The Fortinet NSE 6 - Network Security 7.6 Support Engineer (FCSS_NST_SE-7.6)
Passing Fortinet Fortinet Certified Solution Specialist exam ensures for the successful candidate a powerful array of professional and personal benefits. The first and the foremost benefit comes with a global recognition that validates your knowledge and skills, making possible your entry into any organization of your choice.
Why CertAchieve is Better than Standard FCSS_NST_SE-7.6 Dumps
In 2026, Fortinet uses variable topologies. Basic dumps will fail you.
| Quality Standard | Generic Dump Sites | CertAchieve Premium Prep |
|---|---|---|
| Technical Explanation | None (Answer Key Only) | Step-by-Step Expert Rationales |
| Syllabus Coverage | Often Outdated (v1.0) | 2026 Updated (Latest Syllabus) |
| Scenario Mastery | Blind Memorization | Conceptual Logic & Troubleshooting |
| Instructor Access | No Post-Sale Support | 24/7 Professional Help |
Success backed by proven exam prep tools
Real exam match rate reported by verified users
Consistently high performance across certifications
Efficient prep that reduces study hours significantly
Coverage of Official Fortinet FCSS_NST_SE-7.6 Exam Domains
Our curriculum is meticulously mapped to the Fortinet official blueprint.
High Availability & FGCP Diagnostics (20%)
Deep dive into cluster resilience. Master the troubleshooting of FortiGate Clustering Protocol (FGCP) in both Active-Passive and Active-Active modes. Focus on resolving split-brain scenarios, heartbeat synchronization issues, and session pick-up failures. Learn to use CLI tools to verify HA state-transition triggers and failover efficiency.
Authentication & FSSO Forensics (20%)
Focus on user-access integrity. Master the troubleshooting of Local, LDAP, and RADIUS authentication failures. Deep dive into Fortinet Single Sign-On (FSSO), focusing on collector agent connectivity, NTLM/Kerberos mismatches, and user-group mapping delays. Learn to use real-time debugs to identify credential-negotiation errors.
Routing & VPN Connectivity (20%)
Master the data plane. Focus on diagnosing OSPF and BGP adjacency issues within the enterprise core. Deep dive into IPsec VPN troubleshooting, specifically IKE Phase 1 and Phase 2 negotiations, NAT-Traversal conflicts, and DPD (Dead Peer Detection) logic. Learn to use the packet sniffer to verify encrypted traffic flows and tunnel stability.
Security Profiles & FortiGuard (15%)
Master the inspection engine. Focus on troubleshooting Web Filtering, Application Control, and IPS performance. Diagnose connectivity issues to FortiGuard servers, resolve certificate inspection mismatches (SNI vs. CN), and optimize the flow-based vs. proxy-based inspection paths to resolve latency issues for critical applications.
Fortinet FCSS_NST_SE-7.6 Exam Domains Q&A
Certified instructors verify every question for 100% accuracy, providing detailed, step-by-step explanations for each.
QUESTION DESCRIPTION:
Which Iwo troubleshooting steps should you perform lf you encounter issues with intermittent web filter behavior? (Choose two.)
Correct Answer & Rationale:
Answer: B, D
Explanation:
Intermittent behavior (working sometimes, failing others) points to resource or connectivity fluctuations rather than static misconfigurations.
B. Check that FortiGate is not entering conserve mode:
Reason: When FortiGate enters Conserve Mode (due to high memory usage), it changes its inspection behavior to save resources. Depending on the av-failopen setting, it may either bypass inspection (allowing blocked sites) or drop traffic (blocking valid sites) temporarily until memory recovers. This flapping between states causes intermittent filtering issues.
D. Check that the communication between FortiGate and FortiGuard is stable:
Reason: The Web Filter engine relies on real-time queries to the FortiGuard Distribution Network (FDN) to categorize URLs that are not in the local cache. If the internet connection or the specific path to FortiGuard is unstable (packet loss, latency), queries will time out. This results in " Rating Errors, " which can block or allow traffic unpredictably based on the " Allow websites when a rating error occurs " setting.
Why other options are incorrect:
A: A mismatch in inspection mode (e.g., Profile set to Proxy, Policy set to Flow) is a static configuration error. It would typically result in the profile not being selectable or consistently failing/not applying, rather than working intermittently.
C: If the wrong port is mapped (e.g., HTTP on 8080 is not mapped), the inspection engine will consistently ignore traffic on that port. It would not be intermittent.
