The Fortinet NSE 6 - LAN Edge 7.6 Architect (FCSS_LED_AR-7.6)
Passing Fortinet Fortinet Certified Solution Specialist exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard FCSS_LED_AR-7.6 Dumps
In 2026, Fortinet uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official Fortinet FCSS_LED_AR-7.6 Exam Domains
Our curriculum is meticulously mapped to the Fortinet official blueprint.
Authentication & Identity Management (20%)
Master advanced identity orchestration at the edge. Focus on RADIUS/LDAP integration for enterprise-grade access, deploying FortiAuthenticator for certificate-based security, and configuring 802.1X for machine-level authentication. Learn to manage user-to-device mapping to ensure granular visibility before a packet even hits the core.
Central Management & Provisioning (30%)
The "Automation Engine." Master the architecture of the Security Fabric as it extends to the LAN. Focus on managing FortiSwitch and FortiAP via FortiManager using the FortiLink protocol. Learn to implement Zero-Touch Provisioning (ZTP), manage switch templates, and orchestrate firmware lifecycles across distributed branch locations.
Zero-Trust LAN Access & NAC (30%)
The "Security Core" of the 7.6 exam. Master FortiLink NAC for dynamic asset tagging and VLAN pooling. Focus on MAC Authentication Bypass (MAB) for IoT devices, implementing guest portals with restricted access, and enforcing Zero-Trust Network Access (ZTNA) tags to ensure that LAN users only access authorized micro-segmented resources.
Monitoring & AIOps-Driven Troubleshooting (20%)
Master "Day 2" intelligence. Focus on using FortiAIOps to identify client roaming issues, throughput bottlenecks, and hardware failures before they impact the user. Learn to troubleshoot FortiLink synchronization errors, resolve PoE budget contention, and implement automated quarantine workflows for compromised edge devices.
Fortinet FCSS_LED_AR-7.6 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
In addition to requiring a FortiAnalyzer device to configure the Security Fabric, which license must be added to FortiAnalyzer to use Indicators of Compromise (IOC) rules?
Correct Answer & Rationale:
Answer: D
Explanation:
FortiAnalyzer requires a specific license to evaluateIndicators of Compromise (IOC).
From theFortiAnalyzer 7.4.1 Administration Guide:
IOC identification requires theThreat Detection Servicelicense on FortiAnalyzer.
This license enables:
IOC database updates
Compromised host detection
Event correlation based on FortiGuard threat intelligence
Fabric-wide IOC automation triggers
Why the other answers are incorrect:
A: IoT Security add-on is unrelated to IOC rules.
B: There isnoIOC subscription license type for FortiAnalyzer.
C: FAZ-Basic license doesNOTinclude IOC detection.
QUESTION DESCRIPTION:
Why is it critical to maintain NTP synchronization between FortiGate and FortiSwitch when FortiLink is configured?
Correct Answer & Rationale:
Answer: C
Explanation:
FortiGate and FortiSwitchmust share synchronized timewhen operating in FortiLink mode.
Documented reasons in FortiOS:
Accurate time synchronization is required for logs, authentication events, and fabric correlations.
Why it’s critical:
802.1X EAP and RADIUS timestamp validation
NAC policy enforcement timestamps
Certificate validation
Log correlation in Security Fabric / FortiAnalyzer
Incorrect options:
A: Firmware synchronization does NOT require NTP.
B: Switch-to-switch communication does not depend on NTP.
D: Standalone mode is unrelated to time sync.
QUESTION DESCRIPTION:
How can FortiAIOps help optimize network performance in an SD-Branch deployment with FortiGate, FortiSwitch, and FortiAP?
Correct Answer & Rationale:
Answer: B
Explanation:
In an SD-Branch deployment (FortiGate + FortiSwitch + FortiAP),FortiAIOps:
Collects telemetry and logs from Fabric devices
Usesmachine-learning / AI analyticsto:
Spot anomalies (latency, packet loss, RF issues, misconfigurations)
Highlight root causes
Proposeoptimization recommendations(e.g., channel changes, power tuning, config fixes)
It doesnot:
Automatically disable devices (Afalse)
Replace SD-WAN config or all routing (Cfalse)
Fixallissues with zero human input (Dis marketing fantasy, not reality)
QUESTION DESCRIPTION:
Which statement about generating a certificate signing request (CSR) for a CER certificate is true?
