_EFW_AD-7.6 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The FCSS_EFW_AD-7.6 Fortinet exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Fortinet FCSS_EFW_AD-7.6 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Fortinet has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Fortinet changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