QUESTION DESCRIPTION:
Refer to the exhibit, which shows a truncated output of a real-time RADIUS debug.
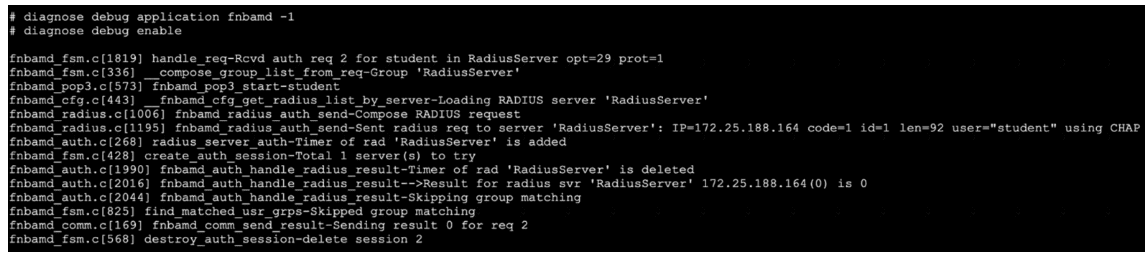
Which two statements are true? (Choose two answers)
Correct Answer & Rationale:
Answer: A, D
Explanation:
The correct answers are A and D .
The debug output shows:
Sent RADIUS req to server ' RadiusServer ' : IP=172.25.188.164 ... user= " student " using CHAP
Result for radius svr ' RadiusServer ' 172.25.188.164(0) is 0
Sending result 0 for req 2
The study guide explains that in RADIUS real-time debug, FortiGate shows the IP address of the RADIUS server it is querying. In the example, it says FortiGate “creates an access request to the RADIUS server at IP address 10.0.13.130” and shows the line Sent radius req to server ... IP=10.0.13.130
So in your exhibit, the queried server is clearly 172.25.188.164 , which makes A correct.
The study guide also states:
“The message fnbamd_comm_send_result-Sending result 0 indicates that the authentication was successful and that FortiGate received the Access-Accept message.”
Since your exhibit also ends with Sending result 0 , that makes D correct.
Why the other options are wrong:
B is wrong because result 0 means authentication successful , not failed
C is wrong because the debug explicitly shows using CHAP , and the study guide lists supported RADIUS schemes as CHAP, PAP, MS-CHAP, and MS-CHAPv2
E is wrong because the study guide says two-factor authentication would involve an Access-Challenge response: “If two-factor authentication is enabled on the server, the response is an Access-Challenge message” Your exhibit shows successful result 0 / Access-Accept , not a challenge.
So the verified answers are: A, D .
QUESTION DESCRIPTION:
In IKEv2, which exchange establishes the first CHILD_SA?
Correct Answer & Rationale:
Answer: D
Explanation:
The correct answer is D. IKE_AUTH .
The study guide explicitly states:
“IKE_Auth exchange:
• Performs the mutual authentication of two IKE endpoints.
• Configures settings like IP/mask, DNS, and so on.
• Sets up the piggyback of a child SA. Negotiates IP flow and security settings for the IPsec SA.”
It also says:
“By default, a piggyback child (IPsec) SA is negotiated along with the IKEv2 SA during IKE_AUTH. If additional IPsec SAs are needed … they are negotiated during subsequent CREATE_CHILD_SA exchanges.”
Why the other options are wrong:
A. IKE_SA_INIT is incorrect because this exchange negotiates the security settings to protect the IKE traffic, not the first CHILD_SA.
B. INFORMATIONAL is incorrect because it is used to convey control messages between IKE endpoints.
C. CREATE_CHILD_SA is incorrect for the first CHILD_SA, because it is used to create new additional child SAs or rekey existing ones after the initial exchange.
QUESTION DESCRIPTION:
Refer to the exhibit, which shows the output of diagnose sys session stat.
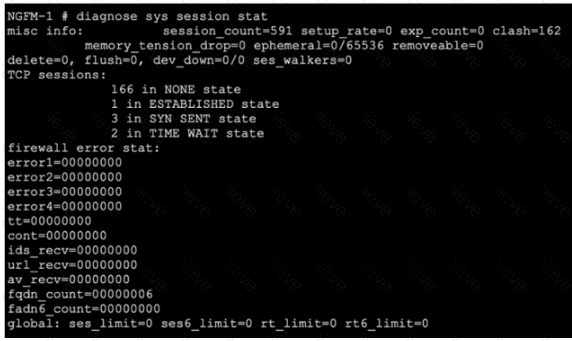
Which statement about the output shown in the exhibit is correct?