Correct Answer & Rationale:
Answer: A
Explanation:
The FortiOS documentation explicitly states that a CSR used for certificate signing must contain accurate and valid fields, especially:
Common Name (CN)
Organization (O)
Country (C)
Public key parameters
According to the FortiGate certificate section:
Incorrect CSR field information can cause the CA to reject the request.
Reasons include:
The CA validates identity and organizational information.
Missing or malformed data invalidates PKI requirements.
The CSR is not corrected automatically by the CA.
Therefore:
✔A is correct.
Options B–D contradict PKI principles:
B is false: CAs do not issue certificates with mismatched identity fields for public trust.
C is false: CSR fields are not only for internal use; they define certificate identity.
D is false: CAs do not auto-correct CSR fields.
QUESTION DESCRIPTION:
Refer to the exhibit.
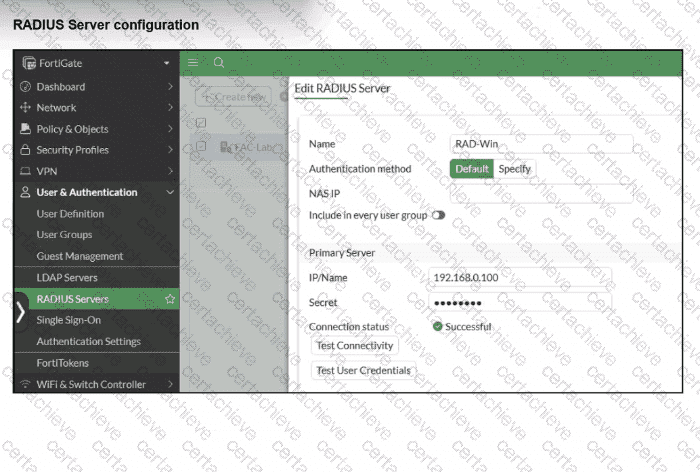
On FortiGate, a RADIUS server is configured to forward authentication requests to FortiAuthenticator, which acts as a RADIUS proxy. FortiAuthenticator then relays these authentication requests to a remote Windows AD server using LDAP.
While testing authentication using the CLI command diagnose test authserver. the administrator observed that authentication succeeded with PAP but failed when using MS-CHAFV2.
Which two solutions can the administrator implement to enable MS-CHAPv2 authentication? (Choose two.)
Correct Answer & Rationale:
Answer: A, B
Explanation:
The correct answers are A and B.
The LAN Edge 7.6 Architect study guide explains that when LDAP is the back-end server, CHAP, MS-CHAP, and MS-CHAPv2 do not work because the client sends a one-way password hash, while LDAP expects the actual password:
“If FortiGate is configured to authenticate clients using a remote LDAP server, VPN and wireless clients using CHAP schemes are not able to authenticate... The reason is that during CHAP, MS-CHAP, and MS-CHAPv2 authentication, a client sends a one-way hash of the password. However, the LDAP server, which is on the back end, is expecting the password itself.”
The same study guide then gives the two valid solutions:
“Two possible methods that you can use to solve the CHAP and LDAP problem are:”
“Use RADIUS: Change your back-end server from LDAP to RADIUS.”
and
“If you are using Windows AD as your LDAP server, an alternative is to use FortiAuthenticator as an authentication proxy... You must also configure FortiAuthenticator to log in to the Windows domain using the credentials of a Windows administrator. This adds FortiAuthenticator as a trusted device on the Windows AD domain, allowing FortiAuthenticator to proxy the password hash from the client to the Windows server, using NTLM.”
That directly matches:
A. Enable Windows Active Directory domain authentication on FortiAuthenticator.
B. Configure FortiAuthenticator to use RADIUS instead of LDAP as the back-end authentication server.
The study guide also states this explicitly in the FortiAuthenticator LDAP configuration section:
“If you want FortiAuthenticator to relay CHAP, MS-CHAP, and MS-CHAPv2 authentication to a Windows AD server, you must enable Windows Active Directory Domain Authentication and enter the credentials for a Windows administrator.”
And it separately confirms RADIUS as another supported back-end proxy model:
“You can configure FortiAuthenticator to connect to existing RADIUS servers... If the local user database is not used, FortiAuthenticator proxies RADIUS authentication requests.”
Why the other options are incorrect:
C. Incorrect. RADIUS attribute filtering does not solve the CHAP/MS-CHAPv2 versus LDAP hash problem. The issue is the back-end authentication method, not attribute filtering.
