The Performing CyberOps Using Core Security Technologies (CBRCOR) (350-201)
Passing Cisco CyberOps Professional exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard 350-201 Dumps
In 2026, Cisco uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official Cisco 350-201 Exam Domains
Our curriculum is meticulously mapped to the Cisco official blueprint.
Fundamentals (20%)
Master the foundational concepts of cybersecurity operations, including the kill chain, threat intelligence sharing, and the application of security models to enterprise environments.
Techniques (30%)
Deep dive into endpoint and network security monitoring, data normalization, and utilizing analysis tools to identify sophisticated attack patterns.
Processes (20%)
Mastering the incident response lifecycle, risk management frameworks, and the critical phases of digital forensics and evidence handling.
Automation and Orchestration (20%)
Expertly build SOAR workflows, utilize REST APIs for security orchestration, and interpret script outputs to automate SOC tasks.
Data Management (10%)
Understanding telemetry types, efficient log storage, and data retention policies essential for maintaining a high-performance Security Operations Center (SOC).
Cisco 350-201 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
A SOC team receives multiple alerts by a rule that detects requests to malicious URLs and informs the incident response team to block the malicious URLs requested on the firewall. Which action will improve the effectiveness of the process?
Correct Answer & Rationale:
Answer: D
Explanation:
Creating an automation script for blocking URLs on the firewall when the rule is triggered will improve the effectiveness of the process by reducing the time between the detection of a request to a malicious URL and the blocking action. This proactive approach ensures that the URLs are blocked immediately, minimizing the window of opportunity for the threat to cause harm
QUESTION DESCRIPTION:
An engineer is going through vulnerability triage with company management because of a recent malware outbreak from which 21 affected assets need to be patched or remediated. Management decides not to prioritize fixing the assets and accepts the vulnerabilities. What is the next step the engineer should take?
Correct Answer & Rationale:
Answer: B
Explanation:
If management decides not to prioritize fixing the vulnerabilities and accepts them, the next step for the engineer is to acknowledge the vulnerabilities and document the risk. This involves recording the decision and the rationale behind it, assessing the potential impact, and ensuring that there is a clear understanding of the risks being accepted. This documentation is crucial for future reference and accountability, and it may also include recommendations for mitigating the risk where possible
QUESTION DESCRIPTION:
Refer to the exhibit.
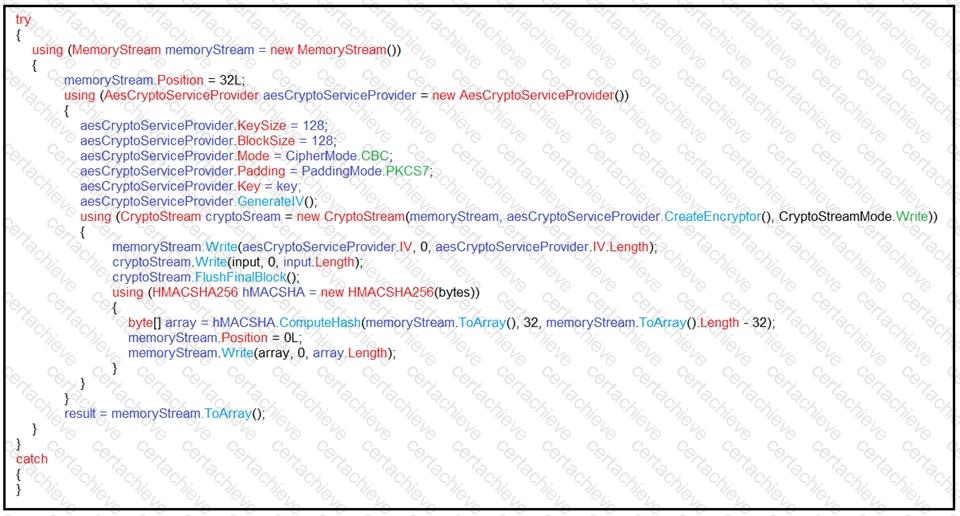
An engineer is performing a static analysis on a malware and knows that it is capturing keys and webcam events on a company server. What is the indicator of compromise?
Correct Answer & Rationale:
Answer: D
Explanation:
The indicator of compromise (IoC) for the malware in question is that it has routines for encryption and decryption, which are used to conceal URLs/IP addresses. Additionally, it is capturing keystrokes and webcam events, and storing this data in encrypted files locally on the company server. This behavior is indicative of malware that is designed to stealthily collect and exfiltrate sensitive information without being easily detected. The use of encryption helps to hide the data and the destination to which it may be sent, making it more challenging for security systems to identify and block the malicious activity.
QUESTION DESCRIPTION:
A SOC analyst is notified by the network monitoring tool that there are unusual types of internal traffic on IP subnet 103.861.2117.0/24. The analyst discovers unexplained encrypted data files on a computer system that belongs on that specific subnet. What is the cause of the issue?
Correct Answer & Rationale:
Answer: D
Explanation:
The presence of unusual internal traffic and unexplained encrypted data files suggests a malware outbreak. Malware can cause abnormal network traffic patterns and encrypt files on infected systems, often leading to ransomware attacks or data exfiltration efforts
QUESTION DESCRIPTION:
Employees receive an email from an executive within the organization that summarizes a recent security breach and requests that employees verify their credentials through a provided link. Several employees report the email as suspicious, and a security analyst is investigating the reports. Which two steps should the analyst take to begin this investigation? (Choose two.)