Correct Answer & Rationale:
Answer: D
Explanation:
The correct answer is D .
The exhibit shows:
session_count=591
clash=162
memory_tension_drop=0
TCP sessions:
166 in NONE state
1 in ESTABLISHED state
3 in SYN_SENT state
2 in TIME_WAIT state
The study guide explains the TCP protocol states and states explicitly:
“When a session is closed by both the sender and receiver, FortiGate keeps that session in the session table for a few seconds, to allow for any out-of-order packets that might arrive after the FIN/ACK packet. This is the state value 5.”
In diagnose sys session stat, the exhibit shows 2 in TIME_WAIT state . Since TIME_WAIT = state value 5 , those are the sessions being kept briefly for possible out-of-order packets. That makes D correct.
Why the other options are wrong:
A is wrong because session_count=591 is the total number of sessions, while the TCP sessions shown add up to only 172 (166 + 1 + 3 + 2). So not all sessions in the table are TCP sessions.
B is wrong because the study guide says the number of sessions deleted because of low free memory is shown by memory_tension_drop , and in the exhibit it is 0 , not 162.
C is wrong because the study guide defines ephemeral/open TCP sessions as those not fully established , but the exhibit does not say all 166 in NONE state are specifically “waiting to complete the three-way handshake.” The clearest directly supported statement from the displayed states is the 2 TIME_WAIT sessions retained for out-of-order packets.
So the verified answer is: D .
QUESTION DESCRIPTION:
Which statement about parallel path processing is correct (PPP)?
Correct Answer & Rationale:
Answer: A
Explanation:
Parallel Path Processing (PPP) in FortiOS refers to the system’s ability to evaluate and select among multiple processing paths—often involving dedicated network processors, content processors, or CPU-based workflows—to optimally process packets. The official documentation highlights that the PPP engine dynamically selects which hardware or software path to use for each session based on session characteristics, policy configuration, and traffic type. This dynamic selection results in optimal throughput and resource utilization.
The document specifies that PPP assesses several processing paths in parallel, using decision logic to determine whether a session should be offloaded to specialist hardware (like NP6, CP9, etc.) or stay in the CPU path, ensuring that each packet is handled by the most efficient available method under current load and policy. Hardware and software configurations both influence this outcome, but it is the PPP engine ' s decision-making that defines the optimal path per session.
QUESTION DESCRIPTION:
Refer to the exhibit.
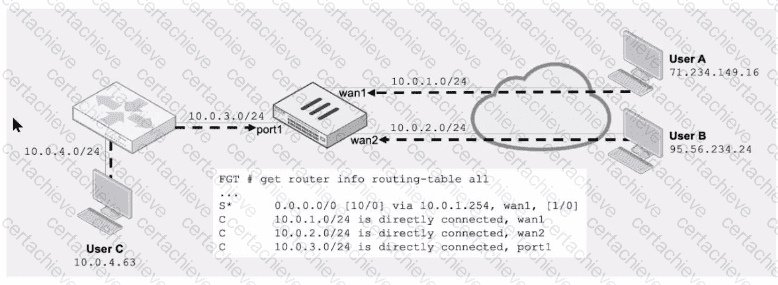
Assuming a default configuration, which three statements are true? (Choose three.)
Correct Answer & Rationale:
Answer: B, C, E
Explanation:
QUESTION DESCRIPTION:
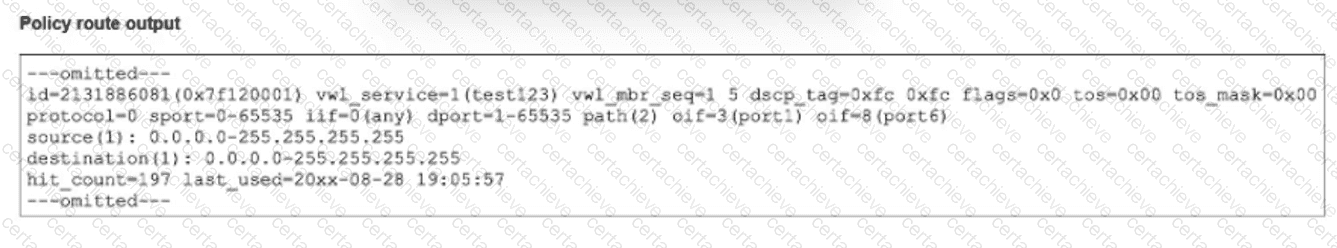
The output of a policy route table entry is shown.