D. Incorrect. Changing from MS-CHAPv2 to CHAP does not fix it, because the study guide says the same limitation applies to CHAP, MS-CHAP, and MS-CHAPv2 when LDAP is the back end
Final verified conclusion:
To enable MS-CHAPv2 authentication in this scenario, the two valid solutions are:
A. Enable Windows Active Directory domain authentication on FortiAuthenticator.
B. Configure FortiAuthenticator to use RADIUS instead of LDAP as the back-end authentication server.
QUESTION DESCRIPTION:
Refer to the exhibits.
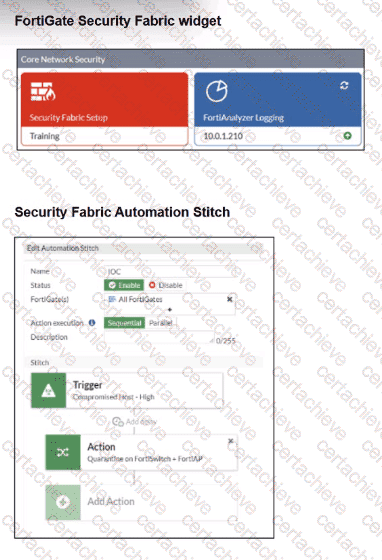
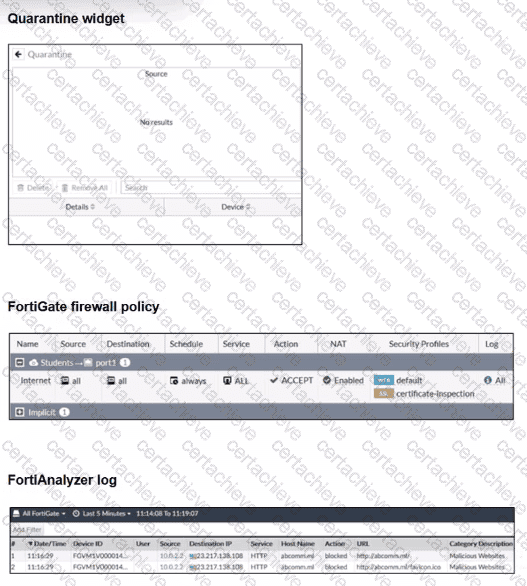
Examine the FortiGate configuration, FortiAnalyzer logs, and FortiGate widget shown in the exhibits.
Security Fabhc quarantine automation has been configured to isolate compromised devices automatically. FortiAnalyzer has been added to the Security Fabric, and an automation stitch has been configured to quarantine compromised devices.
To test the setup, a device with the IP address 10.0.2.1 that is connected through a managed FortiSwitch attempts to access a malicious website. The logs on FortiAnalyzer confirm that the event was recorded, but the device does not appear in the FortiGate quarantine widget.
Which two reasons could explain why FortiGate is not quarantining the device? (Choose two.)
Correct Answer & Rationale:
Answer: C, D
Explanation:
In this scenario:
FortiGate + FortiAnalyzer are part of theSecurity Fabric
AnAutomation Stitchis configured:
Trigger:Compromised Host – High(IOC from FortiAnalyzer)
Action:Quarantine on FortiSwitch + FortiAP
A test device10.0.2.1visits a malicious website.
FortiAnalyzer logs show the event, butFortiGate does NOT quarantine the device.
This means theautomation did not receive an IOC trigger, OR theFabric did not classify it as a compromise.
Let ' s evaluate each answer option.
✅C. The malicious website is not recognized as an indicator of compromise (IOC) by FortiAnalyzer.
✔Correct.
For FortiGate to quarantine a device:
FortiAnalyzer must classify the event as aCompromised Host → High / Medium / Critical
FortiAnalyzer must generate anIOC event
FortiGate must receive that IOC through the Fabric
Even though the FAZ log shows:
Action = blocked
Category = Malicious Websites
→ That doesNOTautomatically mean an IOC was generated.
A blocked website event isnot always an IOCunless:
It is included in theIOC database
FAZ’sAnalytics / UTM / IOCengine marks it as a compromise
Thus, if FAZ only logs a “Malicious Website” event butdoes not classify it as an IOC,
QUESTION DESCRIPTION:
When troubleshooting a captive portal issue, which POST parameter in the redirected HTTPS request can be used to track the user ' s session and ensure that the request is valid?
Correct Answer & Rationale:
Answer: C
Explanation:
In FortiGate captive portal workflows (local or external):
Client connects to SSID / interface that has captive portal enabled.
Client makes an HTTP/HTTPS request.