Correct Answer & Rationale:
Answer: B, E
Explanation:
In the case of a suspicious email, the security analyst should communicate with employees to determine who opened the link and isolate the affected assets to prevent further spread of potential malware. Additionally, checking the email header to identify the sender and analyzing the link in an isolated environment are crucial steps to begin the investigation and understand the scope and impact of the potential breach 1 3 .
QUESTION DESCRIPTION:
An organization had several cyberattacks over the last 6 months and has tasked an engineer with looking for patterns or trends that will help the organization anticipate future attacks and mitigate them. Which data analytic technique should the engineer use to accomplish this task?
Correct Answer & Rationale:
Answer: C
Explanation:
Predictive analytics is the most suitable data analytic technique for anticipating future cyberattacks. It involves using historical data, statistical algorithms, and machine learning techniques to identify the likelihood of future outcomes based on patterns and trends. This approach can help organizations forecast potential cyber threats and take proactive measures to mitigate them before they occur 1 2 3 .
QUESTION DESCRIPTION:
A company launched an e-commerce website with multiple points of sale through internal and external e- stores. Customers access the stores from the public website, and employees access the stores from the intranet with an SSO. Which action is needed to comply with PCI standards for hardening the systems?
Correct Answer & Rationale:
Answer: B
Explanation:
To comply with PCI standards for hardening systems, especially for an e-commerce website with multiple points of sale, it is essential to encrypt personal data. This includes any information that can be used to identify an individual, such as names, addresses, and credit card numbers. Encryption helps protect this data during transmission and storage, reducing the risk of unauthorized access and data breaches 2 .
QUESTION DESCRIPTION:
Refer to the exhibit.
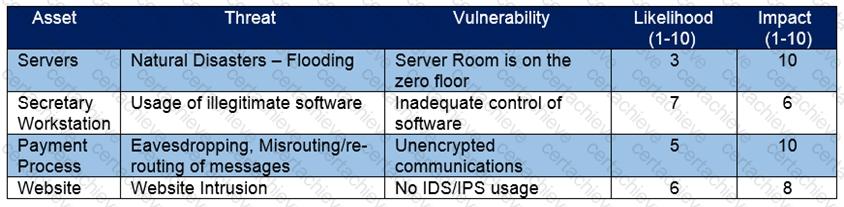
Which asset has the highest risk value?
Correct Answer & Rationale:
Answer: C
Explanation:
The risk value for an asset is typically calculated by multiplying the likelihood of a threat occurring by the impact that the threat would have if it did occur. In the exhibit provided, the ‘payment process’ has a likelihood of 5 and an impact of 10, which when multiplied together gives a risk value of 50. This is the highest risk value when compared to the other assets listed, making the payment process the asset with the highest risk value.
References :
Cisco’s CyberOps Using Core Security Technologies documentation emphasizes understanding and managing risks to an organization’s information assets. This includes identifying vulnerabilities and threats, assessing their potential impact, and calculating risk values to prioritize response actions 1 .
The Cisco Certified CyberOps Associate Overview outlines knowledge areas such as security concepts and intrusion analysis, relevant to investigating and responding to security incidents
QUESTION DESCRIPTION:
What is the impact of hardening machine images for deployment?
Correct Answer & Rationale:
Answer: A
Explanation:
Hardening machine images for deployment reduces the attack surface by eliminating unnecessary services, closing open network ports, removing unused software, and applying security configurations. This process minimizes the number of potential vulnerabilities that can be exploited by attackers 3 .
QUESTION DESCRIPTION:
An analyst received multiple alerts on the SIEM console of users that are navigating to malicious URLs. The analyst needs to automate the task of receiving alerts and processing the data for further investigations. Three variables are available from the SIEM console to include in an automation script: console_ip, api_token, and reference_set_name. What must be added to this script to receive a successful HTTP response?
#!/usr/bin/python import sys import requests
Correct Answer & Rationale:
Answer: C
Explanation:
To automate the task of receiving alerts and processing data for further investigations, the script must include the variables that allow it to communicate with the SIEM console. These would typically be the console’s IP address ( console_ip ) and an authentication token ( api_token ) to establish a secure connection and access the necessary data 2 .
A Stepping Stone for Enhanced Career Opportunities
Your profile having CyberOps Professional certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Cisco 350-201 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Cisco Exam 350-201
Achieving success in the 350-201 Cisco exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in 350-201 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam 350-201!
In the backdrop of the above prep strategy for 350-201 Cisco exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding 350-201 exam prep. Here's an overview of Certachieve's toolkit:
Cisco 350-201 PDF Study Guide
This premium guide contains a number of Cisco 350-201 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Cisco 350-201 study guide pdf free download is also available to examine the contents and quality of the study material.
Cisco 350-201 Practice Exams
Practicing the exam 350-201 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Cisco 350-201 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Cisco 350-201 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning 350-201 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Cisco 350-201 CyberOps Professional FAQ
There are only a formal set of prerequisites to take the 350-201 Cisco exam. It depends of the Cisco organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Cisco 350-201 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Cisco 350-201 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Cisco 350-201 exam dumps to enhance your readiness for the exam.
Like any other Cisco Certification exam, the CyberOps Professional is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do 350-201 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The 350-201 Cisco exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Cisco 350-201 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Cisco has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Cisco changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