Which type of policy route does the output show?
Correct Answer & Rationale:
Answer: C
Explanation:
To determine the type of policy route, we must interpret the specific flags and fields visible in the diagnose firewall proute list (or similar kernel table) output provided in the exhibit
Identify Key Indicators:
The most critical field in the output is vwl_service=1(test123).
It also lists vwl_mbr_seq=1 5.
Decode the Terminology:
vwl: This stands for Virtual WAN Link. In FortiOS, " Virtual WAN Link " is the legacy internal name for the SD-WAN feature. Even in newer firmware versions (7.x), the kernel and CLI debugs often still refer to SD-WAN objects as vwl.
vwl_service: This specifically refers to an SD-WAN Rule (also known as an SD-WAN Service). The name (test123) is the name given to that specific SD-WAN rule by the administrator.
Evaluate the Options:
A & D (Regular Policy Route): Standard policy routes (configured under config router policy) do not carry the vwl_service tag. They are typically identified by simple gateway or interface instructions without the SD-WAN service abstraction.
B (ISDB Route): While SD-WAN rules can use the Internet Service Database (ISDB) as a destination, the structure of the route entry shown here—specifically defined by a vwl_service ID—classifies it fundamentally as an SD-WAN rule, regardless of the destination object.
C (An SD-WAN rule): The presence of vwl_service and vwl_mbr_seq (SD-WAN member sequence) definitively identifies this entry as a rule generated by the SD-WAN subsystem.
Conclusion: The output shows a route controlled by the SD-WAN engine (vwl), confirming it is an SD-WAN rule.
QUESTION DESCRIPTION:
Refer to the exhibit.
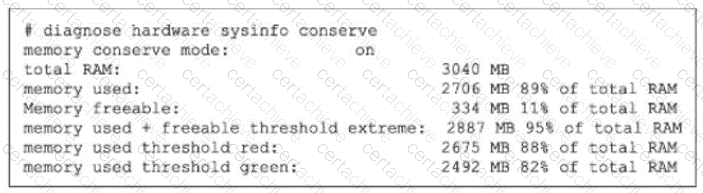
If the default settings are m place, what can you conclude about the conserve mode shown in the exhibit?
Correct Answer & Rationale:
Answer: C
Explanation:
The exhibit shows:
memory conserve mode: on
memory used: 2706 MB 89% of total RAM
memory used threshold red: 2675 MB 88% of total RAM
memory used + freeable threshold extreme: 2887 MB 95% of total RAM
The study guide states that the default thresholds are:
Extreme = 95%
Red = 88%
Green = 82%
So this FortiGate is in conserve mode because memory usage is 89% , which is above the red threshold (88%) , but it has not yet reached the extreme threshold (95%) .
The study guide then explains exactly what happens during conserve mode:
“For traffic that requires proxy-based inspection (and if memory usage has not exceeded the extreme threshold):
config system global
set av-failopen [off | pass | one-shot]
pass (default): All new sessions pass without inspection”
It also says:
“The av-failopen setting also applies to flow-based antivirus inspection.”
And the same page adds:
“If memory usage exceeds the extreme threshold, all new sessions that require inspection (flow-based or proxy-based) are blocked.”
Therefore, with default settings and with memory usage below the extreme threshold , FortiGate is allowing new sessions that require inspection, but bypassing inspection . That matches C .
Why the other options are wrong:
A is wrong because the default behavior is not to block proxy-based inspected sessions; the default is pass , meaning they pass without inspection
B is wrong because if memory rises another 6% , it reaches 95% , which is the extreme threshold . At that point, the study guide says all new sessions that require inspection are blocked
D is wrong because FortiGate blocks all new inspected sessions only when memory usage exceeds the extreme threshold , and the exhibit shows it is currently at 89% , not 95%
QUESTION DESCRIPTION:
Refer to the exhibits, which contain the partial configurations of two VPNs on FortiGate.
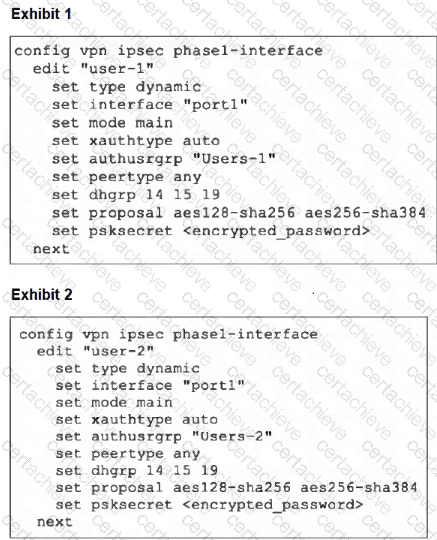
An administrator has configured two VPNs for two different user groups. Users who are in the Users-2 group are not able to connect to the VPN. After running a diagnostics command, the administrator discovers that FortiGate is not matching the user-2 VPN for members of the Users-2 group.