FortiGate intercepts and redirects to alogin page(local or external URL).
The portal form is submitted viaPOSTback to FortiGate.
To prevent tampering and to tie the POST back to thecorrect user session, FortiGate includes a special hidden parameter in the redirect and expects it in the POST:
The parameter is namedmagic.
The magic value:
Is aunique tokengenerated per captive-portal session.
Encodes/session-links the user’s IP, interface, and session info.
Allows FortiGate to ensure that:
The POST comes from the user who initiated the original request.
The request is not a random or replayed submission.
When troubleshooting:
If the external portal does notpreserve and resendthe magic parameter back to FortiGate exactly as received, authentication fails, and you’ll see errors like “session not found” or “invalid magic”.
Why the other fields are not used for this purpose
A. username– Just the login ID; multiple users can use the same username from different locations, so it can’t uniquely track the browser session.
B. redir– Contains the URL the user originally requested, so they can be sent back there after login. It is not a session integrity token.
D. email– Optional field used in some guest/registration flows; irrelevant to session validation.
QUESTION DESCRIPTION:
A conference center wireless network provides guest access through a captive portal, allowing unregistered users to self-register and connect to the network. The IT team has been tasked with updating the existing configuration to enforce captive portal authentication over a secure HTTPS connection. Which two steps should the administrator take to implement this change? (Choose two.)
Correct Answer & Rationale:
Answer: A, D
Explanation:
Goal: enforce captive portal authentication overHTTPSfor guests.
On FortiGate/FortiAuthenticator captive portal setups:
HTTP redirectis used so that when a guest browses to any HTTP site, their request is redirected to theportal URL.
Theportal URLitself must beHTTPSif you want a secure login page.
FortiOS captive portal and firewall authentication guidelines recommend:
EnablingHTTP redirectso unauthenticated HTTP traffic is transparently sent to the portal.
Configuring theportal URL with HTTPS, often referencing a certificate on FortiGate or FortiAuthenticator.
Therefore:
A. Enable HTTP redirect in the user authentication settings.✔This ensures unauthenticated HTTP requests are redirected to the (now HTTPS) portal.
D. Update the captive portal URL to use HTTPS on FortiGate and FortiAuthenticator.✔This makes the login itself secure (TLS-protected).
Incorrect:
B– You don’t need a new SSID; the same SSID can use HTTPS portal.
C– Disabling HTTP admin access on the SSID doesn’t control the captive portal scheme; HTTPS enforcement is done by the portal configuration and redirect, not by admin-access flags.
QUESTION DESCRIPTION:
Why is the suppression of rogue APs becoming more difficult with the introduction of new wireless security standards, such as 802.11w?
Correct Answer & Rationale:
Answer: D
Explanation:
The correct answer is D.
The LAN Edge 7.6 Architect study guide states: “Note that suppression of rogue APs is becoming increasingly more difficult, because new wireless security standards are beginning to mandate management frame protection (802.11w). This requires that clients authenticate management frames as being legitimate, preventing spoofing attacks. Because rogue suppression is a form of spoofing attack, an AP that the client is not connected to is trying to send deauthentication frames and, as a result, 802.11w prevents the client from taking notice of the dedicated monitoring AP.”
This exactly matches option D. Rogue AP suppression relies on spoofed deauthentication behavior, and 802.11w protects management frames, making that suppression method less effective.
Why the other options are incorrect:
A. Incorrect. The study guide does not say 802.11w makes suppression harder because of processing overhead. It specifically points to management frame protection and spoofing prevention
B. Incorrect. The study guide does not mention reduced wireless range as the reason.
C. Incorrect. The issue is not data traffic encryption. The study guide specifically refers to authentication of management frames, not general traffic encryption
QUESTION DESCRIPTION:
Refer to the exhibits.
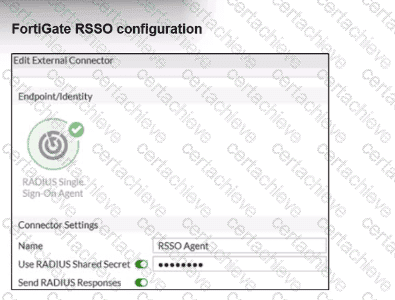
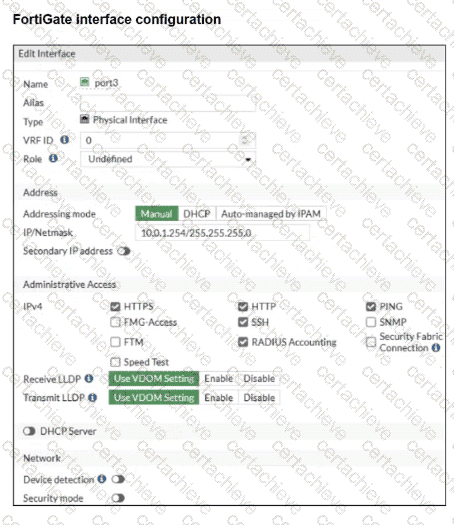
Examine the FortiGate RSSO configuration shown in the exhibit.