Which two changes must the administrator make to fix the issue? (Choose two.)
Correct Answer & Rationale:
Answer: A, D
Explanation:
The key point is that the two VPNs are dynamic dialup IPsec tunnels on the same interface and both are using IKEv1 main mode . In this design, FortiGate cannot reliably distinguish which dialup phase1 to match before phase 1 completes.
The uploaded Network Security Support Engineer 7.6 Study Guide shows that XAuth happens only after phase 1 is already established:
“The IKE real-time debug shows, after phase 1, the exchange of extended authentication (XAuth) packets… You can also see the CFG_REPLY, showing the XAuth user and group name.”
That means the user group is learned too late to be used for selecting the correct phase1 definition. So the fix must be applied to the phase1 matching method itself , not to XAuth.
The FortiOS administration guide gives the exact rule for this scenario:
“When the remote VPN peer has a dynamic IP address and is authenticated by a pre-shared key you must select Aggressive mode if there is more than one dialup phase 1 configuration for the interface IP address.”
QUESTION DESCRIPTION:
What are two reasons you might see iprope_in check () check failed, drop when using the debug How? (Choose two.)
Correct Answer & Rationale:
Answer: C, D
Explanation:
The debug flow message iprope_in_check() check failed, drop specifically indicates a failure in the Local-In Policy check. The " iprope " (IP ROouting Policy Enforcement) engine handles policy lookups. The _in_check suffix confirms that the decision is regarding traffic destined to the FortiGate itself (Local-In traffic), rather than traffic passing through it.
D. The packet was dropped because the requested service is not enabled on FortiGate:
This is the most common cause. When a packet arrives destined for the FortiGate ' s interface IP (e.g., an HTTPS or SSH request), the kernel checks if that specific service is enabled in the interface settings (set allowaccess). If the service is not enabled (e.g., trying to Ping an interface where PING access is disabled), the iprope_in_check function fails and drops the packet immediately.
C. The packet was dropped because the trusted host list is misconfigured:
Even if the service (e.g., HTTPS) is enabled on the interface, the FortiGate checks the Administrator settings. If Trusted Hosts are configured, the source IP of the incoming packet is compared against the allowed list. If the IP is not on the list, the Local-In policy check (iprope_in_check) fails, and the packet is dropped to secure the management plane.
Why other options are incorrect:
A: If traffic is dropped by a standard Firewall Policy (traffic passing through the device from one interface to another), the debug message will typically state denied by policy x or no matching policy. It would generally be a forward check (iprope_fwd_check or similar), not an _in_check.
B: If there is no route to the source, the error is a Reverse Path Forwarding (RPF) failure. The debug flow logs this explicitly as reverse path check fail, drop.
A Stepping Stone for Enhanced Career Opportunities
Your profile having Fortinet Certified Solution Specialist certification significantly enhances your credibility and marketability in all corners of the world. The best part is that your formal recognition pays you in terms of tangible career advancement. It helps you perform your desired job roles accompanied by a substantial increase in your regular income. Beyond the resume, your expertise imparts you confidence to act as a dependable professional to solve real-world business challenges.
Your success in Fortinet FCSS_NST_SE-7.6 certification exam makes your visible and relevant in the fast-evolving tech landscape. It proves a lifelong investment in your career that give you not only a competitive advantage over your non-certified peers but also makes you eligible for a further relevant exams in your domain.
What You Need to Ace Fortinet Exam FCSS_NST_SE-7.6
Achieving success in the FCSS_NST_SE-7.6 Fortinet exam requires a blending of clear understanding of all the exam topics, practical skills, and practice of the actual format. There's no room for cramming information, memorizing facts or dependence on a few significant exam topics. It means your readiness for exam needs you develop a comprehensive grasp on the syllabus that includes theoretical as well as practical command.
Here is a comprehensive strategy layout to secure peak performance in FCSS_NST_SE-7.6 certification exam:
- Develop a rock-solid theoretical clarity of the exam topics
- Begin with easier and more familiar topics of the exam syllabus
- Make sure your command on the fundamental concepts
- Focus your attention to understand why that matters
- Ensure hands-on practice as the exam tests your ability to apply knowledge
- Develop a study routine managing time because it can be a major time-sink if you are slow
- Find out a comprehensive and streamlined study resource for your help
Ensuring Outstanding Results in Exam FCSS_NST_SE-7.6!