FortiGate is set up to use RSSO for user authentication. It is currently receiving RADIUS accounting messages through port3. The incoming RADIUS accounting messages contain the username in the User-Name attribute and group membership in the Class attribute. You must ensure that the users are authenticated through these RADIUS accounting messages and accurately mapped to their respective RSSO user groups.
Which three critical configurations must you implement on the FortiGate device? (Choose three.)
Correct Answer & Rationale:
Answer: A, D, E
Explanation:
The problem states:
FortiGate receivesRADIUS accounting messagesonport3.
User-Nameattribute contains the username.
Classattribute contains the group membership.
Goal: authenticate users through RSSO and map them to the correct user groups.
To achieve this, three critical components must be configured:
✔A. RADIUS Attribute Value in the RSSO group must match the Class attribute
This is mandatory because:
RSSO user groups on FortiGate match users based onthe value inside the RADIUS attribute(usually Class).
For group assignment to work, FortiGate must compare:
RSSO User Group → RADIUS Class Attribute Value
This isexactly how FortiGate maps RSSO users to groups.
✔D. RSSO agent’s sso-attribute must be set to Class
Thesso-attributedefineswhich RADIUS attribute contains the group information.
Because group membership is carried in:
➡Class attribute
You must configure:
config user radius
set sso-attribute Class
end
This tells FortiGate:
" Use the Class attribute to derive user group membership. "
✔E. rsso-endpoint-attribute must be set to User-Name
This identifieswhich RADIUS attributecarries the actualusername.
In this scenario:
RADIUS accounting messages contain the username inUser-Name.
So the correct setting is:
config user radius
set rsso-endpoint-attribute User-Name
end
This ensures the RSSO user object uses the correct username.
❌Incorrect Options Explained
B. Assign RSSO user groups to all firewall policies
Not required.
You only assign them to policies where RSSO authentication is used.
C. Device detection and Security Fabric Connection should be enabled on port3
Totally irrelevant to RSSO.
RSSO only needs RADIUS accounting, not device detection or Fabric services.
A Stepping Stone for Enhanced Career Opportunities
Your profile having Fortinet Certified Solution Specialist certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Fortinet FCSS_LED_AR-7.6 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Fortinet Exam FCSS_LED_AR-7.6
Achieving success in the FCSS_LED_AR-7.6 Fortinet exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in FCSS_LED_AR-7.6 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam FCSS_LED_AR-7.6!
In the backdrop of the above prep strategy for FCSS_LED_AR-7.6 Fortinet exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding FCSS_LED_AR-7.6 exam prep. Here's an overview of Certachieve's toolkit:
Fortinet FCSS_LED_AR-7.6 PDF Study Guide
This premium guide contains a number of Fortinet FCSS_LED_AR-7.6 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Fortinet FCSS_LED_AR-7.6 study guide pdf free download is also available to examine the contents and quality of the study material.
Fortinet FCSS_LED_AR-7.6 Practice Exams
Practicing the exam FCSS_LED_AR-7.6 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Fortinet FCSS_LED_AR-7.6 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Fortinet FCSS_LED_AR-7.6 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning FCSS_LED_AR-7.6 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Fortinet FCSS_LED_AR-7.6 Fortinet Certified Solution Specialist FAQ
There are only a formal set of prerequisites to take the FCSS_LED_AR-7.6 Fortinet exam. It depends of the Fortinet organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Fortinet FCSS_LED_AR-7.6 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Fortinet FCSS_LED_AR-7.6 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Fortinet FCSS_LED_AR-7.6 exam dumps to enhance your readiness for the exam.
Like any other Fortinet Certification exam, the Fortinet Certified Solution Specialist is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do FCSS_LED_AR-7.6 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The FCSS_LED_AR-7.6 Fortinet exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Fortinet FCSS_LED_AR-7.6 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Fortinet has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Fortinet changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