In the backdrop of the above prep strategy for FCSS_NST_SE-7.6 Fortinet exam, your primary need is to find out a comprehensive study resource. It could otherwise be a daunting task to achieve exam success. The most important factor that must be kep in mind is make sure your reliance on a one particular resource instead of depending on multiple sources. It should be an all-inclusive resource that ensures conceptual explanations, hands-on practical exercises, and realistic assessment tools.
Certachieve: A Reliable All-inclusive Study Resource
Certachieve offers multiple study tools to do thorough and rewarding FCSS_NST_SE-7.6 exam prep. Here's an overview of Certachieve's toolkit:
Fortinet FCSS_NST_SE-7.6 PDF Study Guide
This premium guide contains a number of Fortinet FCSS_NST_SE-7.6 exam questions and answers that give you a full coverage of the exam syllabus in easy language. The information provided efficiently guides the candidate's focus to the most critical topics. The supportive explanations and examples build both the knowledge and the practical confidence of the exam candidates required to confidently pass the exam. The demo of Fortinet FCSS_NST_SE-7.6 study guide pdf free download is also available to examine the contents and quality of the study material.
Fortinet FCSS_NST_SE-7.6 Practice Exams
Practicing the exam FCSS_NST_SE-7.6 questions is one of the essential requirements of your exam preparation. To help you with this important task, Certachieve introduces Fortinet FCSS_NST_SE-7.6 Testing Engine to simulate multiple real exam-like tests. They are of enormous value for developing your grasp and understanding your strengths and weaknesses in exam preparation and make up deficiencies in time.
These comprehensive materials are engineered to streamline your preparation process, providing a direct and efficient path to mastering the exam's requirements.
Fortinet FCSS_NST_SE-7.6 exam dumps
These realistic dumps include the most significant questions that may be the part of your upcoming exam. Learning FCSS_NST_SE-7.6 exam dumps can increase not only your chances of success but can also award you an outstanding score.
Fortinet FCSS_NST_SE-7.6 Fortinet Certified Solution Specialist FAQ
There are only a formal set of prerequisites to take the FCSS_NST_SE-7.6 Fortinet exam. It depends of the Fortinet organization to introduce changes in the basic eligibility criteria to take the exam. Generally, your thorough theoretical knowledge and hands-on practice of the syllabus topics make you eligible to opt for the exam.
It requires a comprehensive study plan that includes exam preparation from an authentic, reliable and exam-oriented study resource. It should provide you Fortinet FCSS_NST_SE-7.6 exam questions focusing on mastering core topics. This resource should also have extensive hands on practice using Fortinet FCSS_NST_SE-7.6 Testing Engine.
Finally, it should also introduce you to the expected questions with the help of Fortinet FCSS_NST_SE-7.6 exam dumps to enhance your readiness for the exam.
Like any other Fortinet Certification exam, the Fortinet Certified Solution Specialist is a tough and challenging. Particularly, it's extensive syllabus makes it hard to do FCSS_NST_SE-7.6 exam prep. The actual exam requires the candidates to develop in-depth knowledge of all syllabus content along with practical knowledge. The only solution to pass the exam on first try is to make sure diligent study and lab practice prior to take the exam.
The FCSS_NST_SE-7.6 Fortinet exam usually comprises 100 to 120 questions. However, the number of questions may vary. The reason is the format of the exam that may include unscored and experimental questions sometimes. Mostly, the actual exam consists of various question formats, including multiple-choice, simulations, and drag-and-drop.
It actually depends on one's personal keenness and absorption level. However, usually people take three to six weeks to thoroughly complete the Fortinet FCSS_NST_SE-7.6 exam prep subject to their prior experience and the engagement with study. The prime factor is the observation of consistency in studies and this factor may reduce the total time duration.
Yes. Fortinet has transitioned to v1.1, which places more weight on Network Automation, Security Fundamentals, and AI integration. Our 2026 bank reflects these specific updates.
Standard dumps rely on pattern recognition. If Fortinet changes a single IP address in a topology, memorized answers fail. Our rationales teach you the logic so you can solve the problem regardless of the phrasing.
Top Exams & Certification Providers
New & Trending
- New Released Exams
- Related Exam
- Hot Vendor



